Old technology rarely leaves a business all at once. It piles up.
A few laptops from a refresh project sit in a storage cage. A retired server stays in the network closet because nobody wants to touch it until the next audit. A box of phones from the last mobile upgrade ends up under a facilities shelf. Over time, that pile starts to feel normal.
It is not normal. It is unresolved risk and unrealized value.
In B2B operations, asset and recovery is the discipline of dealing with that backlog in a way that protects data, recovers value, supports compliance, and keeps equipment out of the wrong waste stream. In practice, that usually sits inside a broader IT asset disposition (ITAD) program.
Many teams still treat end-of-life equipment as a disposal task. That mindset is expensive. A smarter approach treats retired devices as business assets that need one final managed workflow.
Your IT Graveyard A Hidden Liability or Untapped Asset
Most organizations have an IT graveyard, even if they call it something else.
It may be a locked room near receiving. It may be a cage in a warehouse. It may be the “temporary” corner where old desktops wait for someone to decide what to do with them. The equipment looks harmless because it is powered off.

It is not harmless.
A retired laptop can still hold customer records, employee files, saved credentials, or cached email. An old server can still contain years of operational data. A stack of unused monitors and peripherals may not create a direct security threat, but they do signal process drift. When devices sit too long, teams lose chain of custody, lose resale timing, and lose clarity on what still has recoverable value.
Why businesses let this pile grow
The usual reasons are practical.
IT is focused on the next deployment, not the last one. Facilities has the space issue but not the data responsibility. Finance wants clean records. Compliance wants proof. Nobody owns the whole workflow from retirement decision to final disposition.
That gap is where problems begin.
A structured asset and recovery program closes it. Instead of asking, “How do we get rid of this stuff?” the better question is, “What is the safest and highest-value next use for each item?”
What changes when you treat it strategically
When organizations formalize this process, three things happen:
- Data risk drops: Devices stop sitting around with unknown status.
- Value becomes visible: Equipment gets evaluated for resale, reuse, or component harvesting instead of blanket scrapping.
- Reporting improves: Leadership gets documentation rather than assumptions.
A useful way to think about it is this. Disposal ends the conversation. Recovery manages the final chapter correctly.
Teams looking at this issue through an operational lens often start with an asset recovery program because it forces a practical review of what the business is holding, what it can recover, and what needs certified destruction.
Tip: If a device is important enough to appear on a purchase order, it is important enough to have a documented end-of-life path.
Understanding IT Asset Disposition and Recovery
A lot of confusion comes from treating recycling, disposal, and ITAD as if they mean the same thing. They do not.
If you manage an old building, you have two broad choices. You can tear it down and haul away the debris. Or you can inspect it, remove hazards, salvage useful materials, preserve what still has value, and document the work. That second path is much closer to IT asset disposition.
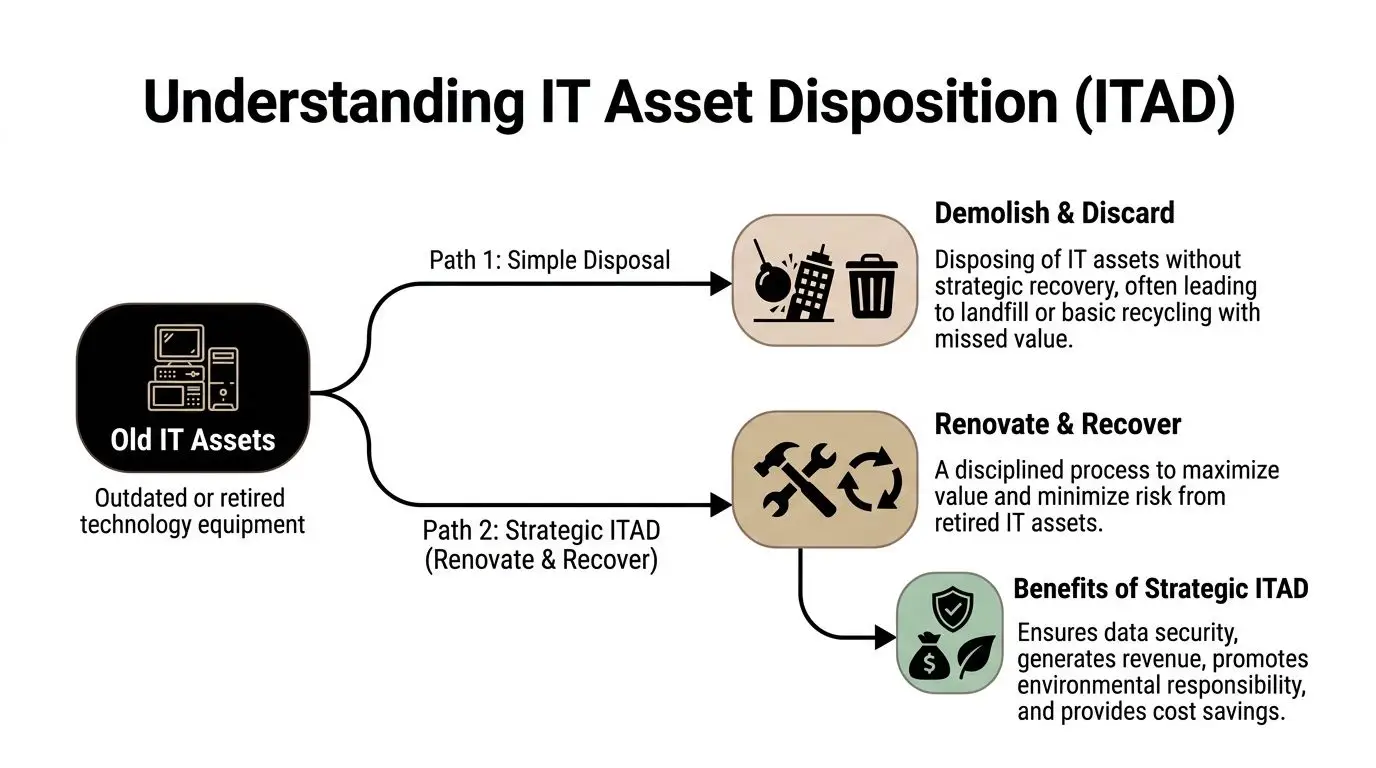
Disposal is the narrow view
Simple disposal asks one question. How do we get this equipment out of the building?
That may remove clutter, but it does not automatically solve data governance, financial recovery, audit evidence, or downstream environmental handling. It also creates a blind spot. Once a device leaves your site without a disciplined process, your options shrink fast.
ITAD is the broader business process
IT asset disposition is the managed process for retiring IT equipment in a way that addresses:
- Security
- Compliance
- Value recovery
- Environmental responsibility
- Documentation
A mature program starts before pickup day. It begins when the organization decides an asset is nearing retirement and needs a controlled path out of active service.
For readers who manage buildings, fleets, or mixed infrastructure, the logic overlaps with broader Asset Lifecycle Management practices. The same principle applies. The more disciplined the lifecycle, the fewer surprises at the end.
Asset recovery is the value engine inside ITAD
Many B2B teams miss the opportunity here.
Asset recovery is the part of the process that asks, “Can this device be repaired, refurbished, redeployed, remarketed, or harvested for parts?” It does not ignore recycling. It treats recycling as the last responsible option after higher-value uses have been considered.
That distinction matters.
A retired laptop with cosmetic wear but solid internal components should not be treated the same way as a damaged device with no practical second life. A rack server with no internal reuse case may still have resale value in secondary channels. Drives may need destruction, while the chassis and memory remain marketable.
A plain-language comparison
| Approach | Main question | Typical result |
|---|---|---|
| Basic disposal | How do we remove it | Fast exit, limited visibility |
| Recycling only | How do we process the material | Responsible material handling, but often missed residual value |
| ITAD with asset recovery | What is the safest highest-value path for each asset | Better control, better reporting, stronger value capture |
Some teams need a simple explainer before they build policy. A practical starting point is this overview of what IT asset disposition means, especially if your stakeholders still think this is only a recycling issue.
Key takeaway: ITAD is not the act of throwing old equipment away responsibly. It is the act of managing retired technology like a business asset until the very end.
The Dual Benefits of a Smart Recovery Program
The strongest ITAD programs get support from two groups that do not always agree on priorities. Finance cares about return and risk. Sustainability cares about responsible outcomes and measurable diversion. A smart recovery program serves both.
The financial case is stronger than many teams expect
A common mistake is to assume used equipment has little or no remaining value. That is sometimes true, but often only after the business has waited too long, mixed everything together, or skipped triage.
According to Unduit, a well-implemented IT asset recovery strategy can elevate recovery rates from near zero to 80-90%, and one example showed that reselling 120 laptops at $175 each yielded $21,000, while redeploying parts added $18,000 in cost avoidance (Unduit IT asset recovery). That single example is useful because it shows two different value channels. Direct resale is only one of them. Internal redeployment also matters.
For a CFO, the takeaway is simple. The question is not whether every retired device has value. The question is whether the organization has a process that can identify value before it disappears.
Security risk has a dollar value too
The second financial benefit is less visible but often more important. A managed program reduces the chance that old assets leave the company with recoverable data, incomplete inventory records, or unclear custody.
That is why recovery strategy should sit close to incident prevention strategy. If your team also deals with damaged media or unexpected failures, this guide to failed hard drive data recovery is useful context. It highlights a point IT leaders know well. Storage devices remain sensitive long after a machine is “done.”
Sustainability is not separate from operational discipline
The ESG side of ITAD is often presented as a brand story. It is more concrete than that.
A disciplined program keeps devices out of unmanaged disposal channels, supports reuse where appropriate, and makes recycling the endpoint for equipment that has no higher use. That supports internal sustainability goals, but it also improves process quality. Organizations that know what they retired, how it was handled, and what was recovered usually have better governance overall.
Social impact can be part of the recovery model
There is also a human side that many procurement teams overlook.
When an organization works with a donation-based recycling or social enterprise recycling model, some eligible devices can support technology access, digital inclusion, or workforce-oriented community programs rather than disappearing into an anonymous waste stream. That does not replace security controls. It depends on them. But it does expand the outcome from “disposed” to “put to beneficial use.”
Why these two benefit categories belong together
Too often, businesses separate the conversation:
- Finance asks about resale proceeds.
- IT asks about data destruction.
- Sustainability asks about landfill diversion.
- Community relations asks about donations.
A mature asset and recovery strategy combines those into one operating model. It is easier to approve, easier to report on, and easier to defend in front of leadership when all four outcomes are managed together.
Practical view: If your current process can remove old devices but cannot show value recovered, data destroyed, and final disposition records, you do not have a full recovery program yet.
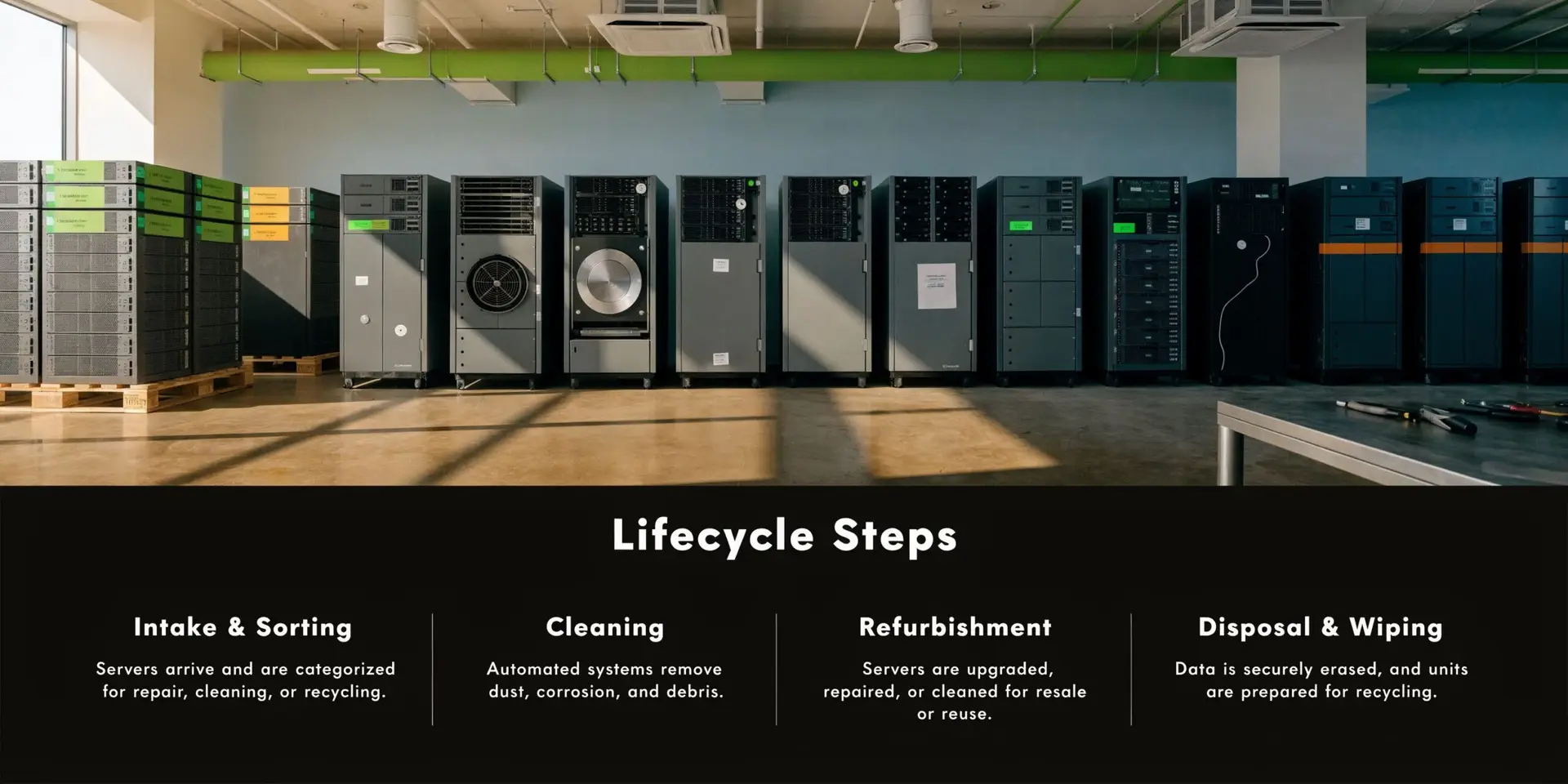
The Core Processes of the ITAD Lifecycle
Good ITAD is not one pickup. It is a chain of decisions.
If one link is weak, the rest of the program becomes harder to trust. That is why mature teams map the lifecycle from retirement notice to final reporting. When clients ask what a professional asset and recovery workflow should look like, I break it into five parts.
Start with an asset audit
Before anything leaves the site, the business needs a clean record of what it has.
That means serial numbers, device type, condition, location, and ownership status. If equipment came from multiple projects or departments, the audit should reconcile those differences before decommissioning begins. At this stage, organizations often discover orphaned gear that nobody had formally retired.
An audit does two jobs at once. It protects chain of custody, and it creates the baseline for financial recovery analysis.
Decommissioning and logistics need control
Once assets are identified, they need a secure path out of service and out of the facility.
Some equipment requires sign-off from IT, some from facilities, and some from department owners. Servers may need formal shutdown sequencing. Networked devices may need account removal or configuration reset. Then comes physical handling, staging, packing, and transport.
A professional chain of custody should answer these questions clearly:
- Who released the assets
- When they were collected
- How they were packaged or secured
- Who transported them
- What happened at intake
If your organization wants a practical view of how these handoffs fit together, this article on the lifecycle of IT equipment from acquisition to recycling gives a useful operational frame.
Data destruction is not optional
Many teams oversimplify this part.
Deleting files or reformatting a drive is not the same as data sanitization. Professional ITAD programs use recognized standards to determine whether media should be wiped, purged, degaussed, or physically destroyed.
Lenovo notes that professional ITAD mandates the NIST SP 800-88 standard for data sanitization, which can involve overwriting media 3-7 times to eliminate forensic recovery risks, and that improper disposition exposes an estimated 70% of enterprises to data leaks (Lenovo asset recovery services). That matters most in regulated sectors, but every business should treat it seriously.
The main sanitization paths
| Method | Best use case | Business reason |
|---|---|---|
| Wiping or overwriting | Reusable storage media | Preserves resale or redeployment path |
| Degaussing | Certain magnetic media | Reduces reuse potential but destroys magnetic data patterns |
| Physical shredding or destruction | End-of-life media or high-sensitivity assets | Strong assurance when reuse is not appropriate |
A good provider does not default every item to destruction. That may feel safer, but it can erase recoverable value. The right method depends on the media type, the data sensitivity, and whether the asset still has a second-life path.
Tip: Ask for serialized certificates of destruction or sanitization records, not just a generic statement that “data was removed.”
Triage determines highest and best use
Once data is secured, the equipment should be sorted by realistic outcome.
Some devices can be refurbished and sold. Some can be redeployed internally. Some should be broken down for usable parts. Others belong in responsible electronics recycling because their age, condition, or economics make further recovery impractical.
This triage step is where experienced operators separate a recovery program from a clearance event. They evaluate condition, marketability, component value, and downstream handling.
Final reporting closes the loop
The process is not finished when the truck leaves or when the drive is shredded.
The last step is documentation. That includes inventory reconciliation, downstream disposition status, destruction records, and financial recovery reporting where applicable. Without that final package, leadership is left with activity but not proof.
For business owners and IT managers, that proof is what turns ITAD from a maintenance chore into a managed control.
Navigating Compliance and Security Minefields
A surprising number of businesses have a written policy for buying technology and a vague habit for retiring it. That imbalance creates legal and operational exposure.
End-of-life devices sit at the intersection of privacy, records management, and environmental responsibility. If your company handles patient data, financial records, employee information, legal files, or customer account details, retired hardware is not just used equipment. It is regulated media until proven otherwise.
The laws matter, but the business question is simpler
Different regulations create different obligations. Healthcare organizations think in HIPAA terms. Companies with international data flows watch GDPR. Public companies and finance teams may also care about controls, retention, and evidentiary integrity.
The practical question is this. Can you prove what happened to the data and the device?
If the answer is no, your organization is depending on trust where it should be depending on records.
A useful operational reference is this article on the growing importance of data security in IT asset disposition. It frames the issue correctly. Data security at retirement is not an afterthought. It is part of the asset’s lifecycle.
Why frameworks matter
A strong framework changes behavior because it defines process, ownership, and evidence.
The UK’s asset recovery system recovered £284.5 million from criminal proceeds in the financial year ending March 2025, according to the UK government, and the same source notes that global e-waste is projected to reach 82 million tons by 2030 (UK asset recovery statistics). The parallel for ITAD is not legal equivalence. It is operational discipline. Frameworks work when they make recovery, restraint, and documented control part of the system.
What organizations should demand from a provider
Not every recycler is equipped for compliance-driven ITAD. Businesses should ask direct questions.
- Auditability: Can the provider produce serialized records tied to the assets you released?
- Custody controls: Is there a documented chain from pickup through processing?
- Data handling: Which sanitization or destruction methods are used, and when?
- Environmental handling: How are non-recoverable assets processed downstream?
- Reporting: Will your team receive documentation that stands up in an internal or external review?
Risk transfer only happens when proof exists
Some leaders assume that once equipment leaves the building, the risk leaves with it. That is incomplete.
Risk transfer only becomes credible when the provider has the process, documentation, and controls to support it. If they cannot show what happened to each category of asset, your business still owns the uncertainty.
Key takeaway: In ITAD, the biggest security failure is not always a breach. It is the inability to prove that no breach path remained.
Measuring Success with KPIs and ROI in Your ITAD Program
If leadership only sees invoices, your ITAD program looks like overhead. If leadership sees measured recovery, documented avoidance, and clear compliance outputs, the same program looks strategic.
That shift starts with the right metrics.
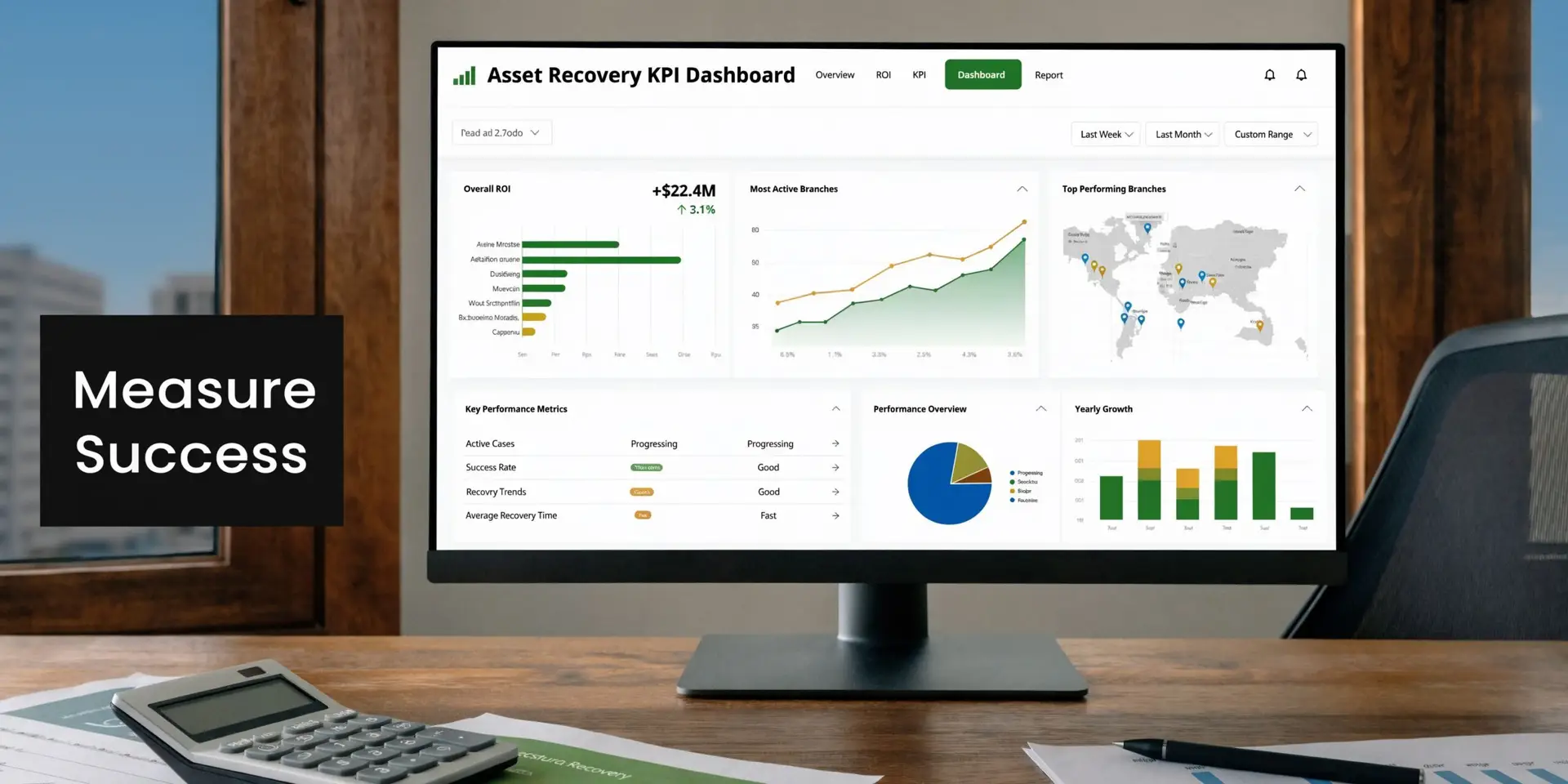
Focus on a small KPI set first
Many teams do not need a huge dashboard. They need a useful one.
Start with a handful of indicators that connect directly to business outcomes.
Recovery rate
This shows how many eligible assets were recovered through resale, reuse, or redeployment rather than lost to poor tracking or unmanaged disposal.
Net value recovered
This is the money brought back through remarketing plus any documented buyback proceeds, minus direct processing costs that your finance team attributes to the program.
Cost avoidance
Redeployed equipment matters. If a business reused viable systems or components instead of buying new replacements, that avoided spend belongs in the program story.
Certificates and reconciliation
Track how many serialized data destruction records and inventory reconciliation records were completed. This is not glamorous, but it is one of the clearest signs of process maturity.
Diversion and final disposition
Sustainability leaders will want to know how much equipment was reused, recycled responsibly, or otherwise kept out of unmanaged disposal channels.
Why measurement matters
The OECD notes that developing countries lose an estimated US$20-40 billion annually to corruption and that less than 1% of illicit financial flows are ever recovered (OECD report on stolen asset recovery). For ITAD, the lesson is straightforward. Value that is not actively traced and recovered usually disappears.
That same logic applies inside a business. If nobody measures recoverable assets, resale timing, or redeployment savings, the organization should assume value leakage is happening somewhere.
A simple ROI mindset
You do not need a complex model to explain this internally. Use a straightforward framework.
| ROI component | What to include |
|---|---|
| Value in | Resale proceeds, buyback credits, documented reuse benefits |
| Value protected | Reduced exposure through secure handling and destruction records |
| Costs avoided | Deferred purchases through redeployment |
| Program costs | Pickup, processing, logistics, internal labor if tracked |
Tip: When presenting to leadership, put financial recovery and compliance evidence on the same page. Decision-makers approve faster when risk and return are shown together.
Implementing Your Strategy with Reworx Recycling
Most companies do not fail at asset and recovery because they disagree with the goal. They fail because the work is fragmented.
IT tracks one list. Facilities stages another. A local recycler handles some items. A shredding vendor handles drives. Someone donates a few devices informally. Months later, nobody has one clean record of what happened.
A better implementation model is simpler.
Build the policy before the event
Your organization needs a written rule for when assets move from active use to retirement workflow. That policy should define ownership, approval steps, data handling requirements, and documentation standards.
The policy should also separate categories clearly. Laptops, servers, phones, networking gear, lab devices, and storage media do not all move through the same path.
Choose a partner that can support the full workflow
An organization can support the full workflow. Provider selection matters in this regard.
A practical option for businesses building that workflow is implementing an IT asset disposition strategy. In that context, Reworx Recycling provides services tied to common program needs such as business pickups, secure data destruction, electronics recycling, and asset recovery support.
Use reporting to improve the next cycle
The best ITAD programs get sharper over time.
A provider relationship should give you more than removal. It should generate inventory insight, trend visibility, and enough reporting to tighten refresh timing and retirement decisions on the next round. That is where newer tools can help. One cited industry source says AI-driven lifecycle modeling can boost asset recovery value by up to 25%, yet only 15% of SMBs are using such tools (asset recovery innovations and trends). Even if your team is not ready for advanced modeling, the takeaway is clear. Better visibility improves recovery decisions.
Keep the model grounded
A strong program usually follows these rules:
- One intake process: Every retired asset enters the same documented workflow.
- One evidence standard: Data destruction and disposition records are consistent.
- One review cadence: Leadership sees results at regular intervals.
- One decision logic: Reuse first where appropriate, then remarketing, then recycling.
That is how asset and recovery stops being a cleanup project and starts working like an operating discipline.
If your business is holding surplus laptops, retired servers, storage media, office electronics, or mixed e-waste, Reworx Recycling offers a practical next step. You can use their educational resources to shape policy, schedule a pickup for business equipment, explore secure data destruction, or build a donation-based recycling and ITAD workflow that supports compliance, value recovery, and community impact.