A lot of Phoenix businesses reach the same moment at once. New laptops arrive, a server refresh is underway, the office storeroom fills with retired monitors, and someone asks a simple question that turns out not to be simple at all. What do we do with all this old equipment?
That pile of devices is more than clutter. It may contain customer records, employee data, saved credentials, licensed software, and components that require careful handling. For a business owner, school administrator, facilities leader, or city department manager, disposal is no longer a housekeeping task. It’s a security, compliance, and operational decision.
That’s why Responsible IT Asset Disposal Services in Phoenix matter. In a city with active technology turnover, expanding business infrastructure, and growing expectations around sustainability, the end of an asset’s life needs as much discipline as the day it was purchased.
Navigating Your Next Tech Upgrade in Phoenix
A Phoenix accounting firm replaces desktop computers across two floors. A medical office retires a cart of aging laptops. A charter school swaps out old classroom devices over summer break. In each case, the team usually starts with the same assumption: if the equipment is old, broken, or slow, the hard part is over.
It isn’t.
Old equipment still holds risk until someone documents it, secures it, transports it, sanitizes it, and sends it to the right downstream path. That’s where many organizations get stuck. They know they shouldn’t throw electronics in a dumpster, but they’re less sure about chain of custody, data destruction standards, or what counts as acceptable recycling.

Phoenix has a mature ITAD environment, and that matters for buyers. Local providers are reporting over 99% accuracy in inventory reports and using standards tied to R2 and e-Stewards, while long-established firms such as DMD Systems, founded in 1994 in Tempe, show that the regional market has been developing for decades, as noted in this Phoenix ITAD market trends overview. If you’re handling desktops, networking gear, servers, or end-user devices, you’re not dealing with a niche service anymore. You’re dealing with an established business function.
What business owners usually underestimate
The first issue is data. Even when a machine won’t boot, data may still be recoverable from the storage media.
The second issue is documentation. If you can’t show what left your building, when it left, who handled it, and how it was processed, you’re relying on trust when you should be relying on records.
Why the right process feels different
A responsible provider doesn’t just “take stuff away.” They inventory assets, separate reuse candidates from scrap, apply approved sanitization methods, and create paperwork your compliance team can use.
For businesses looking at local options for computer recycling in Phoenix, that distinction is the difference between a cleanup job and a risk-managed retirement process.
Old devices stop being harmless the moment nobody owns the disposal decision.
The High Stakes of Improper IT Asset Disposal
Improper disposal creates two types of damage at the same time. One is immediate and visible, such as a data exposure or failed audit. The other unfolds later, when a regulator, customer, or insurer asks for records you don’t have.
Arizona organizations shouldn’t treat this as a minor back-office issue. Disposal errors can trigger environmental liability, privacy problems, contract issues, and expensive remediation work. When executives see old equipment as “junk,” they often miss that the law may still see it as regulated material and the business may still see it as sensitive information.
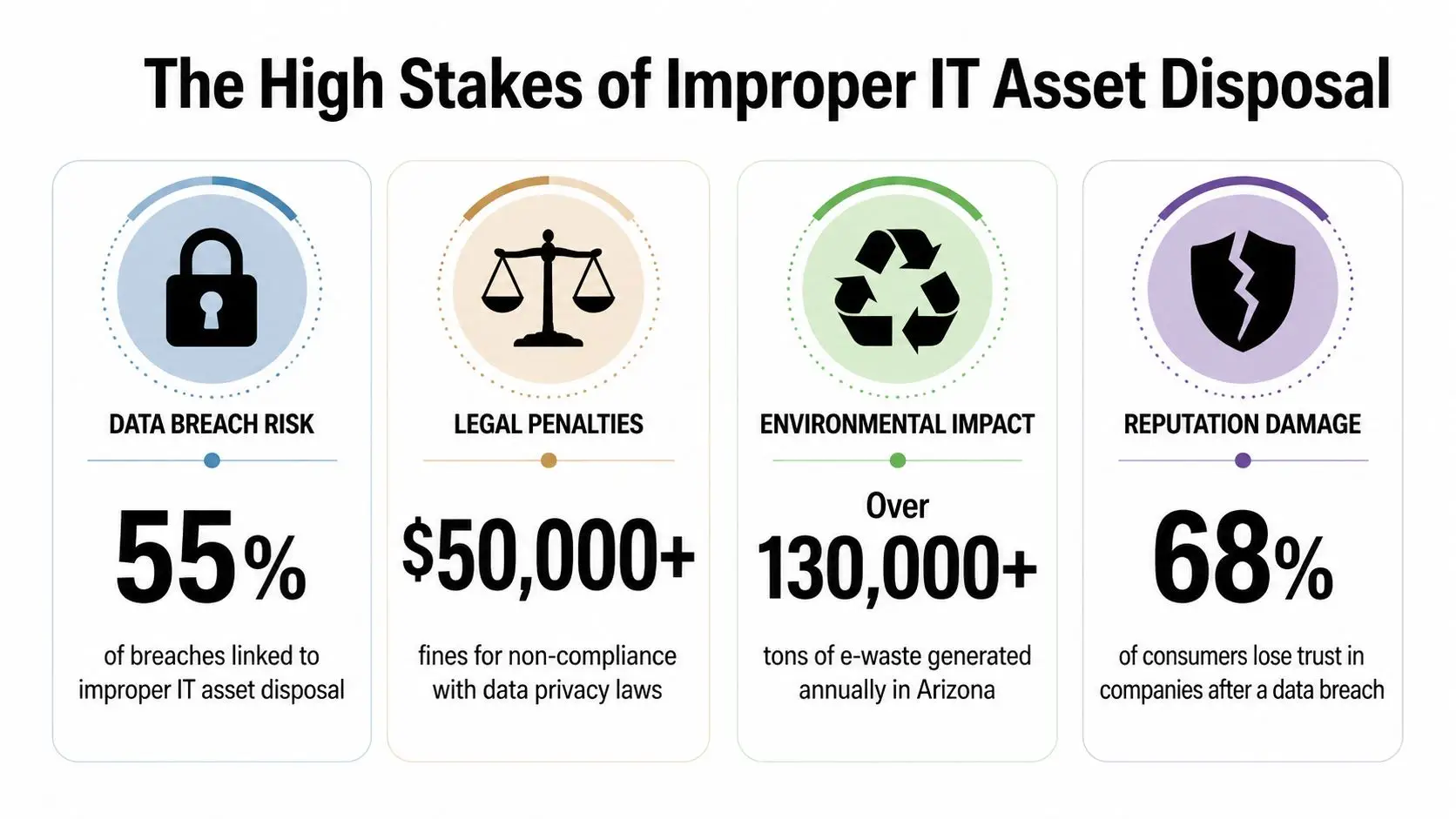
The penalty side is serious
Under the Resource Conservation and Recovery Act, federal fines for improper IT asset disposal can reach $93,750 per day per violation, and Arizona state penalties can reach $25,000 per day, according to this guide to electronics disposal and IT asset management in Phoenix.
Compliance reality: A disposal shortcut that seems cheaper upfront can become the most expensive line item in the whole project.
Those figures get attention, but the fine itself is rarely the whole story. Once an issue surfaces, businesses also deal with internal investigation time, legal review, customer communications, replacement costs, and brand damage. For schools and public agencies, the scrutiny can be even harder because the records and procurement trail may be subject to public review.
Data exposure is often the hidden trigger
Most owners worry about visible failures, such as an illegal dump or a stack of monitors left near a loading dock. The more common concern is quieter. A hard drive leaves the building without proper sanitization. A copier gets sold with stored data intact. A batch of laptops goes to an uncertified downstream handler with no usable audit trail.
That’s why disposal belongs in your security program, not just your facilities workflow.
Consider how these mistakes happen:
- Untracked removals: A staff member clears a closet, but no serial numbers are recorded.
- Informal resale: Someone donates or resells devices without confirming data destruction.
- Mixed waste handling: Electronic devices get bundled with general junk during an office cleanout.
- Missing certificates: The vendor says the equipment was destroyed, but your team has no defensible documentation.
Reputation loss follows operational failure
Customers usually won’t distinguish between a breach caused by active systems and a breach caused by retired assets. They’ll see one thing. Your organization lost control of information it was expected to protect.
That matters in Phoenix’s competitive business environment, where trust supports renewals, referrals, and public confidence. It also matters internally. Boards, finance leaders, and department heads remember the incident that “came from old equipment nobody thought about.”
If you need a broader business case for disciplined handling, the environmental side is part of that story too. This overview of the environmental impact of electronic waste helps frame why improper disposal creates both compliance and community consequences.
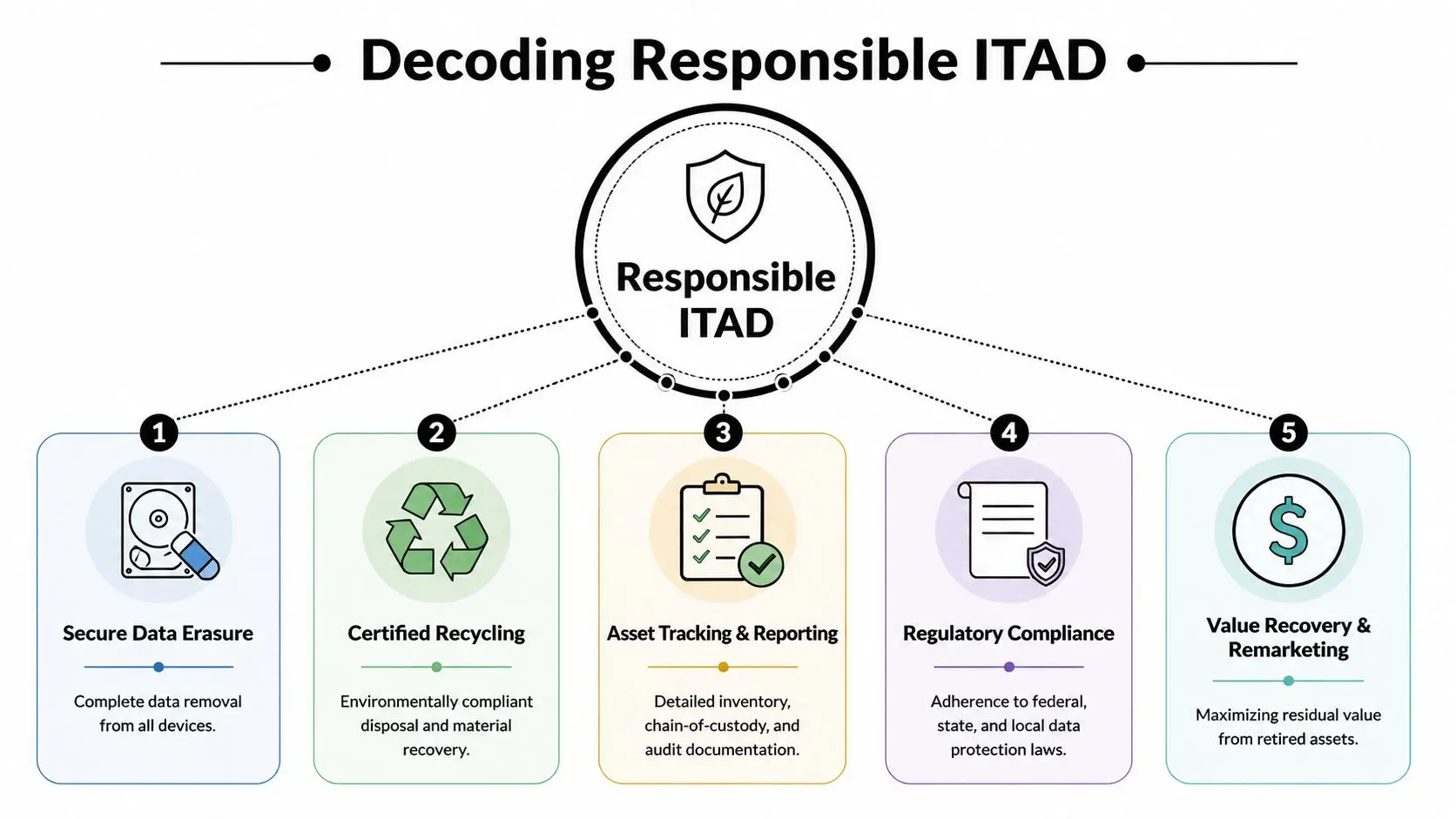
Decoding Responsible ITAD What It Really Means
A lot of providers use the term IT asset disposition, or ITAD, as if it means any form of pickup and recycling. It doesn’t. Responsible ITAD is a controlled process built on three pillars: data destruction, environmental compliance, and value recovery.
If one pillar is weak, the whole program is weak. A recycler can be environmentally careful and still mishandle data. A data destruction vendor can shred drives but provide little visibility into where the rest of the equipment ends up. A remarketing firm can recover value but leave your compliance team with thin documentation.
Pillar one is data destruction
Standards matter more than promises. NIST SP 800-88 Rev. 1 is the benchmark many organizations use for data sanitization decisions. It gives practical categories for how media should be handled, depending on risk and device type.
The same Phoenix workflow reference notes that responsible providers use methods such as overwrite, degauss, and physical destruction, and that R2v3 certification requires certified firms to divert over 95% of e-waste from landfills and demonstrate 99.9% data destruction efficacy, often using NAID AAA-validated shredders, as described in this IT asset disposal workflow resource.
Here’s the plain-English version of the common methods:
- Clear: Software overwriting for media that can be sanitized and reused.
- Purge: More forceful removal methods, such as degaussing or similar approaches for higher-risk situations.
- Destroy: Physical shredding when reuse isn’t appropriate or policy requires total destruction.
Practical rule: If a device held sensitive business data, ask what sanitization method was used for that exact device type, not just whether the vendor “wipes everything.”
Pillar two is environmental and legal compliance
Responsible disposal doesn’t end when data is gone. Equipment still contains metals, plastics, circuit boards, batteries, and other components that have to be routed properly. Certifications help here because they force discipline on the whole chain, not just the first pickup.
That includes downstream accountability. A provider should be able to explain where materials go after sorting, who processes them, and how those partners are vetted. If they can’t answer that, your risk hasn’t disappeared. It’s just moved out of sight.
A compliance-minded process usually includes:
- Serialized intake records: So every asset can be reconciled.
- Chain-of-custody documentation: So handoffs are visible.
- Certificates of destruction or recycling: So your team can prove what happened.
- Retention of records: So audit and insurance questions can be answered later.
Pillar three is value recovery
This part often confuses buyers. Value recovery does not mean every retired asset is worth money. It means the provider evaluates whether usable equipment can be refurbished, remarketed, or otherwise routed for higher-value reuse before final recycling.
That’s a discipline, not a guarantee.
For decision-makers comparing programs, this background on what IT asset disposition involves is useful because it separates disposal from asset management. In practice, the strongest programs ask two questions for every device: Is the data handled properly, and is this item better suited for reuse or materials recovery?
What responsible looks like on the ground
A responsible ITAD engagement usually feels orderly. The provider tags assets, verifies counts, records serials, secures transport, sanitizes or destroys data-bearing media, issues documentation, and reports final disposition.
When buyers get confused, it’s usually because vendors compress all of that into a vague phrase like “full service recycling.” A better question is simpler. Ask them to walk you through one laptop, one server, and one hard drive from your office to final disposition. If they can explain each path clearly, you’re closer to a responsible partner.
A Guide to Core IT Asset Disposal Services
Most organizations don’t need theory first. They need to know what happens after they call an ITAD provider. The answer should sound like an operational workflow, not a sales pitch.
A complete service model usually starts before pickup day. Your team and the vendor agree on scope, site access, equipment categories, and any special handling for servers, networking gear, printers, storage arrays, or medical and lab equipment. If the project involves a lease return, office closure, or data center decommissioning, the provider should map those details early.
What the service flow usually includes
Pickup and secure transport
Equipment is collected from your Phoenix office, school, warehouse, or facility. Better programs treat transportation as part of the control system, not a courier task.Inventory and reconciliation
Assets are counted, tagged, and checked against your internal records. Missing items often surface during this process, making it an indispensable step.Testing and triage
Some devices are suitable for reuse or remarketing. Others move straight to destruction or commodity recycling based on condition and policy.Data destruction
Media is sanitized or physically destroyed according to the agreed standard. You should be able to tie that outcome back to specific assets or device groups.Final reporting
Your organization receives certificates and a disposition summary that finance, compliance, and IT can all understand.
Services that matter more than buyers expect
A few service features tend to separate mature providers from casual recyclers:
- On-site decommissioning: Useful when equipment can’t sit unsecured before removal.
- Serialized reporting: Important for audit defense and internal asset reconciliation.
- Media destruction options: Needed when policy requires physical destruction.
- Remarketing support: Helpful when some devices still have useful life.
- Project management: Critical during moves, closures, and refresh cycles.
This is also the point where provider fit matters. Some organizations need a narrow shredding engagement. Others need national pickup coordination, office cleanout support, and a process for donation-based recycling. Firms evaluating service models can review examples through IT asset disposition services, including secure data destruction, equipment handling, and end-of-life processing.
One practical example
Take a mid-sized Phoenix law office replacing employee laptops and conference room technology. The office manager may think the project is about removing old hardware quickly. The IT lead knows the primary task is preserving a clean chain of custody, confirming destruction of data-bearing media, and documenting what happened to every device.
That difference in perspective is why a written scope matters. It turns a pickup into a controlled disposal event.
A useful service description names the handoffs, the records, and the asset paths. If it only says “we recycle electronics,” keep asking questions.
How to Choose the Right ITAD Partner in Phoenix
Vendor selection is where many disposal programs succeed or fail. Buyers often focus on convenience first. Can the company pick up fast? Will they take mixed loads? Can they help during a move? Those questions matter, but they come after the hard ones.
The hard questions are about control. What standards do they follow? What proof do they provide? How transparent are they about downstream handling? Do they understand the needs of a school district, healthcare office, public agency, or growing SMB that doesn’t have a dedicated compliance staff?
Phoenix ITAD Vendor Selection Checklist
| Criteria | What to Look For | Why It Matters |
|---|---|---|
| Certifications | Current certifications relevant to recycling and data destruction practices | Certifications create a baseline for process discipline and third-party accountability |
| Data sanitization methods | Clear explanation of wiping, degaussing, and shredding options | Different assets require different handling, and vague answers create risk |
| Chain of custody | Serialized tracking, intake records, and documented handoffs | You need proof that assets stayed controlled from pickup through disposition |
| Reporting | Certificates of destruction, recycling records, and usable inventory reports | Audit, legal, and internal teams need documentation they can act on |
| Downstream transparency | Ability to explain who receives materials after initial processing | Your liability concern doesn’t end at the first vendor |
| Insurance coverage | Proof of relevant coverage, including environmental and data-related exposure where applicable | Insurance doesn’t replace process, but it shows operational maturity |
| Service fit | Pickup options, project management, office cleanout or decommissioning support | The vendor should match your real workflow, not force you into theirs |
| Social impact model | Whether reusable equipment can support donation and digital inclusion programs | Some organizations want disposal outcomes that also support community benefit |
Questions worth asking on the first call
Instead of asking “How much do you charge?” start with questions that expose process quality.
- Ask for the asset journey: Have them describe what happens from pickup to final disposition.
- Ask who signs off: Find out who verifies inventory and who authorizes destruction.
- Ask for sample documentation: You want to see the form of the certificate, not just hear that one exists.
- Ask about exceptions: What happens when serial numbers are unreadable, devices are damaged, or counts don’t match?
- Ask about reuse policy: Determine how they decide between donation, remarketing, dismantling, and shredding.
Mission also matters
Two vendors can sound similar on compliance and still differ sharply in business model. One may process scrap. Another may support a structured reuse pathway for appropriate equipment, tying retirement programs to community benefit.
For organizations that care about both risk control and program values, this guide to selecting a reliable e-waste recycling partner is a helpful screen for comparing providers more carefully.
A social enterprise model can be relevant here. If a provider supports donation-based recycling, digital inclusion, or workforce development, that may align with your ESG, procurement, or community partnership goals. It shouldn’t replace due diligence, but it can strengthen the business case when reuse is handled securely and documentation remains strong.
ITAD Logistics and Costs for Phoenix SMBs and Agencies
Small and mid-sized organizations usually have a different problem than enterprise teams. They don’t lack urgency. They lack spare staff time, storage space, and confidence that they’re following the rules correctly.
That’s why generic ITAD advice often falls flat for Phoenix SMBs, schools, and agencies. It assumes an internal asset management team, a formal security office, and a procurement structure that can absorb complexity. Many local organizations have none of those things. They have an office manager, an overextended IT generalist, or a facilities lead trying to clear equipment before a move.

Why SMBs get tripped up
A 2023 EPA report noted that 70% of U.S. SMBs mishandle e-waste due to compliance complexity, and Gartner data from 2025 shows U.S. ITAD recovery rates dropped 22% year over year, according to this Phoenix-area ITAD services discussion. The lesson isn’t that smaller organizations are careless. It’s that disposal requirements are easy to get wrong when the process feels fragmented and the value story is overstated.
That second point matters. Some providers market buyback as if old equipment will naturally offset the whole project. In reality, value recovery depends on age, condition, demand, and the cost of handling. Buyers should expect a realistic review, not vague promises of “maximum value.”
Cost-effective ways to stay compliant
SMBs and agencies usually have more options than they think. The lowest-risk solution isn’t always full on-site destruction for every project.
A practical approach can include:
- Batching equipment by refresh cycle: Fewer pickups, cleaner inventory.
- Separating data-bearing from non-data-bearing devices: So security effort is focused where it matters most.
- Using certified drop-off or scheduled collection models when appropriate: Often simpler for lower-volume loads.
- Preparing a basic internal asset list before pickup: Even a spreadsheet is better than memory.
- Asking for clear documentation packages upfront: So there’s no confusion after removal.
For low-volume organizations, the goal isn’t to copy an enterprise ITAD program. It’s to build a lean version that still preserves control.
Phoenix logistics are operational, not just geographic
Local businesses also need to think about access, timing, and site conditions. Downtown offices may need loading dock coordination. Schools may want pickups outside classroom hours. Public entities may need vendor paperwork cleared before any truck arrives. Facilities with mixed waste streams may need e-waste separated before a cleanout can proceed.
That kind of local visibility is often what makes a project easy or painful.
There’s a parallel here with other service-driven local businesses. If you work with trades or field-service vendors, you’ve probably seen how operational visibility affects customer response and scheduling. This guide on local SEO for electricians is about a different industry, but it usefully shows how local service businesses in Phoenix compete on responsiveness, clarity, and trust. ITAD buyers can apply the same lens when comparing pickup communication, service coverage, and project coordination.
Where a donation-based model can help
For organizations with usable laptops, desktops, and peripherals, donation-based recycling can be a practical option when data destruction and documentation are handled correctly. It may reduce waste, support community technology access, and give leadership a better story than simple scrap removal.
This is one area where provider model matters. Reworx Recycling offers donation-based electronics recycling, secure data destruction, IT equipment disposal, and pickup support for organizations managing retired devices. For SMBs and agencies, that kind of model can be worth evaluating alongside traditional recycling-only vendors, especially when the organization wants both compliance and community benefit.
Take the Next Step Toward Responsible Disposal
A responsible disposal program does three jobs at once. It protects data, reduces compliance exposure, and keeps retired electronics out of the wrong waste stream. When those three outcomes line up, ITAD stops looking like a cleanup expense and starts looking like sound operational governance.
For Phoenix businesses, schools, healthcare offices, and agencies, the most important shift is mental. Old devices aren’t dead inventory. They are managed assets until documented final disposition is complete. That’s the standard your insurer, auditor, leadership team, and community would expect if something went wrong.
What a strong next step looks like
Start with a short internal review. Identify what equipment is waiting for retirement, which items may hold data, who owns the approval process, and what documentation you need back from a vendor.
Then screen providers with discipline:
- Confirm process clarity: Ask for the exact handling path.
- Confirm documentation: Require certificates and inventory reporting.
- Confirm fit: Match the provider to your volume, schedule, and security needs.
- Confirm values: If community reuse matters, ask how that pathway is governed.
Responsible disposal isn’t only about avoiding the wrong outcome. It’s also about choosing a process your organization can defend with confidence.
The strongest programs usually aren’t the most complicated. They’re the ones that make accountability visible from the first inventory list to the final certificate. For many Phoenix organizations, that alone removes the uncertainty that causes equipment to sit in closets and back rooms for months.
If your organization is ready to retire old equipment with better control, explore Reworx Recycling to learn more about donation-based recycling, secure data destruction, business pickups, and ways to turn retired technology into both risk reduction and community benefit.