Your storage room fills up fast after a tech refresh in New York City. Old laptops sit beside retired switches, a copier nobody wants to touch still has a hard drive inside, and a stack of failed SSDs is now both a data risk and a facilities problem.
That’s when many teams search product destruction near me and get results built for residential drop-offs or paper shredding. For a business, especially one handling customer records, financial data, health information, or proprietary designs, that search usually doesn’t answer the core question. You don’t just need disposal. You need documented control, defensible data destruction, and a path that doesn’t dump avoidable material into the waste stream.
Navigating Your Search for Product Destruction in NYC
A local search sounds simple. In practice, NYC businesses are sorting through vendors that do very different work under the same label.

Why search results often miss the business problem
A lot of listings for product destruction near me are really about paper, household hazardous waste, or one-off hard drive crushing. Those services can be useful, but they’re not the same as IT asset disposition (ITAD).
For business use, the issues are broader. You need to know whether the vendor can track serialized assets, handle chain of custody, identify hidden storage in devices like printers and copiers, and document destruction in a way your legal, compliance, and audit teams can use.
The gap is real. A 2025 EPA report cited in market coverage says U.S. businesses generated 6.9 million metric tons of e-waste in 2022, while only 25% of SMBs report using certified ITAD services, and average data breach risk is cited at $4.88 million per incident. The same source also notes that existing online content often fails to address business compliance needs around standards like NIST 800-88 (business e-waste and ITAD coverage).
What a NYC business should screen for first
Start by separating vendors into three buckets:
- Basic destruction providers who can destroy a small set of media but don’t run full audit trails.
- Recycling operators who move material responsibly but may not specialize in regulated data workflows.
- Certified ITAD-focused partners who combine inventory, sanitization, transport controls, destruction, and reporting.
In NYC, volume and density make that distinction more important. You may be clearing one floor, one clinic, one branch office, or one cage in a colocation environment. Each has different risks.
Working rule: If the vendor can’t explain chain of custody before pickup, they probably shouldn’t touch your assets.
A practical first step is to review local service expectations through a business-focused electronics recycling resource such as NYC electronics recycling options. Then ask whether the vendor’s process starts with inventory and ends with verifiable documentation, not just a truck and a promise.
Decoding Product Destruction Types and Services
“Product destruction” covers several jobs that people often lump together. That creates bad scopes, bad pricing, and bad outcomes.
Not every destruction job is an ITAD project
If you’re clearing banker boxes of records, you need document shredding. If you’re retiring backup tapes, failed drives, and decommissioned laptops, you need secure media destruction. If you’re closing a satellite office or replacing racks of hardware, you need full ITAD.
Those are not interchangeable services.
A proper destruction workflow starts with triage. The goal is to identify what should be reused, what should be refurbished, what must be sanitized, and what needs physical destruction. Research on product destruction methodology notes that a complete process should prioritize repair and reuse first, then move to destruction methods such as shredding electronics to less than 5mm particles or incineration for non-recyclables. The same research warns that liability fears can drive 60% over-destruction of items that could have been reused (product destruction methodology and over-destruction risk).
The main service categories
| Service type | Best fit | What to verify |
|---|---|---|
| Document shredding | Paper records, labeled files, archives | Secure bins, witness options, destruction record |
| Media destruction | Hard drives, tapes, SSDs, phones | Sanitization method, particle size, serialized reporting |
| ITAD | Laptops, desktops, servers, network gear, printers | Inventory, chain of custody, reuse triage, certificates |
| Brand protection destruction | Recalled, expired, damaged, or proprietary products | Proof of destruction, control against resale |
For electronics, the hidden risk is assuming “recycling” means “data-safe.” It doesn’t. A recycler may be perfectly capable on material handling and still not be the right fit for a compliance-heavy environment.
How the methods differ
Physical destruction isn’t one thing either.
- Shredding fits drives, mixed electronics, and devices that can’t be remarketed safely.
- Degaussing applies to magnetic media. It doesn’t solve every modern storage scenario.
- Incineration belongs in narrow use cases involving non-recyclables and regulated materials, not as a default answer for general office electronics.
Some businesses default to destruction for everything because it feels safer. That often leaves money, reuse opportunities, and ESG value on the table. Others swing too far the other way and try to remarket assets without properly accounting for embedded storage or product control.
The right question isn’t “Can you destroy this?” It’s “What’s the lowest-risk, highest-control disposition for this specific asset?”
If you need a plain-language breakdown of physical methods, methods for destroying old equipment gives a useful operational overview. Use that framework to scope the job correctly before anyone arrives onsite.
The Non-Negotiable Checklist for Vetting Local Vendors
The biggest mistake in product destruction isn’t choosing the wrong shredder. It’s choosing the wrong partner.
The cautionary example every NYC compliance team should know
A vendor can sound credible, show up on time, and still expose your business. The better test is whether their controls hold up under audit.
One example still gets attention for a reason. Morgan Stanley was fined $163 million after a data breach affecting 15 million customers tied to the use of a non-certified moving company for decommissioning. In the same industry analysis, certified ITAD processes are described as reducing breach risk by over 95% through audited chain-of-custody protocols (ITAD compliance failure example and chain-of-custody controls).

Questions that separate a serious vendor from a risky one
Ask these directly. If answers are vague, move on.
- How do you track each asset? You want serialized inventory, not pallet-level estimates.
- What sanitization standards do you follow? For many businesses, NIST 800-88 is the practical baseline.
- How is chain of custody documented? Handoffs should be logged from pickup through final destruction.
- What proof do you issue at the end? A Certificate of Destruction matters, but so do supporting audit records.
- What happens to non-destroyed assets? Reuse and resale paths must be controlled, documented, and approved.
- How do you handle devices with hidden storage? Printers, copiers, firewalls, and multifunction devices often get missed.
Documentation you should expect
A credible vendor should produce records that stand up internally. At minimum, most business programs should expect:
- Pickup records showing date, location, and custody transfer.
- Serialized manifests matching what left your office to what was processed.
- Destruction verification tied to specific media or asset classes.
- Disposition reporting that distinguishes destroyed, sanitized, refurbished, and recycled material.
Audit lens: If your compliance officer asked for support six months from now, could you reconstruct what happened to each asset without guessing?
For teams comparing providers, how to select a reliable e-waste recycling partner is a useful checklist. In NYC, where regulated industries often sit a few floors apart in the same building, “local vendor” should never mean “low-documentation vendor.”
Onsite vs Offsite Destruction Logistics and Timelines
The right logistics plan depends on sensitivity, volume, building constraints, and how much your team needs to witness.
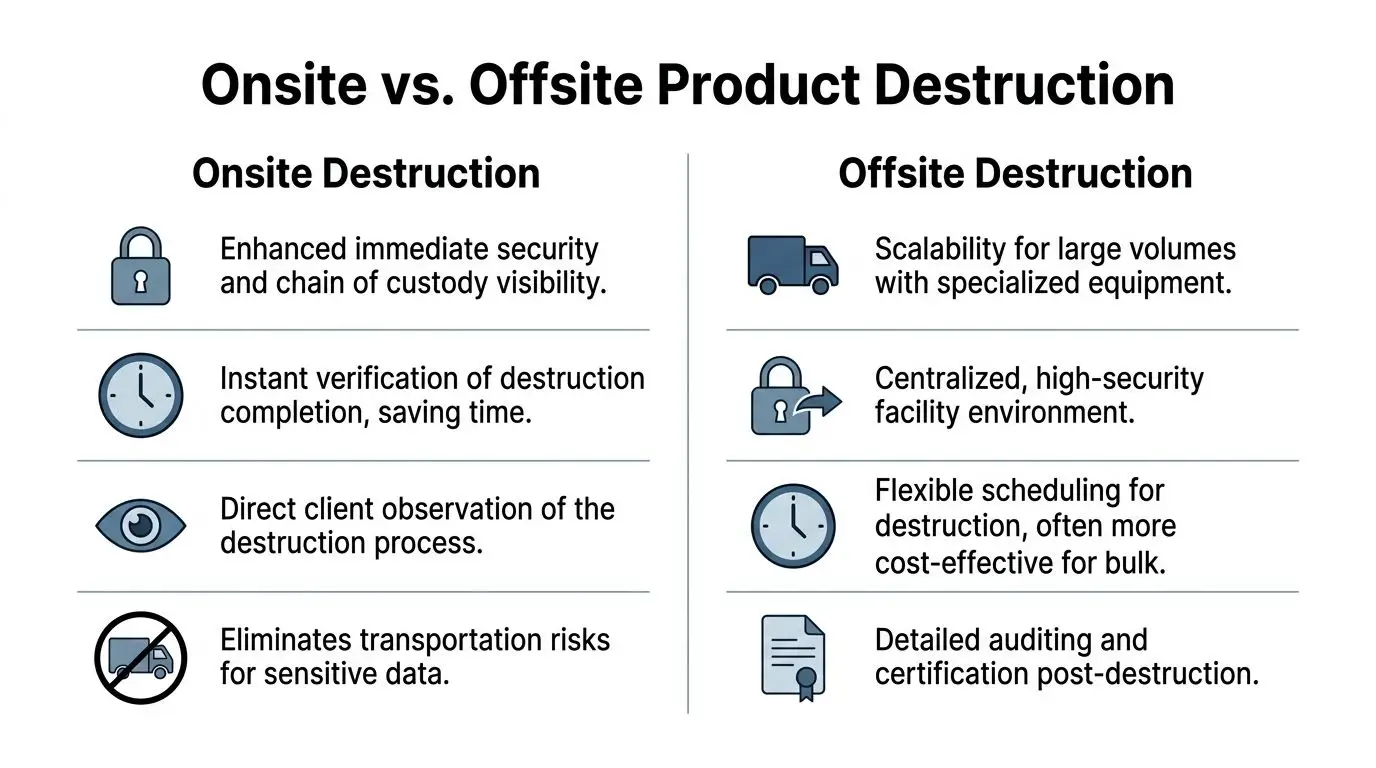
When onsite makes sense
Onsite destruction is usually the stronger option when data sensitivity is high and the business wants immediate verification. That’s common for law firms, finance teams, healthcare environments, and projects involving executive devices or high-risk media.
The advantages are straightforward:
- You maintain direct visibility while destruction happens.
- Transport risk drops because media doesn’t leave intact.
- Internal signoff can happen faster when stakeholders witness the process.
A service such as on-site hard drive destruction fits well.reworxrecycling.org/on-site-hard-drive-destruction/) fits well. It’s often used for failed drives, selective media purges, and situations where chain of custody must remain highly visible.
When offsite is the better operational call
Offsite destruction works better for bulk loads, mixed equipment, and projects that need more than a truck-mounted shredder can handle efficiently. Think office cleanouts, data center exits, school refreshes, or batches of varied hardware that need triage before final disposition.
A secure facility can support:
- more detailed sorting
- stronger reuse screening
- plant-based processing for larger volumes
- integrated recycling workflows after destruction
That doesn’t mean “less secure.” It means security depends on transport and handoff discipline.
The NYC logistics factor
In Manhattan and the outer boroughs, route planning matters. Building loading docks are limited, elevator access is scheduled, and service windows are tight.
There’s also an environmental reason to avoid sloppy logistics. Waste360’s breakdown of NYC recycling notes that diesel trucks haul Manhattan’s garbage 7.8 million miles annually, equal to 312 Earth circumferences, which is a strong reminder that localized, efficient handling matters whether destruction is onsite or moved to a secure facility (NYC hauling mileage and logistics impact).
A poorly planned pickup creates two problems at once. More exposure time for your assets and more operational waste in the process.
A practical comparison looks like this:
| Decision factor | Onsite | Offsite |
|---|---|---|
| Sensitive media | Strong fit | Good with strict custody |
| Bulk mixed equipment | Limited by truck capacity | Strong fit |
| Client witnessing | Easy | Usually indirect |
| Building disruption | Can be higher on the day | Often easier to stage |
| Reuse triage | Limited | Better supported |
For many NYC businesses, the best answer is hybrid. Destroy sensitive media onsite, then move the remaining equipment under documented custody for audit, refurbishment screening, and recycling.
Preparing Your Assets for a Secure Handover
A smooth destruction day starts with internal prep, not with the vendor pulling up curbside.
Build the inventory before pickup is scheduled
Start with a serialized asset list. Pull from your CMDB, fixed asset register, or endpoint management system, then verify physically.
Don’t stop at laptops and servers. Include copiers, printers, access control appliances, VoIP hardware, tablets, network gear, and anything else that may store data.
If an item can’t be matched to a serial number, note that before pickup. Unknown assets create chain-of-custody gaps.
Separate assets by disposition path
Don’t hand a mixed pile to the vendor and expect a clean audit trail. Stage assets into practical groups:
- media for destruction
- equipment for sanitization and reuse review
- damaged items for recycling
- specialty equipment needing separate handling
Labeling matters. So does containment. Lock bins, carts, cages, or a secured room are all better than loose staging in an open office area.
Align your internal teams before the handoff
Most delays happen because IT, facilities, compliance, and security assume someone else owns the last step.
Use a short internal checklist:
- Confirm who signs chain-of-custody documents.
- Confirm who escorts the vendor.
- Confirm which assets are approved for destruction versus evaluation.
- Confirm building access rules, elevator windows, and dock instructions.
- Confirm who receives final reporting.
If your vendor arrives before your internal approvals are aligned, the project is already off track.
Treat internal wiping as a first line, not the only line
If your policy requires software wiping before handoff, do it. That’s good practice. It also doesn’t replace vendor controls.
Devices fail. Drives disappear from inventory. Embedded storage gets overlooked. A defensible process layers your controls. Internal preparation, documented custody, and final vendor verification work together.
For large office cleanouts, keep one person responsible for exceptions. That includes unlabeled equipment, surprise finds from storage closets, and devices discovered after the main pickup window. A project loses discipline when exceptions become informal.
Beyond Destruction Sustainable ITAD with Reworx Recycling
A mature ITAD program doesn’t define success as “everything destroyed.” It defines success as “risk handled correctly, value recovered where appropriate, and waste minimized.”
Why the sustainability piece matters in NYC
New York City residents recycle only 17% of total waste, which is described as half the potential rate, and landfills nearing capacity are linked to 36% of U.S. methane emissions. That makes e-waste diversion through certified recycling and reuse especially important in an urban market where space, hauling, and disposal all come with pressure (NYC waste and recycling data).

That’s why destruction should sit inside a wider disposition strategy. Some assets need shredding. Others need sanitization, testing, resale control, donation review, or compliant recycling.
A better operating model
The strongest programs use a hierarchy:
- destroy what must be destroyed
- sanitize what can safely be redeployed
- refurbish what still has usable life
- recycle material that has reached true end of life
That approach protects data without defaulting to waste.
Reworx Recycling is one example of a provider that combines sustainable IT asset disposition services with electronics recycling, secure data destruction, pickups, and donation-oriented reuse pathways through a social enterprise model (sustainable ITAD services). For businesses, that means the disposition conversation can include compliance, environmental handling, and community benefit in one process.
Destruction closes one risk. Reuse, donation, and responsible recycling can solve three more. Waste reduction, reporting support, and social impact.
In practice, this matters for year-end refreshes, post-merger consolidations, school device turnover, healthcare equipment replacement, and office relocations. The business doesn’t just need material removed. It needs a documented outcome that supports security and corporate responsibility at the same time.
If your team is sorting through product destruction near me and needs a practical path for secure data destruction, electronics recycling, office cleanout support, or IT equipment disposal, explore the options available through Reworx Recycling. You can use their resources to plan a pickup, evaluate donation-based recycling, or build a more defensible ITAD process for your next refresh.