Staring at a pile of old computers and hard drives? Each one is a potential landmine, holding sensitive customer data, financial records, and proprietary secrets. For business owners, IT managers, and sustainability leaders in Atlanta, secure data destruction services aren't just an IT chore—they're a core business strategy that turns that risk into a certified, secure, and compliant process for permanent data elimination.
Why Data Destruction Is a Critical Business Strategy
Picture a mid-sized healthcare practice in Buckhead upgrading its server room. The old equipment, packed with years of protected health information, gets shoved in a closet for "later." Months go by, and a cleaning crew, clueless about the data risk, sends the old servers to a general recycler. Before you know it, those hard drives are on a secondary market, and a massive data breach is unfolding.
This isn't some far-fetched horror story; it's a preventable nightmare that proves a critical truth: old tech is never truly harmless.
The Real Risks of Improper Disposal
Failing to properly destroy data on retired assets opens your organization up to some serious consequences that go way beyond a simple IT headache. The fallout can hit every corner of your business, from finance to public relations.
- Massive Regulatory Fines: Getting on the wrong side of regulations like HIPAA, GDPR, and other industry mandates can lead to seven-figure penalties.
- Irreversible Reputational Damage: A single data breach can shatter customer trust that took you years to build. Winning it back is a slow, expensive grind.
- Competitive Disadvantage: Imagine your trade secrets, R&D data, or client lists falling into a competitor's hands. The damage could be irreversible.
- Legal Liability: You have a legal duty to protect confidential information. A failure here can trigger costly lawsuits from customers, partners, and anyone else affected.
The market is waking up to this reality. The global secure data destruction market was valued at $3.35 billion in 2024 and is expected to hit $5.64 billion by 2029. What's driving this? A surge in regulations demanding irreversible data destruction to prevent breaches, which cost businesses an average of $4.45 million in 2023.
From Liability to Opportunity
This is where a strategic partner like Reworx Recycling steps in, turning a potential crisis into a secure and socially responsible solution. We provide certified secure data destruction services that completely eliminate any chance of data recovery. It’s a key piece of any comprehensive data security management strategy.
When you partner with us for your IT equipment disposal, you not only get a Certificate of Destruction as auditable proof of compliance but also contribute to something bigger. As a donation-based social enterprise, we ensure your old equipment, once a liability, helps support community initiatives and environmental sustainability. For a deeper dive, check out our guide on how data destruction protects businesses.
Ultimately, professional data disposal isn't an expense. It’s an investment in your company's security, reputation, and future.
Breaking Down the Core Methods of Data Destruction
Making data truly disappear requires more than just dragging a file to the trash bin. Real secure data destruction services rely on proven, verifiable methods to make sure sensitive information is gone for good. Think of it like a sensitive paper document—you wouldn't just toss it in the recycling; you'd run it through a cross-cut shredder. The same principle applies to your digital files, but the tools are far more powerful.
When it's time to retire old IT assets, understanding the different destruction methods is key. IT managers and business owners need to make informed choices that line up with their security policies and compliance requirements. Each technique offers a different level of security for specific situations, from software solutions that allow for device reuse to total physical obliteration for maximum protection.
Physical Shredding: The Gold Standard
Picture an industrial-strength machine that doesn't just chew through paper, but devours metal, plastic, and silicon. That's the essence of physical hard drive shredding. This method uses powerful equipment to grind hard drives, solid-state drives (SSDs), and other storage media into tiny, mangled fragments.
Once a drive goes through a shredder, the data is permanently and irretrievably destroyed. There's simply no way to piece the fragments back together to recover information. This makes physical shredding the most secure method out there—it's the top choice for organizations dealing with highly sensitive data, like financial institutions, healthcare providers, and government agencies.
At Reworx Recycling, we specialize in physical shredding because it provides absolute peace of mind. It’s the definitive way to eliminate any chance of data recovery, making it a cornerstone of our secure data destruction services.
Degaussing: Wiping with Magnets
Another powerful method, particularly for traditional hard disk drives (HDDs), is degaussing. Think of it like using a massive magnet to completely scramble the magnetic field on a drive's platters, where the data is stored. It's the modern equivalent of how a strong magnet could wipe an old cassette tape clean.
Degaussing instantly and permanently erases all data by neutralizing the magnetic domains on the storage media. The process is quick and highly effective for HDDs, but it’s completely useless on modern solid-state drives (SSDs), which don’t store data magnetically.
Failing to use professional methods like these can lead to serious consequences—fines, breaches, and a permanent loss of customer trust. The image below drives home just how damaging a single data disposal oversight can be.
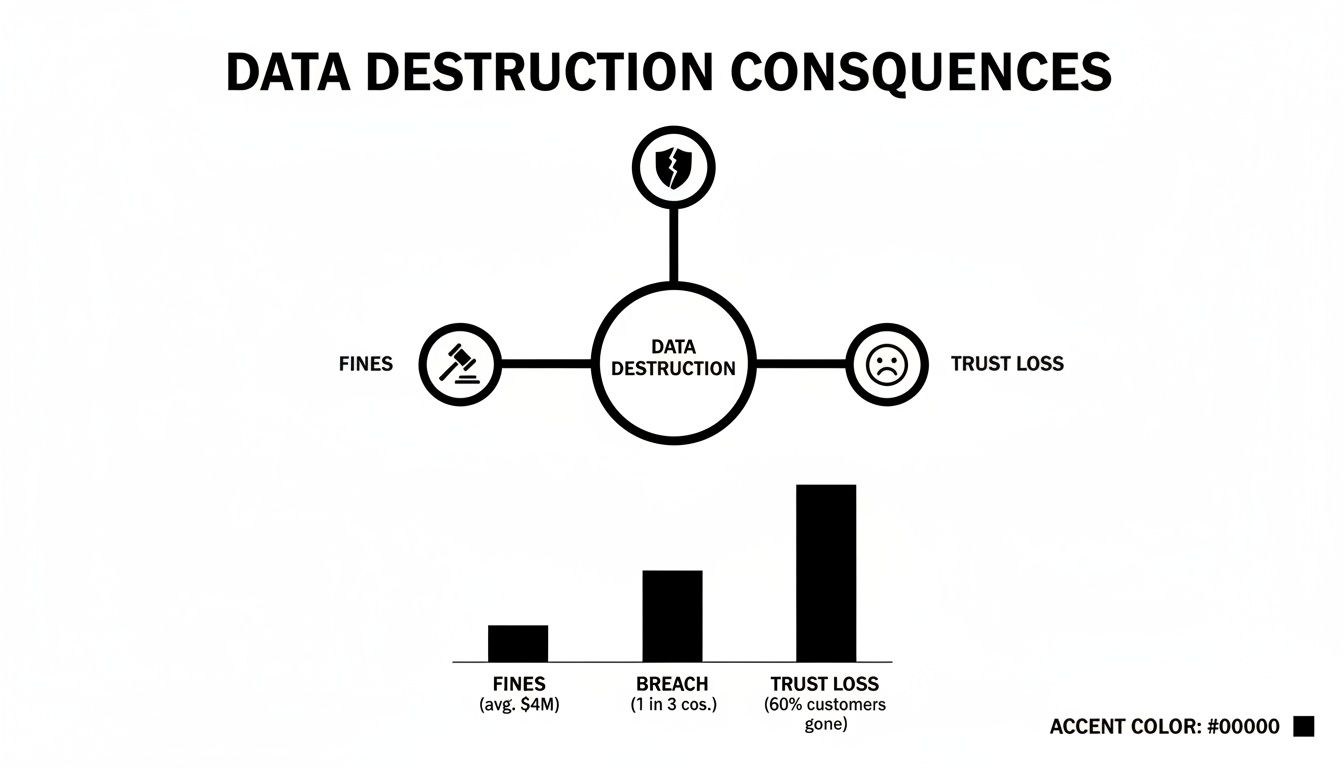
This visual is a stark reminder of why certified, professional data destruction isn't just a good practice—it's a critical business safeguard.
Software Wiping and Cryptographic Erasure
Not every situation calls for turning a hard drive into confetti, especially if a device is destined for refurbishment or resale. In these cases, software-based methods are the way to go.
Software Wiping: This technique uses specialized software to overwrite every single sector of a hard drive with random data, often multiple times. It’s like meticulously writing gibberish over a sensitive document until the original text is completely obscured. When done correctly to a standard like NIST 800-88, this ensures the original data can't be recovered, even with advanced forensic tools.
Cryptographic Erasure: This is a modern and elegant solution for self-encrypting drives (SEDs). Think of it like locking your data in a digital vault and then vaporizing the only key. The process works by instantly erasing the media encryption key, which renders all the encrypted data on the drive permanently unreadable.
Comparison of Data Destruction Methods
With several options available, choosing the right one comes down to your specific needs for security, compliance, and asset value recovery. This table offers a quick comparison to help you decide.
| Destruction Method | How It Works | Data Recovery Potential | Device Reusability | Best For |
|---|---|---|---|---|
| Physical Shredding | Machinery grinds the device into small, unrecognizable pieces. | None. Irretrievable. | None. Device is destroyed. | Maximum security needs; sensitive data (HIPAA, financial); end-of-life media. |
| Degaussing | A powerful magnetic field scrambles and erases the data on magnetic media like HDDs. | None. Irretrievable. | None. Device is rendered unusable. | Rapid, secure erasure of magnetic hard drives and tapes. Not for SSDs. |
| Software Wiping | Specialized software overwrites existing data with random characters, often in multiple passes. | Very Low to None. | High. Device can be reused or resold. | Preparing devices for reuse, donation, or resale while ensuring data is unrecoverable. |
| Cryptographic Erasure | The encryption key for a self-encrypting drive (SED) is erased, making the encrypted data inaccessible. | None. Irretrievable. | High. Device can be reused or resold. | Instant, secure erasure of self-encrypting drives (SEDs), common in enterprise environments. |
Each method has its place. The key is to match the technique to the data's sensitivity and the device's future.
The demand for these services is skyrocketing. Projections show the hard drive destruction market expanding from $1.65 billion in 2024 to $5.05 billion by 2035. A major trend is the shift to on-site services, which are expected to hold a 64% market share by 2035 as 70% of organizations prefer to witness the destruction process firsthand for verification.
Choosing the right approach depends on your end goal—are you reusing the asset, or do you need to ensure total data elimination? For a deeper dive into building a bulletproof plan, check out our guide on strategies for hard drive destruction. Ultimately, partnering with a certified expert is the only way to guarantee the job is done right, protecting your business from the massive risks of a data breach.
Navigating the Complex World of Data Compliance
For any modern business, compliance is a lot more than just an IT checklist item—it’s a legal shield protecting you from crippling fines and a damaged reputation. Failing to follow data protection rules isn't a small mistake; it's a massive business risk. When you retire IT assets, the data on them is still covered by a tangled web of laws, and regulators don't care if a device is in your server room or a forgotten closet.
This legal landscape can feel overwhelming, but the core ideas are pretty simple. Every regulation, whether it's for a specific industry or an international law, is designed to protect sensitive information. Your job is to prove you took every step necessary to permanently destroy that information when you didn't need it anymore. This is exactly where professional secure data destruction services become a non-negotiable part of your compliance plan.
Understanding Key Data Protection Regulations
While there are dozens of regulations out there, a few major ones set the tone for data security across most industries. These aren't just acronyms; they are powerful legal frameworks with very real consequences.
NIST 800-88: Officially titled "Guidelines for Media Sanitization," this is the gold standard from the National Institute of Standards and Technology. It gives a detailed roadmap for erasing data, setting clear rules for methods like software wiping ("Clear" and "Purge") and physical destruction ("Destroy"). Following NIST 800-88 is widely seen as the best practice for showing you’ve done your due diligence.
HIPAA: The Health Insurance Portability and Accountability Act lays down strict rules for protecting patient information. For any healthcare provider, from a big hospital to a small clinic, this applies to old medical devices, laptops, and servers. A breach from improperly disposed of equipment can lead to fines in the millions and serious legal trouble.
GDPR: Even if your business is based in the U.S., the General Data Protection Regulation might apply to you. Understanding international laws, such as GDPR regulations, is critical for businesses that handle the data of European Union citizens to avoid penalties and keep global trust.
These regulations don't just ask you to delete files; they demand a verifiable process that makes sure data is gone for good.
The Certificate of Destruction: Your Compliance Armor
So, how do you prove to an auditor or a court that you responsibly destroyed sensitive data? The answer is a Certificate of Destruction. This formal document is your official, legally defensible record that your data-bearing assets were properly destroyed.
A Certificate of Destruction serves as an auditable receipt, detailing what was destroyed, when it was destroyed, how it was destroyed, and the serial numbers of the specific assets. Without this document, you have no tangible proof of compliance.
This certificate turns data destruction from a forgotten task into a recorded, verifiable business process. It’s the final link in your chain of custody, giving you the peace of mind that comes from knowing you’ve met your legal obligations. Partnering with a certified vendor like Reworx Recycling ensures you get this crucial paperwork for every single asset we handle.
Reworx Recycling: Your Compliance Ally
Navigating this regulatory environment requires a partner who gets what’s at stake. At Reworx Recycling, our processes are built around the highest standards of security and compliance. We don't just recycle your electronics; we provide certified secure data destruction services that line up with legal requirements and industry best practices.
By issuing a formal Certificate of Destruction, we give your organization the auditable proof it needs to satisfy legal scrutiny and show you’re a responsible steward of sensitive information. To get a better handle on the certifications that back up these processes, you can learn more about NAID AAA Certification and why it matters for your business's security. This commitment gives risk-averse decision-makers the confidence that their data, reputation, and bottom line are all protected.
Choosing Your Service: On-Site vs. Off-Site Destruction
When it comes to secure data destruction services, one of the first big decisions you'll face is a logistical one: should the destruction happen right here at your office, or should your old equipment be taken to a secure facility? This choice between on-site and off-site services really comes down to what your organization needs most—be it security, convenience, cost savings, or the ability to witness the process yourself.
Both methods, when handled by a certified pro like Reworx Recycling, will completely and permanently wipe out your data. The real difference is where it happens and how much direct oversight you have. Let's break down the details of each so you can figure out what works best for your workflow and compliance needs.

The Case for On-Site Destruction
On-site destruction brings the whole operation straight to your doorstep. A specialized mobile shredding truck, basically a destruction facility on wheels, pulls up to your location. Your IT assets are gathered, their serial numbers are scanned for the record, and you can personally watch every single hard drive, SSD, or backup tape get pulverized into tiny fragments.
This method offers the ultimate transparency and peace of mind. For businesses in tightly regulated fields like healthcare or finance, being able to see the destruction from start to finish provides a layer of security assurance that’s hard to beat.
On-site destruction completely eliminates any chain of custody risks that come with transporting data-bearing assets. Your sensitive information never leaves your property intact, giving you immediate, verifiable proof that it's gone for good.
There's a reason this approach is gaining so much traction. North America currently holds a commanding 38% share of the global data destruction market, and on-site destruction is projected to capture 64% of that market by 2035. This shift is all about the growing demand for verifiable, real-time privacy. In fact, outsourcing to certified shredders can slash data breach risks from disposed assets by a staggering 99% compared to just trying to wipe them in-house. You can explore the full market analysis on data destruction trends to see why witnessed destruction is becoming the new standard.
Understanding Off-Site Destruction
Off-site destruction is a more streamlined and often more budget-friendly option, especially when you’re dealing with a large volume of old IT equipment. With this service, a secure, GPS-tracked vehicle comes to you. Your assets are immediately placed into locked, tamper-evident containers before they’re even loaded onto the truck.
A strict chain of custody is maintained from the second your assets leave your building until they reach a secure, access-controlled destruction plant. Once there, the devices are destroyed under constant video surveillance. You'll still receive a Certificate of Destruction, which provides the same level of certified proof you'd get with on-site services.
Making the Right Choice for Your Business
So, which one is right for you? Your decision will likely come down to a few key factors.
- Security Requirements: If your company policy or regulatory mandates (like HIPAA or DoD) require witnessed destruction, then on-site is the only way to go.
- Logistical Convenience: Off-site is typically quicker and less disruptive to your day-to-day operations. There’s no need to set aside space or have your staff oversee the process.
- Volume and Cost: If you have a massive amount of devices to get rid of, off-site destruction is usually more economical because of the efficiencies of scale at a dedicated facility.
- Peace of Mind: For many business leaders, nothing beats the absolute certainty of watching their data get physically destroyed with their own eyes.
Reworx Recycling offers both on-site and off-site secure data destruction services, so we can tailor a solution to your specific security protocols, budget, and logistical needs. Whether you need the instant verification of mobile shredding or the efficiency of a secure, plant-based process, we have a compliant, certified solution. To see our mobile shredding in action, you can find more details on our on-site hard drive destruction services.
How to Choose the Right Data Destruction Vendor
Picking a partner for your secure data destruction services is one of the most critical decisions you’ll make in your entire IT asset disposition (ITAD) plan. Let's be frank: not all vendors are created equal. The fallout from a bad choice—think massive data breaches or costly compliance failures—can be devastating.
You have to vet potential partners with a critical eye, and that means asking the right questions to tell the certified pros from the risky operators. This guide is your framework for due diligence, making sure your data, your reputation, and your legal standing are all buttoned up.
Start with Security and Certifications
Before you even get to a conversation about price, you need to verify a vendor's credentials. Industry certifications aren't just fancy logos they stick on a website; they are hard-earned, third-party proof that a company lives and breathes the strictest standards for security, employee screening, and operational integrity.
NAID AAA Certification: This is the gold standard, the absolute non-negotiable benchmark for data destruction. The National Association for Information Destruction (NAID) performs surprise audits to verify everything from secure destruction processes and employee background checks to facility security. A NAID AAA certified vendor gives you a guarantee that your data is handled securely from the moment it leaves your hands.
R2 Certification: The Responsible Recycling (R2) standard is all about environmental responsibility and worker safety. An R2 certified partner, like Reworx Recycling, ensures that any materials left over after destruction are recycled in an environmentally sound way. It's how you prevent toxic e-waste from ever seeing a landfill.
Don't be shy. Ask potential vendors to show you proof of these certifications. If they hesitate or can't produce them, that’s a giant red flag.
Demand a Documented Chain of Custody
A secure process is a documented one. Period. Your vendor must be able to show you an unbroken, verifiable chain of custody from the second your assets leave your facility until the moment they are destroyed. In an audit, this documentation is your first and best line of defense.
A documented chain of custody is your auditable proof of due diligence. It should detail every single touchpoint—who handled the assets, where they were stored, and when they were destroyed, all verified with meticulous serial number tracking.
Here’s what you need to ask:
- How do you document the chain of custody? Look for detailed reports that track individual serial numbers, dates, times, and the personnel involved at every step.
- What security is in place during transport? The only acceptable answer involves locked, GPS-tracked vehicles and tamper-evident containers.
- What's your facility like? It should have restricted access, 24/7 surveillance, and ironclad operational protocols.
Check for Liability and Insurance Coverage
Even the tightest processes need a financial safety net. A professional data destruction partner will carry enough liability insurance to protect your business in the unlikely event that something goes wrong.
Ask for a copy of their Certificate of Insurance. The key thing you're looking for is downstream data liability insurance. This specific coverage protects you from breaches that could happen after the assets are no longer in your control. A vendor without it is essentially asking you to shoulder all the risk. A transparent, trustworthy partner will have this ready for you.
Scrutinize Employee Screening and Training
The people physically handling your sensitive data are the most critical link in the security chain. Your vendor absolutely must have rigorous employee screening and training protocols to minimize the risk of insider threats.
- Background Checks: Every single employee with access to your media must undergo a comprehensive criminal background check. No exceptions.
- Drug Screening: Regular drug screening should be a standard part of their employment policy.
- Security Training: Staff need to be trained regularly on data security protocols, the latest compliance requirements, and chain-of-custody procedures.
At Reworx Recycling, we don't compromise on these standards. Every member of our team is trained and vetted to be a guardian of your information.
Data Destruction Vendor Vetting Checklist
To tie it all together, here’s an actionable checklist to help you systematically evaluate potential partners. Use it to guide your conversations and ensure you cover all the critical bases before making a final decision.
| Evaluation Criterion | Why It Matters | Questions to Ask |
|---|---|---|
| Certifications | Third-party validation of security, environmental, and safety standards. | "Can you provide current copies of your NAID AAA and R2 certifications?" |
| Chain of Custody | Provides an auditable trail, proving due diligence and secure handling. | "What does your chain-of-custody documentation look like? Can we see a sample report?" |
| On-Site vs. Off-Site Options | Flexibility to meet your specific security requirements and witness destruction. | "Do you offer on-site shredding services? What are the security protocols for off-site transport?" |
| Liability Insurance | Financial protection against data breaches that occur after assets leave your control. | "Please provide your Certificate of Insurance. Does it include downstream data liability coverage?" |
| Employee Vetting | Minimizes insider threats by ensuring trustworthy personnel handle your assets. | "What is your policy on employee background checks, drug screening, and ongoing security training?" |
| Reporting & Certificates | Formal proof of destruction for compliance and internal records. | "What kind of Certificate of Destruction do you provide? Does it include serialized reporting?" |
| Environmental Compliance | Ensures e-waste is handled responsibly, avoiding legal and reputational risk. | "How do you manage the electronic waste after the data-bearing components are destroyed?" |
Choosing the right vendor is about finding a true partner in security and compliance. This checklist will help you identify the ones who are genuinely committed to protecting your business.
For a broader view on finding the right partner for your overall ITAD needs, you might find our guide on selecting the best IT asset disposition companies helpful. By being thorough and asking the right questions, you can confidently choose a partner who not only destroys your data but defends your business.
Partnering with Reworx for Security and Social Impact
Choosing a partner for secure data destruction services is about more than just checking off a risk management box. It's a decision that says something about your company's values. After digging into the different methods, compliance needs, and how to vet a provider, the last step is finding one who doesn’t just protect your business—they also align with your commitment to doing good. This is where top-tier security and real social impact meet.
At Reworx Recycling, we are a social enterprise that offers a unique approach, turning a critical business task into a genuine force for good. When you work with us, you aren't just getting compliance paperwork. You're plugging into a model that directly benefits your organization and the community around you.

More Than a Certificate of Destruction
Any partnership with Reworx is designed to be more than a simple transaction. The Certificate of Destruction we issue is your rock-solid guarantee of absolute data security and regulatory compliance. But the real value is in the story that certificate tells—a story of environmental care and community support.
By choosing Reworx, you ensure that your retired IT assets are handled with the highest security standards while simultaneously fueling a mission of digital inclusion, workforce development, and sustainable electronics recycling. It’s a dual return on your ITAD investment.
Your decision to recycle responsibly with us creates a ripple effect. Good, working equipment gets a second life, refurbished and donated to support local initiatives. Electronics that are truly at their end are processed in an environmentally sound way, keeping hazardous e-waste out of landfills for good. Suddenly, your end-of-life IT equipment shifts from a potential liability into a valuable community asset.
Your Next Steps Toward Secure and Responsible ITAD
Making a positive impact while protecting your data is easier than you think. We’ve built our process to be simple, secure, and perfectly suited to your organization's needs. Here’s how to get started:
- Schedule a Pickup: Our team comes straight to your facility to securely collect your outdated IT assets, ensuring a documented chain of custody right from the start.
- Request a Quote: Get a clear, no-nonsense proposal for our secure data destruction services, whether you need on-site shredding or efficient off-site processing.
- Explore Corporate Donation Programs: Let's talk about how your company can partner with us to build a structured donation-based recycling program that maximizes your community impact and supports your CSR goals.
Protecting your business and contributing to your community aren't separate goals. With Reworx Recycling, they happen at the same time. Contact us today to build an IT asset disposition strategy that is secure, sustainable, and truly makes a difference.
Your Data Destruction Questions, Answered
Even after you've got a handle on the methods and compliance rules, some specific questions always seem to pop up when it's time to actually plan a data destruction project. Let's tackle some of the most common ones to clear up any lingering doubts and help you move forward with confidence.
Is Deleting Files or Formatting a Hard Drive Enough?
Absolutely not. Think of it this way: deleting a file is like tearing the table of contents out of a book. The actual chapters and all the information inside are still there, perfectly readable for anyone who knows where to look.
Similarly, deleting files or formatting a drive just removes the easy signposts that point to your data. The data itself remains on the drive, and it’s surprisingly easy to get back with basic recovery software. This is why you need secure data destruction services from a certified partner to guarantee your information is gone for good.
What Is a Certificate of Destruction and Why Is It Important?
A Certificate of Destruction is a formal document that acts as your official proof that data-bearing devices were properly destroyed. It’s your audit trail, showing you complied with privacy laws like HIPAA, GDPR, or NIST standards. Essentially, this certificate is your compliance armor.
A Certificate of Destruction isn't just a receipt; it's your verifiable proof that protects you from liability. It meticulously lists the destruction method, the date, and a serialized inventory of every single asset that was destroyed.
If you ever face an audit or a legal challenge, this document is the concrete evidence you'll need to show you did everything by the book. Without it, you’re left exposed.
Can We Recover Value from Our Old IT Equipment?
Yes, you absolutely can. In many situations, that old IT equipment sitting in a closet still has a good bit of residual value. As a full-service IT Asset Disposition (ITAD) partner, Reworx Recycling looks over your equipment to see what can be refurbished and resold. This is often called value recovery or IT asset remarketing.
For devices that can be safely sanitized and given a second life, your organization can get a financial return, turning a depreciated expense into fresh revenue. For anything that’s truly at its end, we make sure it’s handled through responsible, eco-friendly recycling channels. This approach ties financial recovery directly to your corporate sustainability goals, getting the most out of your original tech investment.
Your old technology holds sensitive data and potential liabilities. Partnering with Reworx Recycling provides certified secure data destruction services that eliminate risk while supporting environmental sustainability and community initiatives. Don't leave your company's security to chance.
Explore our certified ITAD and recycling solutions today.