When Seattle companies refresh laptops, shut down a lab, or clear a floor before a move, the retired equipment usually doesn’t leave the building right away. It ends up in a storeroom, an IDF closet, or a fenced corner of the warehouse. The gear looks harmless sitting there. It isn’t.
Old endpoints still hold data. Aging servers lose resale value while they wait. Mixed piles of monitors, drives, network hardware, and specialty equipment create confusion about what can be reused, what must be destroyed, and what requires documented recycling. For healthcare groups, biotech firms, aerospace suppliers, universities, and public agencies around Seattle, that backlog is less a housekeeping issue than an unmanaged risk.
That’s why Enterprise IT Asset Disposition Services in Seattle should be treated as a governed business process, not a last-mile hauling task. The right ITAD program protects regulated data, preserves recoverable value, and gives procurement, security, facilities, and sustainability teams the same answer when auditors ask what happened to retired equipment.
Beyond the Storeroom A Strategic Approach to ITAD in Seattle
A common Seattle scenario starts with a routine refresh. IT replaces employee laptops, facilities is planning an office reconfiguration, and someone realizes the company is also sitting on old switches, a few racks of retired servers, and a shelf of failed drives from prior incidents. Nobody wants to move first because every path carries risk. If you send assets out too casually, you lose control of data and chain of custody. If you leave them in storage, the inventory gets worse every quarter.

That’s the point where disposal stops being an operational chore and becomes an executive issue. The global Enterprise IT Asset Disposition market is projected to grow from USD 8.67 billion in 2026 to USD 21.51 billion by 2034, and North America leads the market, which reflects how many organizations now rely on professional partners instead of public drop-off options for business equipment handling, according to Fortune Business Insights on the ITAD market.
Why Seattle teams get stuck
Seattle businesses often have three competing priorities:
- Security pressure: Devices may contain customer data, employee records, engineering files, or regulated health information.
- Operational pressure: Nobody wants decommissioning to disrupt production floors, clinics, labs, or office moves.
- Sustainability pressure: Leadership wants documented electronics recycling outcomes, not vague assurances.
Public e-waste programs don’t solve enterprise-grade requirements. They aren’t built around serialized intake, data destruction workflows, audit reporting, or structured pickup windows for corporate fleets of equipment.
Practical rule: If your process begins when the truck arrives, you’re already too late. ITAD starts when assets are marked for retirement.
Strategy beats cleanup
The companies that handle this well treat ITAD like inventory control in reverse. Every asset has an owner, a status, a disposition path, and a record. If your internal processes need tightening before you issue an ITAD RFP, it can help to review broader inventory management best practices and adapt the same discipline to retired technology.
That approach changes the conversation. Instead of asking, “How do we get rid of this pile?” the better question is, “How do we retire assets in a way that protects data, satisfies compliance, and captures any remaining value?” In Seattle, where companies often operate across offices, labs, and hybrid work environments, that shift matters.
A structured ITAD program also creates room for models beyond scrap disposal. Donation-based recycling can support community outcomes when devices are suitable for reuse, while still preserving formal handling and documentation standards expected in enterprise environments.
Defining Your Seattle ITAD Project Scope
Most ITAD problems start before vendor selection. They start with a vague internal brief: “We’ve got about 500 devices,” or “We need to clear our office by month-end.” That isn’t enough. Good project scoping separates a smooth disposition event from a messy one with scope creep, surprise charges, and missing assets.
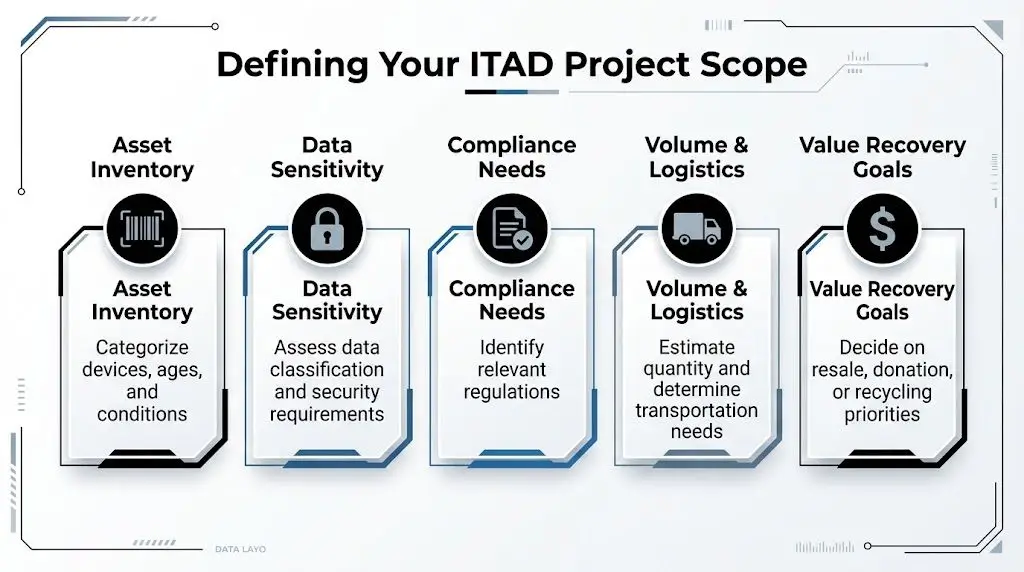
A solid scope begins with a true inventory. A successful ITAD process starts with a detailed inventory and assessment of device specifications, serial numbers, and condition, which helps determine whether assets should be reused, resold, donated, or recycled. Incomplete inventories can cause a 20-30% value loss from missed resale opportunities, as outlined in Faddom’s ITAD process and best practices guide.
Start with asset classes, not one big pile
Break the project into distinct asset groups. In Seattle enterprise environments, that usually includes more than office laptops.
User computing assets
Laptops, desktops, docking stations, monitors, and mobile devices move fast and often have mixed conditions. Some are suitable for redeployment or donation. Others go directly to recycling or destruction.Data center and infrastructure gear
Servers, storage arrays, firewalls, switches, UPS units, and rack accessories require tighter scheduling and more technical deinstallation planning.Specialized equipment
Labs, clinics, engineering teams, and manufacturing sites may hold devices with embedded storage, regulated components, or nonstandard removal requirements.Loose media and failed parts
Failed hard drives, SSDs, backup tapes, and decommissioned boards should never be treated as an afterthought. They often drive the highest security concern in the entire project.
Define the business outcome before the pickup
Different internal stakeholders care about different outcomes. Your scope should say which outcome leads.
| Priority | What it changes |
|---|---|
| Maximum security | Pushes more work toward onsite handling, drive shredding, restricted access, and stricter documentation |
| Maximum value recovery | Requires better grading, testing, and remarketing pathways |
| Fast site clearance | Prioritizes labor planning, palletization, and tight pickup windows |
| ESG and community impact | Favors documented recycling and reuse channels, including donation programs |
That alignment prevents conflict later. Security may want all drives shredded. Finance may want remarketing where feasible. Sustainability may want diversion reporting. The scope has to settle those trade-offs up front.
Choose onsite or offsite based on risk, not instinct
Many Seattle teams tend to overcorrect. Some insist every task happen onsite, which can increase complexity and cost. Others push everything offsite without enough controls.
Use this decision lens:
- Choose onsite services when assets contain highly sensitive data, deinstallation must occur in controlled spaces, or internal policy requires witnessing destruction.
- Choose offsite processing when the equipment volume is high, asset triage is labor intensive, and the provider’s facility can process, test, and report more efficiently.
- Use a hybrid model when you need onsite serial capture and media destruction, but want downstream remarketing and recycling handled at a certified facility.
If your team can’t explain why it wants onsite work, it probably wants assurance, not necessarily onsite processing. Those are different requirements.
For Seattle offices with tight loading docks, elevator restrictions, or shared building access, logistics should also be written into scope early. A downtown office cleanout needs a different plan than a suburban warehouse or a distributed regional refresh.
Build a usable project brief
Before speaking to vendors, document the following:
- Asset counts and categories: Estimated quantities by type, with notes on unknowns.
- Location details: Site access, loading constraints, security checkpoints, and staging areas.
- Data handling requirements: NIST 800-88 erasure, shredding, degaussing, or mixed methods.
- Packaging and labor needs: Whether your team will stage gear or the vendor must do deinstallation and packing.
- Disposition preferences: Resale, redeployment, donation-based recycling, or recycling only.
If you’re planning Seattle-area computer recycling as part of a broader retirement effort, Reworx outlines service considerations on its Seattle computer recycling page.
A scoped project doesn’t need to be perfect. It needs to be specific enough that competing vendors are pricing and staffing the same work.
Navigating Certifications and Washington State Regulations
A vendor can promise secure handling, responsible recycling, and complete reporting. Those promises matter less than the certifications, audit controls, and contract language behind them. In Seattle, that distinction is important because the region includes private enterprise, research institutions, healthcare networks, and public agencies with very different risk profiles.
One warning sign stands out for public sector buyers. A 2025 EPA report showed 68% of Pacific Northwest government entities faced compliance fines for improper e-waste disposal, and Washington’s updated HB 1389 mandates serialized asset tracking for state contracts, according to the Seattle ITAD compliance discussion published by GreenTek Solutions. Even if your organization isn’t a state agency, that points to a broader lesson: generalized recycling services often don’t meet enterprise or government documentation standards.
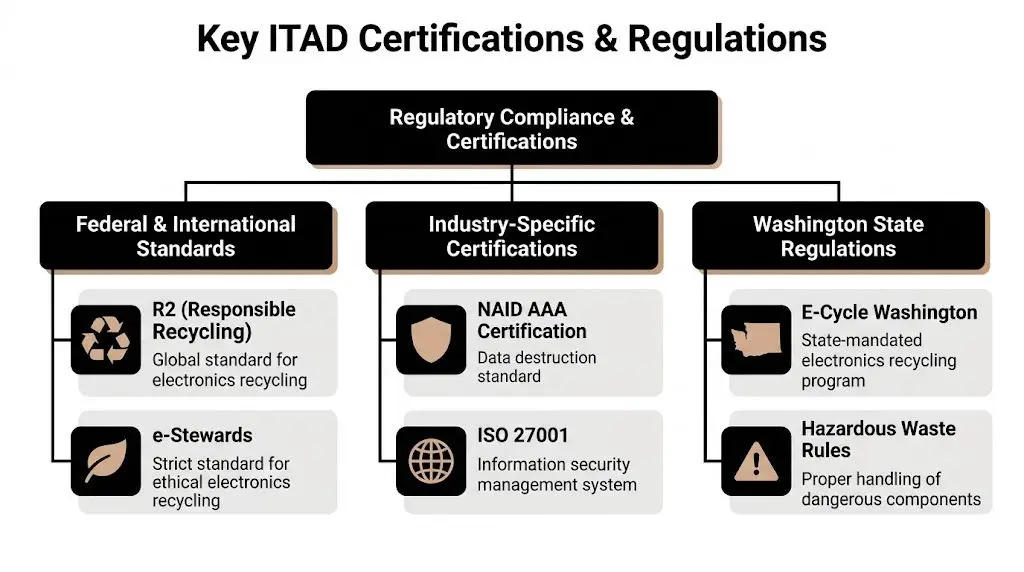
What the main certifications actually tell you
Not every certification answers the same question.
R2v3
R2v3 is the operational standard I’d expect serious enterprise buyers to ask about first. It speaks to responsible recycling controls, downstream accountability, environmental handling, and process discipline. In practice, it’s useful because it forces a recycler or ITAD provider to prove how materials move through the chain, not just what the sales team says happens.
For Seattle companies with sustainability reporting obligations, R2v3 is often the baseline certification that helps reconcile security and environmental goals.
e-Stewards
e-Stewards is also relevant when the organization places heavy emphasis on ethical downstream management and strict environmental practices. Some procurement teams prefer it when international downstream concerns or corporate responsibility scrutiny is high.
The important point isn’t to treat one badge as universally “better.” It’s to ask which certification aligns with your risk profile and reporting obligations.
NAID AAA
NAID AAA Certification is the credential many buyers look for when data destruction is central to the project. It focuses on secure destruction practices, process controls, and audited handling of confidential material. If drives, tapes, and storage media are a major part of your scope, this is often the credential that separates a certified destruction workflow from a generic recycling process. Reworx explains the role of this credential in its overview of NAID AAA certification.
Why Washington rules complicate vendor selection
Seattle companies sometimes assume that if a recycler operates in Washington, it must automatically fit enterprise compliance needs. That isn’t how this works.
E-Cycle Washington serves an important public purpose, but it is designed around consumer-facing electronics recycling access, not enterprise-grade serialized intake, chain of custody, or custom SLA reporting. A business can’t rely on a consumer-oriented pathway if the organization needs asset-level documentation, proof of destruction, or internal audit evidence.
Public sector agencies and quasi-public institutions in King County need to be more careful still. If a contract requires serialized tracking, your vendor must be able to capture assets at intake, preserve records across transport and processing, and return reports in a format procurement and compliance teams can use.
A truck and a scale ticket aren’t an ITAD program. For regulated organizations, they’re missing the most important parts.
A practical vendor vetting checklist
Use these questions in vendor interviews and RFP reviews:
- Can the vendor show current certification scope? Ask for certificates and scope statements, not logos on a website.
- How are serial numbers captured? Intake method matters. Manual spreadsheets are not the same as controlled serialized workflows.
- What reporting is standard versus extra? Some vendors advertise reporting, then charge separately for the level auditors require.
- Who handles downstream materials? You need visibility into where non-resellable material goes.
- What happens with exceptions? Damaged drives, unlabeled equipment, and embedded storage are where weak processes break down.
Match credentials to your environment
A biotech company with regulated research data, a hospital network subject to privacy requirements, and a city agency answering to procurement rules can’t all use the same low-detail statement of work. Seattle buyers should match vendor credentials to the environment where the equipment originated.
That means the procurement file should include more than a recycling certificate. It should show that the vendor can support your specific operating model, whether that’s office cleanouts, data center decommissioning, or government asset retirement with serialized audit evidence.
Mastering Data Destruction and Chain of Custody
The most expensive mistake in ITAD usually isn’t a poor resale result. It’s uncontrolled data. Retired devices carry old credentials, cached files, customer records, source code, scans, and backups. If you don’t govern destruction carefully, yesterday’s hardware becomes tomorrow’s incident report.

That’s one reason the market is moving this direction. The Data Destruction segment within the North American ITAD market is projected to grow at a 14.3% CAGR, reflecting stronger cybersecurity concerns and growing use of advanced sanitization and tracking technologies, according to KBV Research on the North American ITAD market.
Pick the destruction method that fits the media
The right method depends on the asset, the sensitivity of the data, and whether the device still has remarketing potential.
Software-based erasure
For reusable devices, NIST 800-88-aligned erasure is often the best path. It preserves asset value while providing a documented sanitization process. This works well for many laptops, desktops, and some storage devices that remain functional.
Use erasure when:
- The media is healthy enough to process
- The asset may be reused or resold
- Your policy accepts logical sanitization with verification
Degaussing
Degaussing disrupts magnetic media. It can be appropriate in environments that handle older magnetic storage and require strong destruction controls, but it also makes media unusable afterward. It’s not a universal answer because not all modern media types respond the same way.
Physical shredding
Shredding is the method most security teams trust for failed drives, high-risk media, and devices that won’t be remarked. It’s direct, visible, and easy to write into policy for sensitive environments.
Field advice: Shred when the business value of certainty outweighs the resale value of the device.
Chain of custody is where secure plans succeed or fail
A valid destruction method is only part of the answer. You also need a defensible chain of custody from the moment assets leave service.
That means the provider should be able to explain, in order:
How assets are identified at collection
Serial capture, asset tags, or intake labels should happen before equipment disappears into gaylords or pallets.How custody changes are recorded
You want documented handoffs, named personnel, and time-stamped events.How transport is secured
Locked vehicles, controlled routing, and monitored transit procedures matter because many losses occur between sites, not at the facility.How exceptions are flagged
A broken drive, a missing serial, or an unlisted laptop shouldn’t roll into the same stream without notation.How final outcomes are tied back to the asset record
Your report should connect each item to erasure, shredding, resale, or recycling status.
What to require in the certificate
A useful Certificate of Data Destruction is not a ceremonial PDF. It should support audit review. At minimum, require:
- Asset identification: Serial numbers or other traceable identifiers
- Destruction method: Erasure, degaussing, shredding, or mixed workflow
- Date and location: When and where destruction occurred
- Authorization trail: The provider’s responsible party or processing record
- Reference to the service event: Pickup, project number, or work order linkage
If a provider can only produce a general statement that “materials were destroyed,” that’s not enough for most enterprise environments.
Operational controls matter during office cleanouts
During office cleanouts and facility closures, data security often slips because speed takes over. Someone starts boxing equipment by department, monitors get separated from docks, and loose drives appear in desk drawers after the formal pickup is complete.
That’s why secure services need to be embedded into the project itself, not bolted on after. Reworx outlines its approach to secure data destruction services, including destruction handling as part of broader equipment retirement.
The best Seattle ITAD projects treat chain of custody as a living operational control. Not paperwork after the fact.
Optimizing Logistics and Maximizing Value Recovery
Too many organizations evaluate ITAD as if the only question is removal cost. That’s a narrow view. In practice, the project has two linked outcomes: how efficiently you clear the assets, and how much value you preserve on the way out.

The economics are real. Professional ITAD services can recover 10-50% of residual value from surplus gear, R2v3-certified firms outperform non-certified ones by 40% in value recovery, and in-house ITAD attempts fail in 70% of cases. The same source notes that 1 in 10 improperly disposed drives retain recoverable data, according to Transpere’s Seattle ITAD benchmark page.
Reverse logistics needs a real operating plan
A Seattle pickup isn’t just a truck appointment. Downtown towers, shared loading bays, suburban campuses, and multi-site networks all create different constraints. The wrong plan adds labor, delays, and asset confusion.
A workable logistics plan should answer:
- Where will assets be staged? Secure room, loading area, rack row, or departmental floor.
- Who is responsible for prep? Internal staff, provider technicians, or mixed teams.
- What must stay segregated? Resale candidates, destruction-only media, and scrap material should not be mixed.
- How is business disruption reduced? Pickup windows should fit building rules and operational downtime.
Value recovery requires selectivity
Not every retired asset should be sold. Some should be redeployed internally. Some should be donated. Some should be recycled immediately because testing costs and handling risk exceed any likely return.
Here’s the practical hierarchy I use:
| Asset condition | Usually best path |
|---|---|
| Late-model, working equipment | Remarketing or internal redeployment |
| Usable but lower-market-value gear | Donation-based reuse or selective resale |
| Failed devices with sensitive media | Media destruction, then commodity recovery |
| Obsolete or damaged equipment | Certified recycling |
Such practices frequently lead to financial losses for internal teams. They either scrap everything too quickly, or they hold everything too long hoping for resale. Both choices are costly.
The best value recovery program isn’t the one that tries to resell the most items. It’s the one that makes disposition decisions quickly and correctly.
Donation-based recycling is a legitimate enterprise option
For some Seattle organizations, donation-based recycling fits better than a pure buyback model. It supports social impact goals, aligns with digital inclusion initiatives, and can strengthen ESG reporting when done with proper documentation and controlled handling.
That works especially well for:
- Employee laptop refreshes
- School and nonprofit partnership programs
- Community technology access initiatives
- Mixed fleets where some assets have modest market value but strong reuse potential
Reworx provides asset recovery services that can support that kind of planning alongside more traditional ITAD pathways.
The key is to keep standards consistent. Donation should never mean informal handling. Devices still need inventory control, data sanitization, and documented disposition.
Building Your RFP and Choosing Your Seattle ITAD Partner
By the time you’re ready to issue an RFP, the hard part should already be done. You should know your asset profile, your security requirements, your regulatory exposure, your reporting needs, and your value recovery priorities. The RFP’s job is to force vendors to answer those requirements in comparable terms.
If your procurement team wants a broader template for structuring the document itself, this powerful request for proposal guide is a helpful reference. For ITAD, though, generic procurement language won’t be enough. You need clauses that expose process quality.
Clauses worth putting into the RFP
Below is sample language I’d consider for a Seattle enterprise ITAD procurement package. Edit it to fit your environment and legal review process.
Data security clause
“The vendor shall document all data sanitization and destruction methods used for retired media and devices. The vendor shall identify which assets are eligible for software-based sanitization and which require physical destruction. The vendor shall provide asset-level records tying each device to its final destruction or sanitization outcome.”
That language prevents vague replies like “all drives are handled securely.”
Chain-of-custody clause
“The vendor shall maintain documented chain of custody from collection through final disposition. Records shall include intake identifiers, custody transfers, transport controls, facility receipt, processing status, and final disposition reporting.”
That’s where weak operators often struggle. If they can’t explain handoffs, they can’t prove control.
Reporting clause
“The vendor shall provide final reporting in a format suitable for audit review, including serialized asset lists where applicable, certificates of data destruction, and documentation of final disposition categories.”
Do not assume “reporting included” means the report you need.
SLA points that separate serious providers from haulers
A service-level agreement should answer how the work will be performed.
Consider requiring responses on:
- Pickup scheduling: Defined service windows and escalation contacts
- Onsite labor scope: Deinstallation, packing, palletizing, and segregation responsibilities
- Exception management: Process for unlisted assets, damaged media, and inaccessible equipment
- Insurance and liability: Evidence of coverage relevant to transport and processing activities
- Downstream accountability: Disclosure of material handling beyond the primary facility
A simple evaluation matrix
Use a weighted scorecard. Not all criteria deserve equal weight.
| Evaluation area | What strong answers look like |
|---|---|
| Security controls | Clear destruction methods, asset-level traceability, documented custody events |
| Compliance fit | Certifications aligned to your environment and reporting needs |
| Operational capability | Can handle office, data center, and specialty equipment without improvising |
| Reporting quality | Sample certificates, serialized reports, and exception logs available for review |
| Value recovery approach | Real grading and disposition logic, not blanket scrap assumptions |
| Sustainability alignment | Credible reuse and recycling pathways with usable environmental documentation |
Ask every finalist for a sample final report package. Sales promises get abstract fast. Reporting examples do not.
What Seattle buyers should ask in the finalist round
The best finalist interviews are specific and slightly uncomfortable. Good vendors won’t mind.
Ask questions like these:
- How do you handle a pallet that contains listed assets, unlisted assets, and loose drives?
- What happens if a serial number is unreadable on intake?
- When do you recommend shredding instead of erasure?
- How do you document downstream recycling for material that has no resale value?
- What does the client receive after a facility cleanout versus a routine refresh cycle?
If you’re comparing providers for Enterprise IT Asset Disposition Services in Seattle, you can also review how Reworx frames its IT asset disposition company services. The useful question is whether any provider can support your required controls consistently across pickups, destruction, reporting, and final disposition.
The right partner won’t just remove equipment. The right partner will make your internal stakeholders more comfortable saying yes. Security knows the data is handled properly. Facilities knows the site will be cleared without chaos. Sustainability gets documentation it can use. Procurement gets contract language that stands up later. That’s the standard worth buying.
Seattle businesses don’t need another informal e-waste workaround. They need a documented ITAD process that protects data, supports compliance, and creates responsible reuse or recycling outcomes. If your team is planning a tech refresh, office cleanout, data center decommissioning, or corporate donation program, Reworx Recycling is one option to explore for secure electronics recycling, IT equipment disposal, and donation-based recycling support.