Your team just finished a network refresh. The new switches are live, VoIP is cleaner, the branch firewall rollout is done, and performance complaints have finally slowed down. Then you open the storage room and see what the project left behind: old routers, access points, handsets, patch panels, drives, and a few mystery boxes from prior upgrades that no one wants to touch.
That's usually when “telecom equipment disposal near me” becomes an urgent search, not a planned process.
For Atlanta businesses, this isn't just a housekeeping issue. It sits at the intersection of security, compliance, environmental risk, and corporate responsibility. If your company operates in healthcare, finance, logistics, professional services, education, or public sector work around metro Atlanta, old telecom gear can expose stored credentials, network maps, call records, and customer data if it leaves your facility the wrong way. It can also turn a manageable IT asset disposition project into an audit problem.
Why Smart Telecom Equipment Disposal Matters in Atlanta
Atlanta companies replace telecom equipment fast. Office expansions, cloud migrations, unified communications projects, branch consolidations, and infrastructure refreshes all create a steady stream of retired hardware. The mistake is treating that equipment like ordinary scrap.

Telecom gear is different because it often contains both recoverable materials and residual data. The environmental stakes are also larger than many teams realize. The global telecommunications equipment market contributes to a significant share of the 62 million metric tons of electronic waste produced worldwide in 2022, and only 22.3% was formally collected and recycled, according to Reworx Recycling's overview of electronics recycling. That leaves a large volume of material outside formal recovery channels.
What makes telecom gear risky
A retired phone system or networking stack can still hold useful or sensitive information after it's unplugged. Common examples include:
- Routers and firewalls holding saved credentials, VPN settings, and network configuration files
- VoIP phones retaining contact directories, extension assignments, and provisioning data
- Servers and storage arrays containing logs, recordings, backups, and user data
- Wireless controllers and switches preserving management settings and access policies
That's why a local pickup option isn't enough by itself. You need a disposal process that treats the equipment as both an environmental asset and a security liability.
Practical rule: If a device ever joined your network, assume it needs documented handling before it leaves your building.
For Atlanta firms with ESG or CSR goals, there's another angle. End-of-life telecom equipment can support a more responsible operating model when it goes through a structured reuse, donation, or materials recovery path instead of being pushed into a dumpster or handed to an unverified hauler. If your team wants a broad consumer-oriented reference on device end-of-life habits, Trade.com.au's guide on ethical phone disposal is a useful reminder that disposal choices have social and environmental consequences beyond the office.
A practical starting point for local planning is to review Atlanta-specific e-waste recycling options in Atlanta and then map your telecom assets to the right disposition path before any pickup is scheduled.
Before You Recycle Assessing Your Telecom Assets
An Atlanta office closes a floor, facilities schedules a pickup, and a few pallets of old telecom gear are staged near the dock. Then the questions start. Which devices are leased. Which still support a branch office. Which contain storage or saved configs. If your team cannot answer those before removal day, disposal becomes a control problem instead of a routine ITAD task.

A sound telecom disposition project starts with an inventory that is usable by IT, facilities, procurement, and compliance. For routers, switches, servers, handsets, PBX equipment, and related hardware, record serial numbers, model families, installed modules, storage components, and current status. “Old network gear” is not enough detail for a pickup order, a quote, or an audit file.
In Georgia, this step matters for more than internal housekeeping. Businesses often need to show consistent handling of retired assets for security review, contract compliance, and environmental reporting. If your company also tracks CSR or ESG commitments, the inventory decides what can be reused, what can be remarketed, and what should go straight to responsible recycling through a local partner that also creates community benefit.
Sort assets by disposition, not by shelf location
A practical first pass uses three categories:
Data-bearing telecom assets
Firewalls, routers, PBX appliances, voicemail systems, call recording hardware, network servers, and any unit with embedded or removable storage.Reuse or buyback candidates
Supported switches, newer VoIP phones, rack hardware, and clean working equipment with resale or redeployment value.Commodity recovery assets
Damaged, obsolete, unsupported, incomplete, or nonfunctional units that are better suited for dismantling and material recovery.
This sounds simple, but it changes the economics of the project. If everything gets treated as scrap, your company gives up resale value. If everything gets treated as remarketing stock, you create unnecessary handling cost and delay. Good assessment work keeps the security decision, the financial decision, and the recycling decision aligned.
What your inventory should actually show
Useful records include:
- Device identity, including manufacturer, model, serial number, and asset tag
- Business ownership, such as department, site, cost center, or assigned administrator
- Physical location, including branch, MDF or IDF closet, rack position, storage room, or offsite holding area
- Condition, such as working pull, failed unit, incomplete chassis, cracked handset, or missing power supply
- Data profile, including flash memory, SSD, HDD, SIM, removable media, or retained configuration capability
- Planned disposition, such as redeploy, remarket, sanitize and resell, media destroy, or recycle
That record becomes the backbone of chain-of-custody control. It also gives your recycler or ITAD partner enough detail to scope labor, pickup requirements, and downstream processing without guessing.
A good inventory proves that each retired asset had a known owner, a reviewed condition, and an approved exit path.
Check for hidden value and hidden risk
Telecom assessments often miss two things at the same time. The first is residual value in newer phones, switching gear, optics, and accessories. The second is stored data in devices that do not look like traditional storage assets.
That trade-off matters. A business phone system refresh can include gear that still has secondary market value, while an older appliance with little resale potential may still require careful handling because it retains credentials, logs, or provisioning information. Atlanta organizations with CSR targets should care about both outcomes. Reuse extends asset life. Responsible recycling keeps material out of landfill. Working with a local social enterprise such as Reworx can support both goals while also producing measurable community impact through job creation and workforce development.
For teams tightening their process before scheduling removal, this guide to IT inventory audits before recycling gives a practical framework for getting IT, facilities, compliance, and procurement aligned.
Pre-pickup review points
| Item | Why it matters |
|---|---|
| Asset list complete | Prevents unreviewed telecom gear from leaving the site |
| Leased or vendor-owned equipment identified | Avoids disposing of property your company does not own |
| Data-bearing devices flagged | Separates sanitization work from standard recycling |
| Reuse and buyback candidates marked | Preserves recoverable value and supports CSR reporting |
| Access and labor scope defined | Reduces disputes about stairs, racks, palletizing, and pickup time |
| Internal approvals documented | Gives IT, compliance, and facilities a clear record of the decision |
Teams that do this work up front usually get a cleaner quote, fewer surprises on pickup day, and better reporting after the job is done. That is the difference between a rushed cleanout and a telecom disposal process your Atlanta business can defend to auditors, leadership, and the community.
Ensuring Total Data Destruction for Telecom Hardware
An Atlanta IT manager decommissions a phone system after a migration, clears the admin interface, and schedules pickup. Weeks later, legal asks for proof that voicemail archives, call logs, credentials, and stored configs were destroyed. A factory reset does not answer that question.
For telecom hardware, data destruction has to match the media, the business risk, and the intended disposition of the asset. Security teams care about irrecoverability. Compliance teams care about documentation. Finance may still care about resale value if the hardware can be reused. Good ITAD planning balances all three.
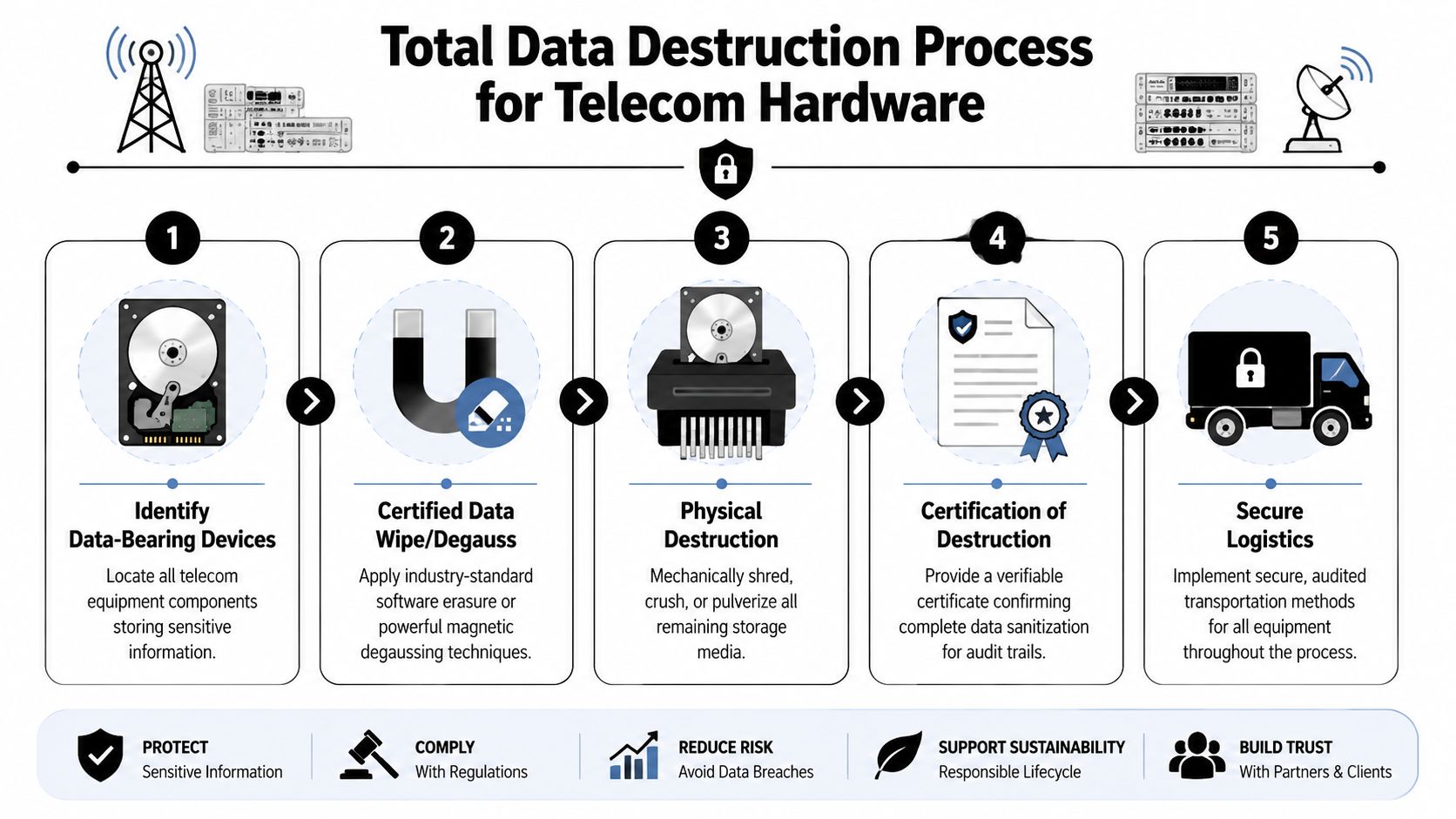
The standard I recommend is simple. Use a documented sanitization process aligned to NIST 800-88, then keep the custody and destruction records with the rest of the project file. That matters in Georgia businesses handling patient data, financial records, internal recordings, customer contact details, or network credentials. It also matters for CSR reporting, because reuse only counts as a responsible outcome if the data-bearing components were handled correctly first.
Match the destruction method to the asset
A single method for every device usually creates unnecessary cost or unnecessary risk.
Software wiping
Software wiping fits assets that still work and may be redeployed, resold, or refurbished. That often includes newer servers, some UC appliances, and telecom gear with standard removable drives.
It preserves downstream value. It also requires verification. If the drive is damaged, locked, inaccessible, or the device has a high-risk data profile, wiping is the wrong call.
Degaussing
Degaussing applies to magnetic media only. It is useful when reuse is off the table and the goal is to render the media unreadable before final processing.
That does not help with solid-state media or flash storage. Many teams miss that distinction.
Physical destruction
Physical shredding or crushing is usually the cleanest option for failed drives, unknown media, highly sensitive environments, and equipment with no resale path. If exposure risk is higher than the value of the hardware, destroy the media and document it.
That trade-off comes up often in healthcare, finance, legal, and public sector work around Atlanta.
Telecom assets that often get missed
The risk is rarely limited to the obvious storage array in the server room. In telecom projects, the overlooked items are often the ones that create problems later.
Pay close attention to:
- Call recording systems that retain audio files, timestamps, and user metadata
- PBX and VoIP management servers with provisioning records, extensions, and routing details
- Firewalls, session border controllers, and SD-WAN appliances that store certificates, VPN settings, and credentials
- Unified communications platforms with user profiles, logs, and message data
- Backup media tied to telecom infrastructure, especially if it was kept outside the main data center process
Documentation is part of the destruction process
A secure outcome is not complete until your team can prove what happened. That means records that hold up under internal audit, customer review, or legal inquiry.
The file should typically include:
- Chain-of-custody documentation from pickup through final processing
- Certificates of destruction mapped to the relevant asset batch or serial range
- Method details showing whether media was wiped, degaussed, or physically destroyed
- Exception records for damaged, inaccessible, or unidentified devices
Without that paperwork, your team is left relying on vendor assurances. That is weak control.
What the method choice looks like in practice
| Approach | Best fit | Common problem |
|---|---|---|
| Factory reset | Internal reconfiguration of some devices | Does not prove secure disposal |
| Software wipe | Functional assets headed for reuse or resale | Fails if media is damaged or high risk |
| Degaussing | Magnetic media with no reuse value | Not suitable for flash or SSD storage |
| Physical shredding | High-risk or failed media | Eliminates resale value tied to the drive |
For Atlanta companies trying to meet both compliance obligations and CSR goals, the strongest approach is to separate reusable equipment from media that needs destruction, then work with a local provider that can issue defensible records. Using documented data destruction services in Atlanta for businesses helps protect the business, supports responsible reuse where appropriate, and keeps a clean audit trail if leadership, regulators, or customers ask questions later.
Vetting Certified Telecom Recyclers in the Atlanta Area
The local market includes everyone from junk haulers to specialized ITAD firms. They may all claim to recycle electronics. That doesn't mean they provide the same level of control.

The difference shows up in documentation, downstream handling, and whether they can answer specific questions without hand-waving. According to SAMR's telecom recycling guide, 20% of e-waste handled by unverified recyclers is exported to unregulated markets. The same source states that R2-certified facilities can achieve up to 97% diversion from landfills and provide EPA-compliant certificates used in HIPAA or GDPR audit contexts.
Scrap hauler versus ITAD partner
A simple comparison makes the trade-off clear:
| Vendor type | Typical strength | Common weakness |
|---|---|---|
| General junk or scrap hauler | Fast removal from the site | Limited data controls and weak audit trail |
| Uncertified electronics collector | May accept mixed loads | Unclear downstream processing |
| Certified ITAD recycler | Chain of custody, destruction records, compliant handling | Requires more structured intake from your team |
That extra structure is usually worth it. For telecom gear, the service isn't just “take this stuff away.” It's “take this exact asset set, process it under documented controls, and give me records I can defend.”
Questions worth asking every vendor
Don't ask broad questions like “Do you recycle responsibly?” Ask operational questions that force specific answers.
- What certifications do you hold now? Ask for the exact certifications relevant to data security and electronics processing.
- How do you maintain chain of custody? You want to hear how assets are tracked from pickup through destruction or recovery.
- What happens downstream? If they can't explain where materials go after initial processing, that's a problem.
- Do you issue certificates of destruction and recycling? If yes, ask what details those documents include.
- How do you handle mixed loads? Telecom projects often include batteries, drives, cables, rack gear, and general IT equipment in one pickup.
- What's your exception process? Damaged drives, unlabeled gear, and incomplete equipment should not derail the whole job.
Unclear downstream answers are usually a sign that the vendor is selling convenience, not control.
Certifications matter because they change behavior
Certified providers separate themselves through these specific qualifications. Standards such as R2v3 and NAID AAA matter because they require repeatable handling practices, documented controls, and accountability beyond a verbal promise.
In the Atlanta market, one option businesses often evaluate is Reworx Recycling, which provides electronics recycling, secure data destruction, and ITAD-related services from the Smyrna area. If you're comparing providers, their guide on selecting a reliable e-waste recycling partner is a practical framework for vendor screening.
Red flags that should slow the project down
A vendor might still be wrong for your business even if the pickup sounds easy.
Watch for these signs:
- No written process for data-bearing equipment
- No certificate language in the proposal
- No discussion of downstream vendors
- No distinction between reuse, destruction, and commodity recovery
- No questions about your asset inventory or data risk
When your team searches telecom equipment disposal near me, speed is usually what gets advertised. Control is what protects the business.
Understanding Disposal Costs Buybacks and Regulations
A lot of companies still search for “free recycling” as if it's a standard commercial model. Sometimes pickup can be included. Sometimes processing costs can be offset. But responsible telecom disposal is rarely as simple as “everything is free.”
The pricing gap usually comes from labor, logistics, secure handling, and the condition of the equipment.
A 2025 EPA-referenced discussion cited by Techbros notes that 65% of U.S. businesses encounter unexpected charges in ITAD contracts, and telecom equipment recycling costs average $0.20 to $0.50 per pound. That's why IT managers should push for transparent scopes, especially when the load includes network gear, rack hardware, batteries, drives, and mixed office equipment.
Where hidden fees show up
The most common surprise charges aren't mysterious. They usually come from work that wasn't defined clearly at the start:
- Access and labor for equipment in closets, data rooms, or multiple floors
- Sorting mixed loads that combine telecom hardware with unrelated junk
- Data destruction services for drives or embedded storage
- Hazardous components that need separate handling
- Custom logistics for after-hours, multi-site, or tightly controlled pickups
That doesn't mean the quote is unfair. It means your team needs line-of-sight into what is and isn't included.
Buyback changes the economics
Smart planning helps in these cases. Not every retired asset is a disposal cost. Some functional telecom equipment may still hold residual value, particularly if it's newer, complete, and in demand.
A realistic decision framework looks like this:
| Asset condition | Better path |
|---|---|
| Functional and supportable | Evaluate for buyback or remarketing |
| Functional but sensitive | Sanitize first, then assess value |
| Obsolete or damaged | Recycle for material recovery |
| Unknown status | Quarantine and review before pickup |
For Atlanta businesses, buyback matters because it reframes the project. Instead of seeing ITAD as pure expense, you can treat it as a mix of cost control, risk reduction, and value recovery.
Compliance affects the price and the process
Telecom disposal is also shaped by regulation. The exact rules depend on your industry and data environment, but the recurring themes are straightforward: handle hazardous materials correctly, document where assets go, and make sure data destruction is auditable.
For broader federal guidance, the EPA's electronics donation and recycling resources are worth bookmarking.
The practical point for Georgia businesses is this: compliance isn't only about avoiding penalties. It affects vendor selection, pickup procedures, internal approvals, and the records your company needs to keep after the load leaves the site.
The cheapest quote often assumes the least responsibility. That's why it looks cheap.
If your organization is managing a network refresh, office cleanout, facility cleanout, or partial data center decommissioning, ask vendors to separate transportation, data destruction, recycling, and buyback into clear line items. That makes bids easier to compare and prevents the “free pickup” conversation from turning into a disputed invoice later.
Partner with Reworx for Responsible Atlanta ITAD
Atlanta businesses don't need another vendor that hauls away old hardware. They need a process that stands up to security review, supports environmental goals, and makes sense for operations teams that are already juggling projects, deadlines, and space constraints.
That's why telecom disposal should be treated as a business decision, not a cleanup task. The strongest programs align four things at once: asset visibility, secure data handling, documented downstream processing, and a clear path for reuse or material recovery.
For companies trying to connect compliance with CSR, a social enterprise model adds something standard scrap vendors usually don't. Donation-based recycling can turn retired equipment into broader community benefit when assets are suitable for reuse or value recovery supports digital inclusion and workforce efforts. That matters to sustainability leaders, procurement teams, and executives who want disposal choices to reflect company values.
Why the local angle matters
Working with an Atlanta-area partner simplifies coordination. Site access, pickup scheduling, chain of custody, and facility communication are easier when the provider understands metro Atlanta operations and can support office moves, branch refreshes, and end-of-year cleanouts without creating extra friction.
If your project also includes non-electronic assets, it helps to coordinate disposal streams instead of treating everything as one pile. For example, facilities teams planning a broader office reset may also want to review responsible furniture removal for offices so electronics, furnishings, and fixtures each go through the right channel.
A local starting point for business recycling support is Reworx Recycling's Atlanta service coverage. For companies evaluating office cleanouts, secure data destruction, computer recycling, laptop disposal, product destruction, or larger IT asset disposition projects, that gives your team a practical way to scope the work before it turns into another storage-room problem.
The better outcome is simple. Old telecom equipment leaves your site with documentation, data risk is closed out, useful assets are evaluated intelligently, and your company can support sustainable recycling without treating everything as waste.
If your business is searching for a practical next step, explore Reworx Recycling to plan telecom equipment disposal, secure data destruction, an office or facility cleanout, or a corporate donation program that supports responsible recycling in the Atlanta area.