Your telecom refresh is finally moving. New switches are on order, the carrier cutover is scheduled, and someone has asked the dangerous question: “Can we just find ITAD telecom services near me and get the old gear out next week?”
That's usually the point where a straightforward upgrade turns into a risk project.
Retired telecom equipment rarely sits in one neat pile. It's spread across network closets, branch offices, server rooms, MDFs, IDFs, storage shelves, and sometimes the trunk of a facilities manager's car. Some assets still hold configurations or data. Some still have resale value. Some are regulated electronic waste that can't be treated like ordinary scrap. If you don't define the job clearly, local vendors will quote against assumptions, and assumptions are where projects go sideways.
A good local ITAD partner does more than haul hardware away. The right one can document custody, sanitize data-bearing devices properly, explain value recovery without fee games, and support your compliance and sustainability goals. That's the standard worth using when you search for ITAD telecom services near me.
Defining Your Telecom ITAD Project Scope
Most telecom decommissioning projects start with an incomplete list. Someone knows about the core switches. Someone else remembers the handsets in a satellite office. Then facilities finds a rack of legacy gear nobody claimed.
That's why the first task is not getting quotes. It's building a scope that a disposal partner can successfully execute.

The volume coming into ITAD channels is only getting larger. The global ITAD market is projected to reach about USD 54.54 billion by 2030, and the IT and telecom segment accounted for over 30% of industry revenue in 2024 according to Grand View Research's IT asset disposition market analysis. That tells you something practical. Telecom retirement work is now routine enough to demand process, not improvisation.
Start with an asset list you can defend
A usable inventory goes beyond “20 switches and some phones.” Break assets into operating categories so your internal team and any vendor are speaking the same language.
Use categories like these:
- Core network equipment. Routers, switches, firewalls, network appliances, load balancers.
- Telecom systems. PBX hardware, VoIP handsets, conference phones, gateways, SBCs.
- Wireless infrastructure. Access points, controllers, antennas, mounts, injectors.
- Data center and edge gear. Servers, storage arrays, telecom racks, patch panels, console gear.
- Supporting electronics. UPS units, batteries, power supplies, transceivers, cables, adapters.
Add model numbers and serial numbers where you can. For data-bearing devices, flag them clearly.
Practical rule: If a device ever touched your production network, treat it as sensitive until someone proves otherwise.
Triage by urgency, value, and handling complexity
Not every asset needs the same treatment. Some items need immediate secure disposition because they contain storage or configuration data. Others can wait for a consolidated pickup. Some may be candidates for asset recovery.
A simple triage model works well:
| Priority type | What belongs there | Why it matters |
|---|---|---|
| Immediate control | Firewalls, appliances, servers, storage, phones with stored data | These create the highest security risk |
| Logistics-sensitive | Rack gear in active closets, roof-mounted or hard-to-access telecom equipment | Removal planning affects labor, timing, and safety |
| Value-review | Newer switches, routers, servers, reusable handsets | These may offset part of the project cost |
| Recycle-only | Damaged, obsolete, incomplete, or nonfunctional electronics | These need compliant downstream handling |
This is also the point to separate “must remove now” from “can remove during the larger office exit.” If your telecom retirement overlaps with furniture liquidation or a broader move, coordinate it. Teams often save time when ITAD is planned alongside efficient office furniture removal and disposal instead of handled as a last-minute add-on.
Don't ignore physical access
A local quote can be wrong even when the asset count is right. Why? Access conditions drive labor.
Record details such as:
- Site layout. Loading dock, elevator access, stair-only rooms, after-hours restrictions.
- Equipment condition. Live rack, powered down, already unracked, loose on pallets.
- Packaging status. Boxed, shelf-stored, or still mounted in cabinets.
- Geographic spread. Single site, multiple branches, or mixed office and warehouse locations.
A vendor can't plan chain of custody or transportation well if your own team doesn't know where the assets are and who controls each location.
Build a project brief before requesting bids
The best handoff document is short, specific, and operational. Include asset categories, estimated counts, serial-number expectations, site access notes, timing constraints, and any mandatory reporting you require. If your team needs a quick refresher on the process itself, this overview of IT asset disposition is a useful baseline for aligning IT, facilities, procurement, and compliance.
A strong scope does two things. It improves vendor responses, and it exposes missing assets before pickup day instead of after the truck leaves.
Ensuring Compliance and Bulletproof Data Security
Telecom disposal becomes a security issue the moment retired gear leaves your control. That includes obvious assets like servers and storage, but it also includes firewalls, phones, routers, switches, and appliances that store credentials, configs, logs, or cached data.
If you only remember one rule, remember this: a vendor's reassurance is not a control.
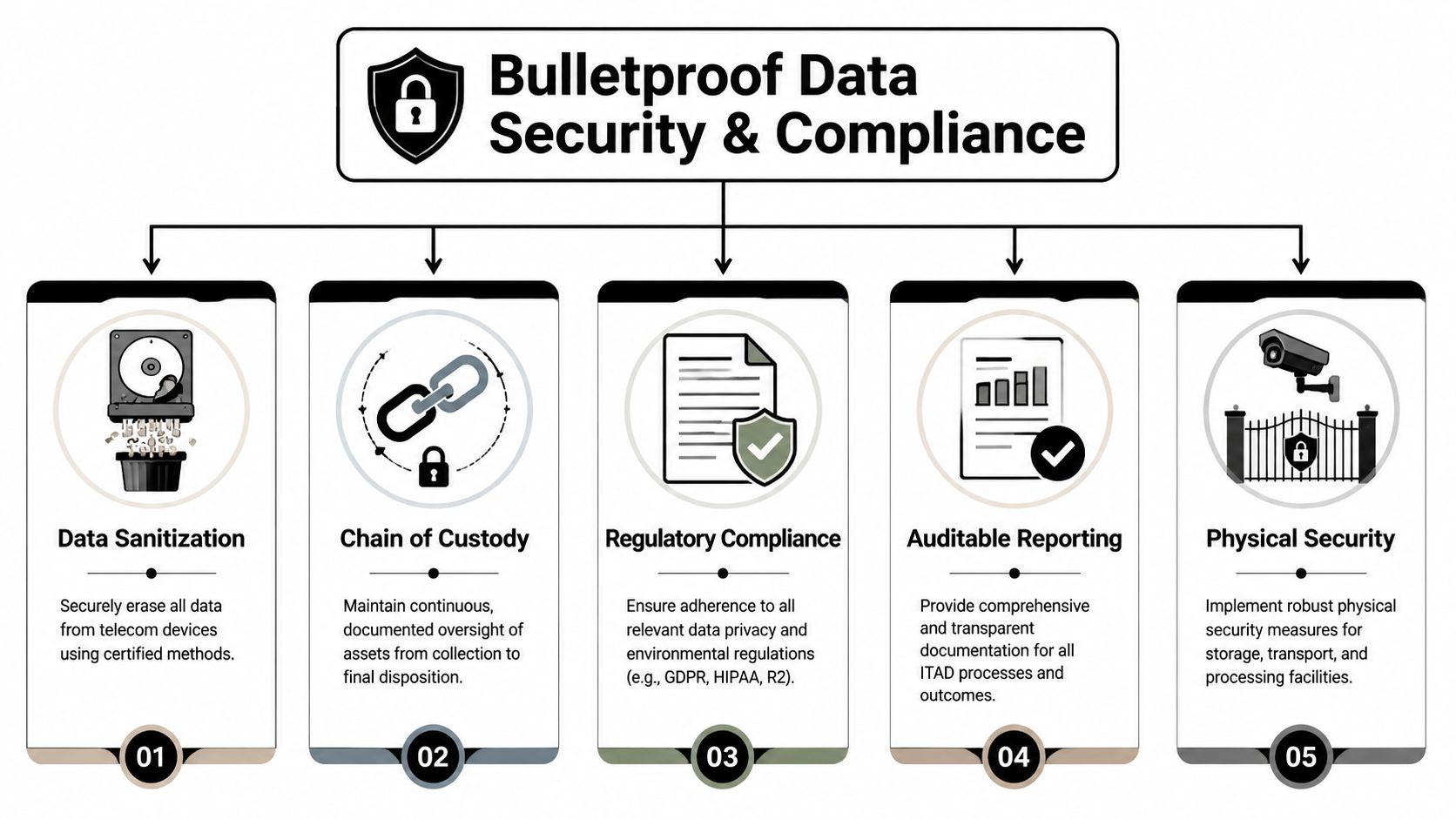
Industry guidance cited by Reworx notes that roughly 35% of data breaches are traced back to IT and telecom equipment that was not properly sanitized before being resold, reused, or recycled in its telecom equipment disposition guidance. That's why local ITAD selection should start with data destruction controls, not pricing.
Know what certifications actually do
Certifications don't guarantee perfect execution, but they give you a baseline for process, training, and auditability. For telecom projects, I look for certifications as evidence that the vendor operates inside documented controls rather than informal shop practices.
A practical screening list includes:
- R2 certification. Indicates process discipline around responsible recycling and downstream controls.
- NAID AAA. Relevant when you need verified data destruction processes and documentation.
- ISO-related controls. Useful when you want evidence of formal management systems.
- HIPAA-aligned handling. Important when telecom gear intersects with healthcare workflows or protected data environments.
If a vendor says it's certified, ask for the certificate and verify dates. Don't accept “we follow the same standards” as a substitute.
For data-destruction-specific due diligence, Reworx's NAID AAA certification page shows the kind of credential detail you should expect any serious provider to supply.
Match the destruction method to the asset
Not every device should be handled the same way. Over-destroying recoverable gear can erase value. Under-securing data-bearing gear can create a compliance problem.
Use this decision framework:
| Asset type | Common risk | Appropriate control |
|---|---|---|
| Servers and storage arrays | Residual data on drives | NIST 800-88 aligned wiping when reuse is allowed, or physical destruction where policy requires it |
| Firewalls and network appliances | Stored configs, credentials, logs | Verified sanitization and device-specific validation |
| Switches and routers | Startup configs, cached settings, removable media in some cases | Reset is not enough. Require documented sanitization |
| Mobile and telecom endpoints | User data, call logs, credentials | Wiping plus audit trail, or physical destruction if chain-of-custody risk is high |
A factory reset is an operational step. It is not the same thing as documented data sanitization.
For some projects, software wiping is the right path because it supports reuse or remarketing. In others, degaussing or shredding is the safer answer because policy, regulator expectations, or asset condition make reuse irrelevant. The point is to decide intentionally, not let the vendor decide based on convenience.
Chain of custody is where good plans hold up
A secure process has to survive handoffs. That means from rack removal to staging, from staging to transport, and from transport to processing. Chain of custody should be visible and documented at each point.
What I want to see in practice:
- Pre-disposition inventory with serial-number-based asset tagging where possible.
- Transport records showing who released, received, and moved the equipment.
- Processing confirmation tied back to the original inventory.
- Certificates of destruction that identify what was destroyed and when.
If your project includes multiple sites, require site-level manifests. A combined certificate issued weeks later is usually too blunt to resolve discrepancies.
Segregation of duties matters more than people think
One of the most common ITAD mistakes is letting a single person or single vendor workflow control the entire process without independent checks. The Retire-IT guidance on vendor risk argues for a segregation-of-duties framework, detailed destruction certificates, and 100% chain-of-custody documentation with zero unexplained asset discrepancies in its write-up on ITAD control failures.
That sounds formal, but the application is simple. The person who approves the inventory shouldn't be the only person who confirms pickup. The vendor employee loading the truck shouldn't be the only one who records what left the site. The certificate shouldn't be accepted without matching it back to the original list.
What works: tagged inventory, independent verification, documented handoffs, and final reconciliation.
What fails: trust-based pickups, vague manifests, and “we'll send the paperwork later.”
Managing Logistics and Maximizing Asset Value
Once the security model is fixed, the next problem is operational math. How do you get the gear out with minimal disruption, and what will the project really return after fees, labor, and processing?
Many "ITAD telecom services near me" searches go wrong at this point. Buyers compare headline buyback language and ignore the mechanics underneath it.

Pick the right logistics model for the site
There isn't one correct pickup model. The right one depends on volume, access, sensitivity, and whether your staff can prepare assets beforehand.
Three common models:
- Onsite packing and palletizing. Best when gear is still in racks, spread across closets, or too sensitive to leave to internal cleanup.
- Scheduled business pickup. Works when your team has already staged and inventoried the equipment.
- Customer drop-off. Useful for small loads, but less practical for distributed telecom refreshes.
The cheapest option on paper can become the most disruptive one in practice. If your team spends days breaking down racks, matching inventory, and moving gear to a dock without proper controls, you may save on vendor labor but lose more in internal time and risk.
Asset value isn't what the first quote says
Telecom gear has uneven secondary market value. Newer enterprise switches, routers, and servers may return value. Damaged units, incomplete kits, unsupported models, and heavily customized systems often won't.
The mistake is assuming that a rough estimate equals a net payout.
Industry analysis highlighted by Data Recycling NE shows that some vendors use fee-stacking methodologies that can reduce client payouts by 40-70% from initial estimates, as described in its analysis of ITAD remarketing fee structures. The issue isn't that fees exist. The issue is when logistics, testing, refurbishing, and recycling charges get deducted in a sequence that makes the original value estimate misleading.
If a vendor can't explain exactly when fees are applied, assume the estimate is a marketing number, not a forecast.
Ask for financial transparency before assets move
You don't need a long legal memo. You need a fee schedule that makes it hard for surprises to hide.
Ask each provider to show:
| Financial question | Why it matters |
|---|---|
| Is the valuation based on actual condition or ideal condition? | Condition assumptions can distort expected returns |
| Are logistics and testing charged before or after revenue split? | The sequence changes your payout materially |
| What happens to no-value assets? | Some programs quietly turn buyback into disposal billing |
| When do you receive itemized reporting? | Slow reporting makes disputes harder |
I'm skeptical of any bid that promises strong recovery value but gives vague language on packaging, transport, testing, and recycling charges. Transparent vendors can usually explain this in a page or two.
If you're trying to tighten your broader lifecycle process, these future IT asset management tips are worth reviewing alongside your disposition planning. Better intake, tagging, and refresh discipline usually lead to cleaner ITAD outcomes later.
What practical buyers should demand
For larger telecom retirements, I'd put these requirements in writing:
- A pre-approved fee schedule with line items.
- A condition methodology that defines how gear will be graded.
- A timeline for reconciliation after sale or processing.
- A clear path for reuse, recycling, and nonmarketable assets.
One provider type in this category is Reworx's asset recovery solutions, which outline value recovery alongside disposition services. Whether you use that model or another local option, the important part is getting line-item logic before the equipment leaves your site.
A transparent project may produce less optimistic estimates upfront. That's fine. Accurate numbers are more useful than inflated ones that collapse after deductions.
Meeting Sustainability Goals and Regulatory Demands
A telecom disposal project can satisfy the operations team and still fail the sustainability review. That happens when the chain beyond first pickup is opaque.
Many organizations now treat ITAD as part of ESG reporting, internal audit readiness, and public accountability. That changes the vendor standard. It's no longer enough for a provider to say equipment was “recycled responsibly.” You need to know what that means operationally.

Downstream visibility is the real compliance test
The SK tes industry discussion on ITAD sustainability risk notes that businesses face reputational and legal risks from ITAD partners with opaque downstream recycling chains, and that verifying domestic-only processing and transparent audits is a critical ESG due diligence step in its IT asset disposition services overview.
That point matters because environmental risk often sits downstream, not at pickup. If a vendor can't explain where non-reusable telecom assets go next, your internal ESG narrative is weaker than it looks.
Here's what to ask for:
- Downstream processor disclosure. Who handles what after initial sorting?
- Audit visibility. Can the provider show audits or certification evidence for downstream partners?
- Domestic processing clarity. If your policy requires domestic-only handling, can they confirm it in writing?
- Reporting quality. Will you receive records that support compliance and sustainability reporting?
Social impact can be part of the disposal strategy
A social enterprise model can change this decision. Some organizations want more than compliant electronics recycling. They want a path that connects surplus technology management with community benefit, donation-based recycling, and digital inclusion.
That doesn't remove the need for security or environmental controls. It raises the bar. A credible social enterprise still has to prove where devices go, what was recycled, what was reused, and how sensitive assets were handled. The benefit is that your end-of-life process can support both waste diversion and community outcomes instead of stopping at “material processed.”
A sustainability claim is only useful when operations can document it.
What strong sustainability reporting looks like
A usable ITAD sustainability file should help your IT team, compliance team, and CSR or ESG lead answer basic questions without chasing the vendor for weeks.
Look for reporting that covers:
| Reporting area | What you need |
|---|---|
| Asset disposition summary | What was reused, recycled, destroyed, or held for review |
| Environmental documentation | Certifications and downstream handling records |
| Community or donation outcomes | If applicable, documentation that supports the social claim |
| Audit support | Records that can stand up to internal review |
If you're evaluating local providers, Reworx's electronics recycling certification information is the kind of certification-oriented material that should be easy to obtain during due diligence.
For business owners and sustainability leaders, that's the bigger shift. ITAD isn't just cleanup anymore. It's part of how you prove your organization retires technology responsibly.
How to Vet and Select Your Local ITAD Partner
Once you've defined scope, security requirements, financial expectations, and sustainability needs, vendor selection gets simpler. Not easy. Simpler.
Most local providers can describe pickups. Fewer can survive detailed questions about controls, reconciliation, and accountability. That's the gap your vetting process needs to expose.
Use a shortlist built on evidence
Start by eliminating vendors that rely on broad claims. A credible ITAD partner should be able to show documentation quickly, not after repeated follow-up.
My first-pass checklist looks like this:
- Certification proof. Current documents, not verbal assurances.
- Sample reporting. Manifests, destruction certificates, and reconciliation examples.
- Service clarity. Pickup, onsite services, packaging, sanitization, and downstream handling defined in writing.
- Insurance discussion. Enough detail to support internal risk review.
- Escalation path. Named contacts for operations and issue resolution.
If they can't provide basic documents during the sales process, expect more friction after your assets leave the building.
Ask questions that test operations, not marketing
A polished website won't tell you whether the vendor's process is tight. Specific questions will.
Use questions like these in calls and RFPs:
- How do you maintain chain of custody from site release through final processing?
- What data destruction methods do you use for routers, switches, servers, storage, and telecom endpoints?
- Can you provide a sample certificate of destruction and a sample asset manifest?
- How do you reconcile discrepancies between pickup inventory and processing inventory?
- Which certifications apply to your recycling and destruction workflows, and can you provide current documentation?
- Who are your downstream processors, and how do you audit them?
- How do you calculate resale value and fees on recoverable telecom assets?
- What happens when an asset arrives damaged, incomplete, or different from the manifest?
- What reporting will we receive, and when?
- What is your contingency plan if a scheduled pickup, transport handoff, or processing step fails?
This line of questioning does something useful. It forces the provider to talk about real workflow, and weak workflows are hard to hide in detailed answers.
The best vendor conversations sound operational. The worst ones sound reassuring.
Verify segregation of duties and audit discipline
The Retire-IT guidance is especially useful here because it moves beyond simple trust. It recommends a segregation-of-duties framework, detailed destruction documentation with R2 or NAID AAA certifications, and the goal of 100% chain-of-custody documentation with zero unexplained asset discrepancies. That's the right benchmark for reviewing any local partner.
Translate that into practical checks:
| Control area | What to verify |
|---|---|
| Inventory accountability | Assets are tagged or listed before pickup and reconciled later |
| Handoff control | More than one person can verify release and receipt |
| Destruction proof | Certificates identify assets clearly enough to audit |
| Exception handling | Missing, extra, or mismatched assets trigger documented review |
If a vendor shrugs off discrepancy management with “that never happens,” keep looking. Mature operators expect exceptions and have a process for them.
Evaluate fit for your actual environment
A local provider isn't automatically the right provider. You want geographic convenience, but you also need fit.
A branch-heavy healthcare group, a city agency, a school district, and a regional manufacturer all retire telecom gear differently. Your provider should understand site access rules, chain-of-custody expectations, and reporting needs in your setting. That includes facility constraints like loading docks, security escorts, after-hours windows, and multi-site scheduling.
I also look for one more sign of maturity. Good vendors ask sharp questions back. They want to know whether assets are still racked, whether serials are available, whether some equipment is intended for remarketing, and whether your internal team requires site-level certificates. That's a good sign because it means they're planning the work instead of just trying to win it.
Red flags that should stop the process
Some warning signs are worth treating as disqualifiers.
- Vague destruction language such as “we wipe everything” without method details.
- No sample paperwork for manifests or certificates.
- Unclear downstream story once equipment leaves primary custody.
- Aggressive value estimates paired with fuzzy fee language.
- One-person control over inventory, pickup, and reconciliation.
- Delayed answers to basic compliance questions.
When you search for ITAD telecom services near me, proximity matters. Process matters more. The vendor that can prove custody, destruction, fee logic, and downstream accountability is usually the safer choice than the vendor with the fastest pickup promise.
Your Next Steps for Responsible Telecom Equipment Disposal
A telecom decommissioning project gets easier once you stop treating it like junk removal. It's a controlled retirement process for assets that may carry data, resale value, regulatory exposure, and sustainability implications all at once.
The sequence is straightforward. Define the full asset scope. Separate high-risk gear from ordinary recycling loads. Require documented data destruction and chain of custody. Push for line-item financial transparency. Verify downstream handling, not just pickup capability. Then choose the local provider that can prove its process in writing.
That's the standard businesses should use when evaluating ITAD telecom services near me.
If your team is preparing for an office cleanout, network refresh, data center decommissioning, or broader telecom retirement project, telecom equipment disposal near you through Reworx Recycling is one path to review alongside other qualified providers. The practical test is the same either way. Ask for evidence, not promises.
A well-run ITAD project protects your organization twice. It prevents unnecessary security and compliance exposure today, and it gives you cleaner records, stronger controls, and a more defensible sustainability story tomorrow.
If you're ready to retire old telecom gear, computers, servers, or office electronics through a certified, community-minded process, explore the services and planning resources on Reworx Recycling. You can use that next step to schedule a pickup, evaluate secure data destruction options, or build a donation-based recycling plan that supports both compliance and community impact.