A lot of Denver businesses arrive at the same point the same way. An office refresh happens, a server room gets cleaned out, a merger leaves duplicate hardware behind, or a department accumulates retired laptops in a closet because no one wants to be the person who guesses wrong about data security.
That pile of electronics isn’t just surplus equipment. It’s a mix of compliance exposure, operational drag, and missed value. If your company handles customer records, employee data, financial files, health information, or proprietary work product, every retired device needs a documented end-of-life path.
Corporate Electronics Recycling in Denver works best when you treat it as a business process, not a junk removal task. The companies that do this well usually connect three goals at once: risk control, sustainability, and community impact. That’s also why donation-based recycling has become a more serious conversation for IT managers, operations leaders, and sustainability teams. A disciplined program can reduce storage headaches, support reporting needs, and turn retired equipment into something more useful than scrap.
Navigating Denver's E-Waste Landscape for Businesses
A Denver business can accumulate e-waste faster than expected. Laptops from onboarding cycles, monitors from hybrid work transitions, networking gear from upgrades, old mobile devices from security policy changes, and specialty equipment from labs or clinics all tend to linger longer than they should. The delay is usually not about intent. It’s about uncertainty over who owns the decision and what “proper disposal” requires.
That uncertainty matters more in Colorado than many businesses realize. The state’s electronics landfill restrictions changed the baseline years ago, and the volume challenge hasn’t gone away. Colorado’s statewide electronics diversion reached about 17,000 tons in 2018 and fell to nearly 12,000 tons by 2023, a 29% drop, according to Rocky Mountain PBS reporting on Colorado electronic recycling. For Denver companies, that decline is a practical signal. More devices are entering retirement cycles, but fewer are moving through formal diversion channels.

Why the closet full of devices is a business issue
Stored electronics create problems in layers.
- Security exposure: Old laptops and drives often still contain credentials, cached files, and regulated data.
- Compliance risk: Disposal decisions can affect industry obligations and internal audit readiness.
- Space and process drag: Facilities and IT teams lose time managing dead inventory.
- Brand inconsistency: A company can talk about sustainability publicly while handling obsolete equipment informally behind the scenes.
A mature recycling program fixes more than one problem at once. It gives IT a repeatable disposition process, gives legal and compliance teams an audit trail, and gives leadership a credible environmental story that isn’t built on vague claims.
Denver businesses benefit from treating recycling as ITAD
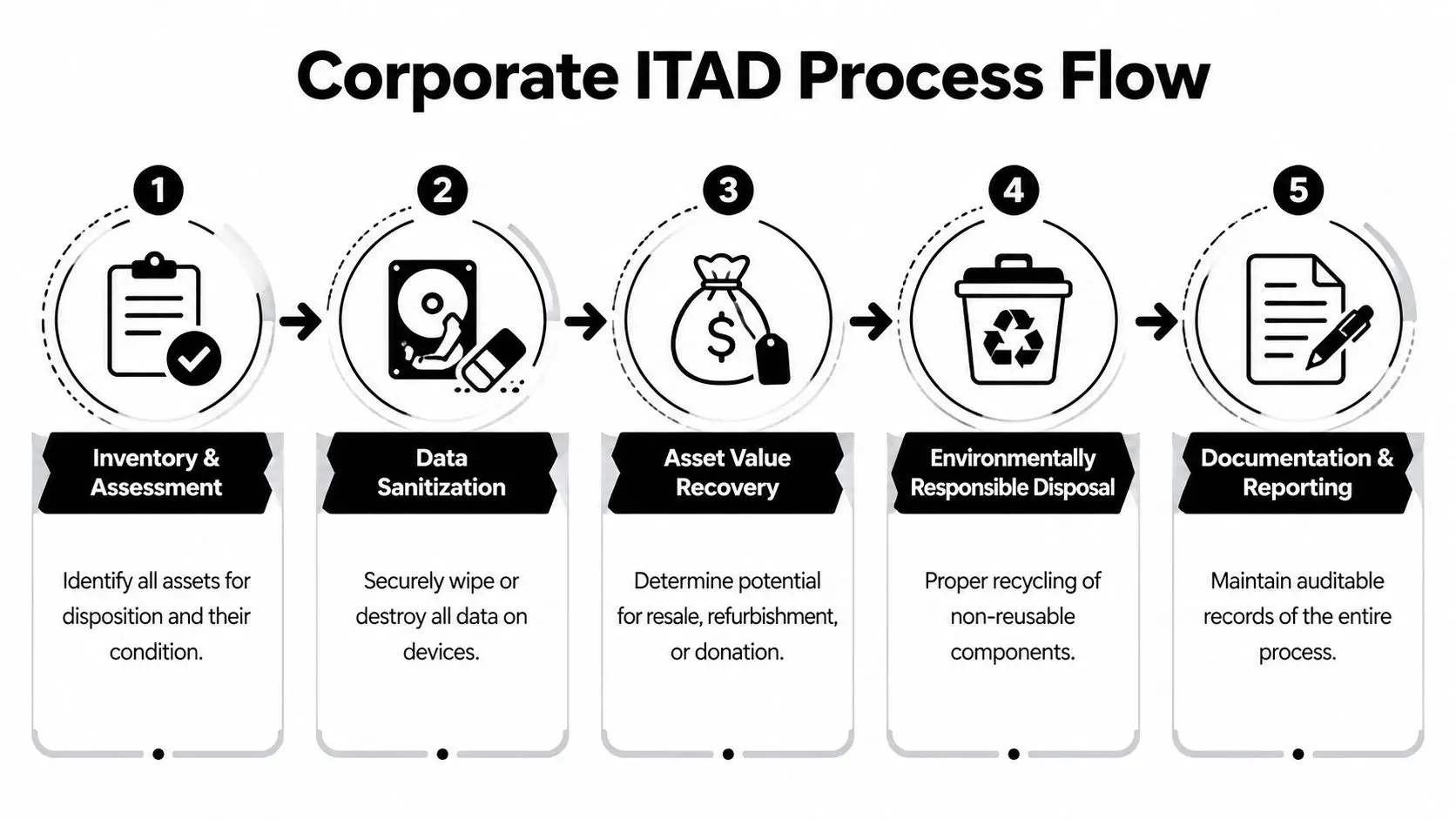
The right framing here is IT asset disposition, not trash hauling. ITAD forces better decisions around inventory control, secure data destruction, remarketing, donation, and downstream recycling. It also helps separate devices that still have use from devices that belong in certified deconstruction streams.
Practical rule: If a device ever stored business data or connected to your network, it shouldn’t leave your control without a documented disposition decision.
That’s where donation-based models can add value. Instead of seeing every retired asset as waste, businesses can evaluate whether equipment is suitable for refurbishment, donation, or responsible materials recovery. For teams comparing local options, Denver-area electronics recycling services in Colorado can help frame what a business-focused program should include beyond a simple drop-off.
What works in practice
The companies that handle this well usually do a few things consistently:
| Approach | What happens |
|---|---|
| Ad hoc cleanout | Devices sit too long, ownership stays unclear, and records are incomplete |
| Facilities-only disposal | Pickup may happen, but data, chain-of-custody, and asset tracking are often under-scoped |
| IT-led ITAD program | Inventory, data handling, logistics, and reporting stay tied together |
| CSR-aligned donation program | The company gets compliance structure plus a stronger community narrative |
Denver’s business culture tends to reward companies that can connect operational discipline with visible community benefit. Electronics recycling is one of the few back-office processes where that connection is immediate. Handle it well, and you reduce risk while demonstrating that your sustainability claims reach the loading dock.
Decoding Denver's E-Waste Compliance and Liability
Compliance failures in electronics recycling usually don’t start with bad intent. They start with assumptions. A business assumes the hauler is certified, assumes deleted files are gone, assumes a contract shifts liability, or assumes a “free recycling” offer covers the whole downstream chain.
Those assumptions don’t hold up well when a regulator, auditor, customer, or insurer asks for documentation.
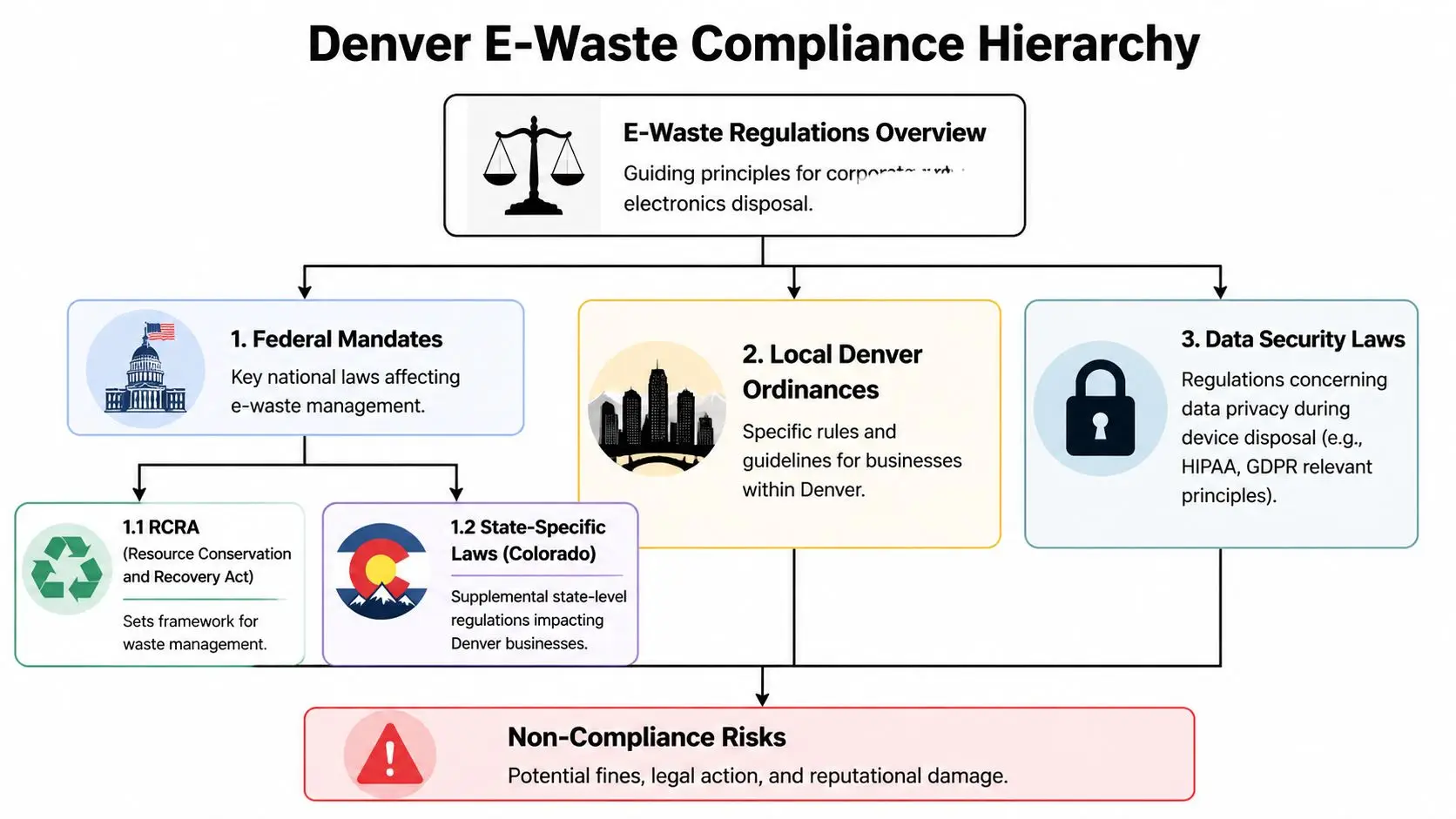
What Colorado law means operationally
Colorado’s Electronic Recycling Jobs Act (SB 12-133) bars covered electronics from landfills. The devices called out in the verified background include computers, monitors, TVs, printers, and smartphones. For a Denver business, that means end-of-life electronics can’t be treated like routine solid waste.
The legal point is simple. You need a defensible disposition path for covered devices. The operational point is more demanding. You need to know who handled the asset, how it was transported, how data was destroyed or sanitized, and where the material ultimately went.
Liability doesn’t disappear when you hire a recycler
Many programs fall short in addressing the rigorous requirements for Denver-area businesses in regulated sectors. These businesses carry specific compliance burdens, and liability can remain with the generator if due diligence is weak or a recycler’s status changes during the contract term. The City and County of Denver materials highlighted that risk directly, noting that proper contract language and audit trail documentation matter if a recycler fails certification mid-contract. See Denver guidance on electronic recycling and related compliance considerations.
That issue is bigger for healthcare, finance, education, government, and any business managing sensitive employee or customer information. Certification badges on a website aren’t enough. You need records, contract protections, and a way to verify that the service you bought is the service being performed.
A recycler’s certification can support your compliance posture. It does not replace your company’s duty to verify process, documentation, and downstream control.
For a practical overview of those stakes, the environmental and legal impacts of improper commercial e-waste disposal lays out why businesses should treat end-of-life electronics as a governed workflow.
The due diligence checklist that matters
A procurement team should ask for more than a quote. Start with documentation.
- Ask for current certification evidence. If a vendor references R2, e-Stewards, NAID-related services, or data destruction standards, request documentation and effective dates.
- Review chain-of-custody practices. You want to know when assets are tagged, who signs at pickup, and how transfers are recorded.
- Check contract language around certification loss. If a recycler loses accreditation, your company needs a defined remedy.
- Require reporting samples. Certificates of recycling, destruction records, serialized inventories, and pickup logs should be available in a usable format.
- Clarify downstream handling. A primary vendor should be able to explain where materials go after initial processing.
What compliance looks like inside the business
The recycler is only one side of the equation. Internal controls matter just as much.
- Procurement should vet certifications and insurance.
- IT should approve sanitization and destruction rules by asset type.
- Compliance or legal should review contract language and retention of records.
- Facilities should control staging and pickup access.
- Department leaders should be prevented from using side-door disposal methods.
Common failure points
A few patterns repeatedly create exposure:
| Failure point | Why it creates risk |
|---|---|
| Unlogged office cleanouts | Devices leave the building with no asset-level record |
| Shared collection bins | It becomes hard to prove what was included and who handled it |
| Informal employee take-home practices | Data control and ownership become murky fast |
| Vendor selection based only on “free” | Price obscures questions about security, transport, and downstream documentation |
The safest Denver programs are boring in the best way. They rely on written workflows, controlled pickups, auditable records, and contracts that assume something can go wrong. That’s what makes the program defensible if it ever gets examined.
Your Step-by-Step IT Asset Disposition Plan
Most first-time business recycling programs fail because they start with removal instead of planning. A truck gets scheduled before the company knows what it owns, what still has value, what requires destruction, and what records must survive after the hardware is gone.
A workable ITAD plan starts upstream. The objective isn’t just to empty a room. It’s to move assets through a controlled sequence that protects data, captures value where appropriate, and produces records your business can use later.
Start with inventory, not pickup
The best first move is a structured asset audit. Build a list by device type, serial number, location, owner department, and disposition category. Include standard office hardware, but also look for less obvious assets such as phones, docking stations, networking gear, AV systems, point-of-sale equipment, lab devices, and medical-adjacent electronics if your facility uses them.
A formal ITAD process using serialized tracking can achieve over 95% accuracy in asset recovery, and certified deconstruction by R2 or e-Stewards technicians can reach a 98% landfill diversion rate, compared with 70% for uncertified operations, according to the executive summary cited here.
That difference matters. If your inventory is weak at the front end, every later control gets weaker too.
Assign each asset to a clear path
Once inventory exists, divide equipment into disposition lanes. Don’t overcomplicate it.
| Asset lane | Typical decision |
|---|---|
| Reuse internally | Hold for redeployment after testing and sanitization |
| Remarket | Sell or recover value from working business-grade hardware |
| Donate | Transfer suitable equipment through an approved program |
| Recycle | Deconstruct end-of-life equipment responsibly |
| Destroy | Apply for devices or components that require physical data destruction |
This is also where organizations should define who decides. IT usually judges technical condition. Compliance sets handling rules for sensitive devices. Finance may want input on any resale or write-off treatment. Sustainability may need reporting outputs.
Build logistics around your real operating pattern
Not every company needs the same collection model. A law office with one annual refresh doesn’t need the same workflow as a multi-site healthcare group or a company closing a floor.
Three common models work well:
- One-time office cleanout: Best for relocations, lease exits, and major upgrades.
- Recurring pickup schedule: Better for organizations retiring smaller batches throughout the year.
- Project-based decommissioning: Used when data center, lab, warehouse, or specialized equipment is involved.
Field note: The easiest programs to sustain are the ones that fit normal operations. If your process requires managers to invent a new approval path every quarter, people will bypass it.
For Denver businesses that want a business-focused service model, IT asset disposition support in Denver is an example of the kind of structured pickup, tracking, and disposition workflow companies should look for when comparing providers.
A practical rollout sequence
You don’t need a huge committee to launch this. You do need ownership. A simple rollout usually looks like this:
- Choose an internal owner. This is usually IT, operations, facilities, or a cross-functional lead.
- Map the asset universe. Pull procurement records, endpoint management exports, and department-held surplus lists.
- Set disposition rules. Decide what gets wiped, shredded, donated, remarketed, or recycled.
- Define staging and pickup controls. Pick where assets sit before transport and who can release them.
- Require documentation. Inventory reports, pickup records, destruction records, and final recycling reporting should all be retained.
- Run a pilot. One office, one department, or one refresh cycle is enough to expose process gaps.
What small, mid-sized, and complex environments each need
The structure should change with scale.
Small business office
A smaller Denver firm usually needs straightforward controls: one inventory sheet, one approved disposition workflow, and one pickup process. The biggest risk is informality. Employees often mean well and still create exposure by taking devices home, dropping them at retail locations, or moving them without records.
Mid-sized multi-department operation
This environment needs governance more than volume handling. Different teams will retire equipment at different times, so recurring pickups and a standing approval process matter more than a once-a-year purge.
Enterprise, healthcare, lab, or data-heavy environment
These organizations should expect more complexity around chain-of-custody, access control, destruction standards, and segmented handling. A monitor doesn’t require the same treatment as a server drive, and a standard laptop doesn’t always move through the same approvals as a device from a regulated workflow.
What works and what doesn’t
A short comparison makes the trade-offs clear.
| Works | Doesn't work |
|---|---|
| Serial-level tracking | “Approximate” box counts |
| Department signoff before pickup | Surprise cleanouts |
| Defined asset lanes | One bucket for everything |
| Written data destruction rules | Case-by-case guesses |
| Scheduled collection rhythm | Waiting until storage overflows |
The strongest ITAD plans are not complicated. They are disciplined. If your business can account for how it buys technology, it can also account for how it retires it. That’s the standard worth building to.
Ensuring Secure Data Destruction for Corporate Assets
A surprising number of businesses still confuse basic file deletion with real data destruction. From a security standpoint, that’s a major mistake. Deleting folders, reformatting a drive, or sending equipment to surplus storage without a documented sanitization step leaves your company exposed long after the device is gone.
Data destruction is the control that turns electronics recycling from a facilities task into a security process.
When wiping works and when shredding is better
Two methods dominate business ITAD workflows: software sanitization and physical destruction.
Software wiping is appropriate when a device may be reused, resold, or donated after sanitization. In verified guidance for this article, secure processes that follow NIST 800-88 for software wipes and NSA standards for physical shredding to 2mm particles can achieve a data breach prevention rate exceeding 99.99%. The same verified source notes that behavioral non-compliance, where employees mishandle devices, accounts for up to 40% of security incidents, based on the secure data destruction overview here.
Physical shredding is the stronger fit when devices contain highly sensitive data, the drive state is unknown, the media is damaged, or internal policy requires irreversible destruction.
The real failure point is often people
Most organizations focus on tools first. The tool matters, but people usually create the bigger problem.
- A retired laptop sits under a desk for months.
- An employee moves old phones into an unlabeled box.
- A branch office ships devices without chain-of-custody paperwork.
- A manager assumes factory reset equals full sanitization.
That’s why written policy has to match technical method. If your team doesn’t know which assets require wiping, which require shredding, and who signs off before release, your controls won’t hold.
Treat data destruction as a custody problem first and a mechanical problem second. Once a device falls outside a controlled workflow, proof becomes harder.
A simple decision framework
Use this working model when setting internal rules:
| Asset type | Preferred handling |
|---|---|
| Reusable business laptops and desktops | NIST-aligned wipe, verification, then release |
| Failed or inaccessible drives | Physical destruction |
| Server drives from sensitive environments | Physical destruction with documentation |
| Mobile devices | Policy-driven reset plus documented handling through approved workflow |
| Unknown or mixed media lots | Segregate first, then sanitize or destroy by media type |
For employee-issued phones, it helps to pair corporate policy with simple user-facing instructions before the device enters the official disposition stream. If your team needs a plain-language example of how to prep your phone for a new owner, that kind of reset checklist can support the front-end handoff. It should not replace your company’s formal sanitization and custody process.
What to require from a provider
A business should expect more than a verbal assurance that drives were destroyed.
Look for these outputs:
- Certificate of destruction: The document should tie the destruction event to the assets received.
- Method clarity: The provider should explain whether the device was wiped, shredded, or otherwise processed.
- Chain-of-custody records: Pickup and transfer documentation should be available.
- Exception handling: Failed drives and inaccessible devices should have a defined path.
- Policy alignment: Your internal rule set should match the vendor’s actual process.
The strongest programs also reduce employee improvisation. Once teams know there is one approved path for retired assets, security incidents from casual mishandling become much less likely.
Selecting Your Denver Electronics Recycling Partner
Choosing a recycling partner is not a commodity purchase. It’s a due diligence exercise. A low quote or a “free pickup” offer may sound efficient, but it doesn’t answer these questions: Who controls the chain-of-custody? Who verifies downstream handling? Who documents data destruction? Who takes responsibility if something goes wrong?
Those are the questions that separate a usable vendor from one that merely removes clutter.

The “free recycling” trade-off
The Denver market has plenty of providers advertising free electronics recycling. Sometimes that model fits. Sometimes it hides the important costs in logistics, sorting limits, special handling, or data destruction requirements. The bigger issue isn’t whether a line item says “free.” It’s whether your company understands the true operating model behind that promise.
That’s especially important for businesses that need pickup, serialized reporting, secure hard drive handling, project scheduling, or support for office cleanouts and facility cleanouts. Those needs create work. If a proposal skips detail, ask what has been omitted rather than assuming the service is complete.
The vendor questions worth asking
A short, serious review process usually reveals a lot.
Ask for process evidence
Don’t stop at marketing claims. Ask for sample chain-of-custody forms, destruction documentation, and reporting outputs. If a provider can’t show what records look like before the contract starts, that’s a warning sign.
Ask how assets are sorted
Usable laptops, broken monitors, networking gear, and mixed peripheral pallets shouldn’t all move through one generic stream. A credible provider should be able to explain the difference between reuse, remarketing, donation, deconstruction, and product destruction.
Ask about certification continuity
If a provider references R2, e-Stewards, or secure destruction standards, ask how your company will be notified if that status changes. This is one of the most overlooked contract points in business recycling.
Procurement should evaluate a recycler the same way it evaluates any vendor that touches regulated data or environmental liability. Convenience matters, but controls matter more.
Use a practical scorecard
This kind of matrix keeps selection disciplined.
| Evaluation area | What to verify |
|---|---|
| Data security | Sanitization and destruction methods, documentation, exception handling |
| Environmental process | Downstream transparency, landfill avoidance approach, deconstruction standards |
| Logistics | Pickup scheduling, site access control, multi-location capability |
| Reporting | Serialized inventory, destruction records, recycling certificates |
| Contract strength | Certification language, liability clauses, documentation requirements |
| CSR alignment | Donation pathways, refurbishment potential, community benefit model |
Why mission fit can matter in B2B recycling
For many Denver companies, vendor selection now touches CSR and ESG reporting as well as operations. That doesn’t mean choosing a partner based on branding alone. It means asking whether the end-of-life program supports the kind of company you say you are.
A donation-based or social enterprise recycling model can fit especially well when your business wants retired assets handled responsibly while also supporting digital inclusion or community reuse. That approach doesn’t remove the need for chain-of-custody or secure data destruction. It raises the bar, because the provider has to manage both compliance and mission execution credibly.
One example in this category is Reworx guidance on choosing an e-waste recycling partner, which reflects the broader criteria companies should use when screening any business-focused recycler.
What strong partnerships look like
The best vendor relationships are operational, not ceremonial. You know who your contact is. Pickup procedures are documented. Escalation paths exist. Reports arrive in a consistent format. IT, facilities, and compliance all know what to expect.
Weak partnerships look different. You get vague answers, broad promises, and little detail about what happens after the truck leaves.
If you’re comparing providers for computer recycling, secure data destruction, medical equipment disposal, laboratory equipment disposal, laptop disposal, or data center decommissioning, don’t let those categories blur together. Different asset classes create different risks. Your vendor should speak to those differences clearly.
Turning E-Waste Into Opportunity with Reworx Recycling
The strongest corporate recycling programs don’t treat retired electronics as a cleanup problem. They treat them as a controlled exit from the asset lifecycle. That shift changes the outcome. Instead of unmanaged storage, uncertain data exposure, and vague sustainability claims, the business gets a documented process with operational, environmental, and social value.
Denver already has proof that organized electronics recycling can produce meaningful impact. In one year, a certified Denver social enterprise recycler processed 11,728,961 pounds of e-waste, diverted 337,249 pounds of hazardous waste from landfills, recycled 103,317 fluorescent bulbs, and achieved a greenhouse gas reduction equivalent to 16,348,888 pounds, according to the Denver Environmental Health and Safety report referencing Blue Star Recyclers. That’s what structured, community-linked recycling can look like at real scale.
Why this matters beyond disposal
For a Denver business, the value of a mature program shows up in several places at once:
- Risk management: Fewer undocumented devices and stronger custody controls.
- Operational discipline: Clear workflows for office cleanout, facility cleanout, and routine refresh cycles.
- Sustainability credibility: Reporting that connects actual diversion activity to internal goals.
- Community impact: More thoughtful pathways for equipment that can still serve people.
That last point is where many programs can improve. A business doesn’t need to choose between security and social impact. It needs a process that sequences them correctly. Data must be handled first. Asset evaluation comes next. Donation or reuse should happen only when the device is appropriate for that lane.
A more useful CSR model
This is also why donation-based recycling deserves attention from leadership, not just facilities. If your business already supports workforce development, digital inclusion, school partnerships, neighborhood programs, or broader ESG commitments, retired technology can support those priorities when the disposition process is built correctly.
Good electronics recycling protects the business first. Great electronics recycling protects the business and leaves something useful behind for the community.
Reworx Recycling fits that conversation as a donation-based electronics recycling and IT equipment disposal social enterprise that supports pickups, secure data destruction, and business-focused end-of-life handling. For companies that want a model tied to both responsible processing and community benefit, how Reworx Recycling helps reduce electronic waste shows how that approach can align with a broader corporate program.
The practical takeaway is simple. If your company is replacing devices, closing out storage rooms, decommissioning equipment, or formalizing ITAD for the first time, don’t frame the work as disposal alone. Build a process your security team can trust, your compliance team can defend, and your leadership team can stand behind.
If your business is ready to move old equipment out of storage and into a documented, responsible end-of-life process, connect with Reworx Recycling. You can use that partnership to plan a pickup, support a donation-based recycling program, and build a Corporate Electronics Recycling in Denver workflow that protects data, supports sustainability goals, and turns surplus technology into community value.