A Chicago enterprise rarely has an IT refresh problem. It has a governance problem disguised as logistics.
A few floors of departing laptops, aging monitors, retired mobile devices, storage media from a server refresh, and a facilities team trying to clear space before the next rollout can turn into a messy chain of custody issue fast. In a city with dense office footprints, regulated industries, and constant pressure to show measurable sustainability progress, IT Asset Disposition in Chicago for Enterprise Companies isn't a back-office cleanup task. It's a risk decision, a financial decision, and increasingly an ESG decision.
The companies that handle it well treat ITAD as part of enterprise operations. The ones that don't usually discover the gap later, during an audit, a legal review, a relocation, or a board-level sustainability discussion.
The High-Stakes Challenge of Enterprise ITAD in Chicago
A CIO in a Loop office tower approves a major hardware refresh. Procurement has done its work. New devices are inbound. Then the harder question lands on IT, legal, facilities, and sustainability at the same time: what happens to the outgoing assets, and how do you prove they were handled correctly?
That question gets more complicated in Chicago because scale piles up quickly. A single enterprise footprint can include headquarters users, suburban offices, remote employees, lab equipment, conference room technology, network gear, and storage devices that can't leave the building without a documented chain of custody. This isn't ordinary electronics recycling. It's operational decommissioning with legal and reputational consequences.

Chicago has long mattered in this market. Chicago has been a dominant U.S. hub for IT Asset Disposition since the late 1990s, and the city became one of the top three U.S. markets alongside New York and San Francisco because of its concentration of corporate headquarters, tech firms, and logistics capacity. The broader North America ITAD market reached USD 4.04 billion in 2022 and is projected to grow to USD 7.45 billion by 2032 at a 6.2% CAGR, according to Chicago ITAD market context from Cascade Asset Management.
Why enterprise scale changes the equation
At enterprise volume, disposal mistakes don't stay small.
- A missed drive isn't just a missed drive. It can become a reportable incident.
- Poor inventory control doesn't just slow a project. It breaks auditability.
- Unstructured recycling doesn't just lose value. It weakens the business case for future refresh programs.
- Undocumented downstream handling doesn't just create uncertainty. It creates exposure for legal, procurement, and ESG reporting teams.
Practical rule: If your ITAD plan starts after the new equipment arrives, you're already behind.
Large Chicago organizations also face a practical city problem. Equipment removal has to work around loading docks, elevator schedules, building access windows, and downtown traffic patterns. A provider that looks capable on paper can still fail in execution if it can't manage urban pickups, serial-level tracking, and cross-functional communication.
What works and what fails
What works is early planning tied to real asset classes. Laptops, docks, monitors, smartphones, drives, racks, and specialty devices shouldn't all move through the same process. Some belong in resale streams. Some belong in certified destruction. Some may fit donation pathways if security, condition, and policy allow.
What fails is treating the entire project like a bulk junk haul. Once enterprise assets are mixed, poorly labeled, or removed without a clear manifest, value recovery drops and compliance work gets harder. Chicago companies don't need another recycler that shows up with a truck. They need a disposition process that holds up under scrutiny.
Developing Your Strategic Enterprise ITAD Framework
A strong ITAD program works like a controlled operating model, not a pickup request. The framework has to answer five questions before the first pallet moves: what you have, what data sits on it, who touches it, what residual value remains, and what proof you'll keep after disposition.
That matters because enterprise demand is moving toward more formal programs. The global enterprise ITAD segment is projected to reach USD 17.16 billion by 2030 at a 15.2% CAGR, and computers and laptops are expected to account for 42.60% of North America ITAD volume in 2025, driven by hybrid-work refresh cycles, according to enterprise ITAD market data from Ken Research.
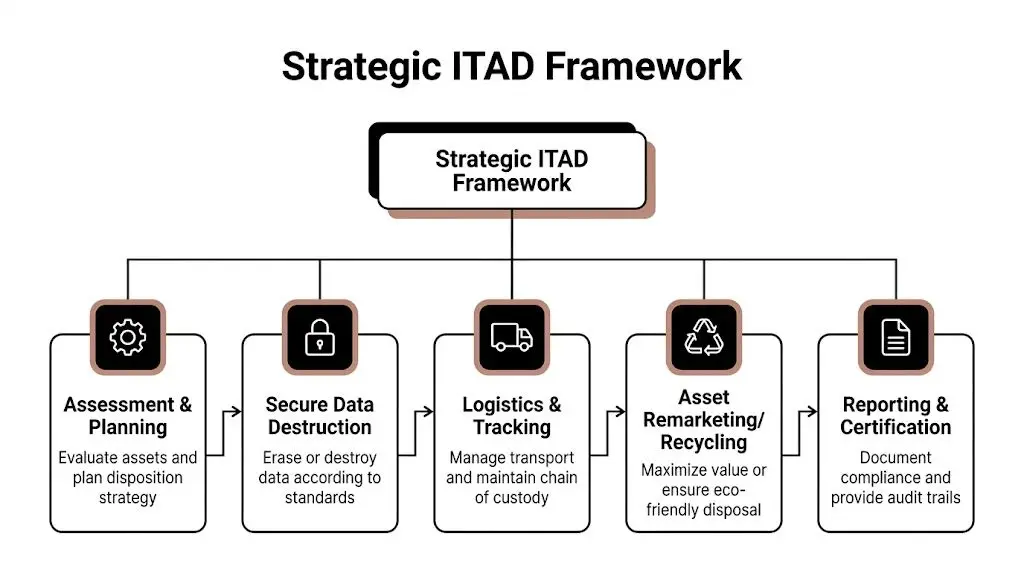
Assessment and planning
Start with a disposition map, not a truck date.
You need a current inventory, but not just a count. The useful version includes asset type, user group, physical location, condition, data sensitivity, and likely end path. A laptop used by finance shouldn't be grouped with display hardware from a conference room or with old networking gear from a lab closet.
Three planning decisions usually shape the rest of the project:
- Which assets are eligible for remarketing. Devices with residual value should be separated early.
- Which assets require mandatory destruction. This includes media and devices tied to sensitive environments.
- Which business units need exception handling. Healthcare, legal, finance, and R&D often need tighter review.
Secure processing and logistics
Most enterprise failures happen in the middle, not at the beginning or end. Inventory is created, certificates are eventually issued, but the transport and handoff steps are weak.
A mature framework should include:
- Serialized intake controls so each high-risk asset can be tracked individually
- Documented chain of custody from site release through final processing
- Controlled packaging and segregation to prevent mix-ups between resale and destruction streams
- Exception handling for damaged devices, locked assets, and missing tags
- Site-specific pickup planning for towers, campuses, data rooms, and remote collections
This is also where temporary staging can become a hidden problem. If your internal team is stacking retired equipment in closets, conference rooms, or shared storage areas, you are creating avoidable exposure. In broader operations planning, offsite storage helps streamline your operations because it reduces internal congestion and clarifies accountability. The same principle applies to ITAD staging. Uncontrolled storage tends to become invisible inventory.
The best enterprise ITAD programs reduce touches. Every additional handoff adds delay, confusion, and risk.
Remarketing, recycling, and reporting
Reactive disposal and strategic ITAD separate.
Some assets should be refurbished and resold. Some should move into parts harvesting. Others belong in certified recycling because condition, age, or policy eliminate reuse. The choice shouldn't be emotional and it shouldn't be improvised. It should follow a written disposition policy aligned with security, finance, and sustainability goals.
A consultative provider can help build that policy across departments. Reworx Recycling is one example of a partner that offers IT asset disposition, secure data destruction, pickups, and reverse logistics support, which is useful when a company wants one operating model across office cleanouts, equipment retirement, donation-based recycling, and formal reporting.
What a usable framework includes
A framework is ready when it produces the same outcome under pressure.
- Clear ownership: IT, facilities, procurement, legal, and sustainability each know their role.
- Documented decision trees: Teams know when to wipe, shred, remarket, donate, or recycle.
- Operational cadence: Refreshes, office exits, and data center projects don't require reinvention.
- Proof at the end: The records support audit, insurance, and ESG review.
If those elements aren't in place, the organization doesn't have an ITAD strategy. It has a disposal habit.
Navigating Chicago's Compliance and ESG Demands
For Chicago enterprises, compliance usually gets discussed in narrow terms. Was the data destroyed? Was the equipment recycled? Was the paperwork filed?
Those are baseline questions. The more difficult question is whether the disposition program creates evidence that stands up across legal, environmental, and disclosure workflows. That's where many companies still have a gap.

A key issue in Illinois is the weak bridge between recycling activity and reportable ESG outputs. According to Illinois ITAD ESG reporting context, the state generated approximately 1.2 million tons of e-waste in 2023, yet only 20% was responsibly recycled, and enterprises face a significant guidance gap when trying to connect ITAD work to auditable sustainability metrics tied to disclosure requirements.
Compliance is broader than disposal
In practice, enterprise ITAD touches multiple obligations at once.
Healthcare organizations have to think about protected data. Financial institutions care about records control and defensible process. Public companies and large private firms increasingly need documentation that supports governance review and sustainability reporting. Even when the law doesn't prescribe a single disposition workflow, auditors and internal counsel still expect a repeatable, documented system.
That means a Chicago ITAD program should produce more than a certificate. It should produce a record set that answers these questions:
- What assets left the enterprise environment
- Which destruction or reuse path each asset followed
- Who handled the assets at each transfer point
- What environmental outcome the company can support with documentation
- Whether any social impact claims are tied to verifiable donation or reuse pathways
Where ESG programs usually break
Most sustainability teams can report on large waste streams, energy projects, and facility programs. End-of-life IT often falls between departments.
IT sees devices. Facilities sees removal. Procurement sees residual value. Sustainability wants diversion data. Legal wants proof that nothing creates a disclosure problem. The result is fragmented reporting, especially when the vendor's documentation wasn't built for ESG use in the first place.
Common weak spots include:
- Weight-only reporting: Useful for hauling records, weak for enterprise storytelling and audit detail.
- No separation between reuse and recycling: That blurs the environmental and community value of the program.
- Missing donation traceability: Social impact claims become hard to support.
- No asset-level reconciliation: Sustainability can't match outcomes to enterprise inventory.
- Generic certificates: They satisfy a transaction file but not a board-facing ESG narrative.
ESG claims tied to retired technology should be as auditable as financial claims tied to retired leases.
Turning ITAD into usable ESG evidence
A stronger model starts by defining reporting outputs before pickup. If the sustainability office needs data for annual reporting, that requirement has to shape intake, segregation, and final certificates. Otherwise the company ends up trying to reconstruct evidence after the fact.
A practical enterprise scorecard usually tracks four categories qualitatively and, where available from the vendor, with auditable supporting detail:
| Reporting area | What the enterprise should ask for |
|---|---|
| Asset accountability | Serialized lists or reconciled equipment manifests |
| Data governance | Destruction method, date, and custody records |
| Environmental outcome | Clear distinction between reuse, refurbishment, and recycling |
| Community benefit | Documentation for approved donation or digital inclusion pathways |
For teams building a local program, this business leader's guide to electronics recycling in Chicago is useful because it frames how recycling decisions connect to operational and environmental responsibilities in the city.
The social enterprise angle matters
A standard recycler can close a ticket. A social enterprise model can help a company support a wider narrative around responsible disposition, community technology access, and workforce impact, if the chain of documentation is solid.
That doesn't mean every retired enterprise device should be donated. Many shouldn't. Security, age, condition, and policy come first. But when approved assets are suitable for reuse, a donation-based recycling channel can strengthen the "S" in ESG in a way that scrap-only programs can't.
Chicago companies tend to miss this by treating ITAD and community benefit as separate initiatives. In reality, they can sit in the same controlled process if governance comes first. The key is discipline. Donation can't become an informal side stream. It has to be a defined disposition path with documented approval, data handling, and downstream proof.
Ensuring Ironclad Data Security and Chain of Custody
The most expensive ITAD mistake usually isn't environmental. It's informational.
A single drive with recoverable data can erase years of careful policy work. That's why serious enterprise ITAD begins with one assumption: every device should be treated as if it contains sensitive information until proven otherwise.
Choose the destruction method by asset and risk
Teams often talk about data wiping, degaussing, and shredding as if they're interchangeable. They aren't.
Data wiping is appropriate when the asset is intended for reuse and the media supports reliable sanitization. The value advantage is obvious. If the device can be securely sanitized and remarketed, the enterprise preserves recovery potential.
Degaussing applies to certain magnetic media. It can be effective in the right context, but it also changes the asset's future use. It isn't a generic answer for all device types.
Physical shredding is the hard stop. When policy, media condition, or data sensitivity rules out reuse, shredding gives the clearest finality. That's why many enterprises reserve it for failed drives, highly sensitive storage, or environments where any residual risk is unacceptable.
The operational mistake is picking one method for every asset. The right practice is to define a destruction matrix in advance.
Make chain of custody visible
Chain of custody isn't a slogan. It's the documented sequence showing where an asset was, who controlled it, and what happened to it.
That sequence should begin before removal from the office or data center. Labels, manifests, sealed containers where appropriate, signed release points, receiving logs, processing timestamps, and final certificates all matter. If one of those steps is missing, counsel and auditors will notice.
A workable custody model usually includes:
- Site release controls tied to authorized personnel
- Asset reconciliation against internal inventory or pickup manifests
- Transport documentation with time and custody handoff records
- Processing records that link a device to sanitization or destruction outcome
- Exception escalation for missing, damaged, or unscannable items
If your provider can't show you where an asset was between pickup and processing, you don't have a secure chain of custody. You have a hope-based process.
Audit the process, not just the promise
Many enterprises overvalue policy language and undervalue operational proof. A vendor may describe secure handling well, yet still rely on inconsistent intake practices, pooled assets, or loosely managed receiving areas.
The better test is observational. Ask what happens when:
- a serial number doesn't match,
- a device arrives damaged,
- a drive is found inside a unit that wasn't flagged for media destruction,
- a remote office sends equipment without proper labeling,
- or a pickup includes equipment outside the agreed scope.
These moments reveal whether security is built into the process or added to the sales deck.
For organizations that need formalized handling, secure data destruction services from Reworx Recycling outline the type of controls companies should expect around device processing, hard drive shredding, and documented destruction workflows.
Security practices that hold up under pressure
When a project is rushed, weak procedures surface fast. Strong programs hold up because the rules are simple and enforced.
- Segregate by disposition path: Assets for reuse should never be casually mixed with destruction-only media.
- Treat unidentified storage as high risk: If the team doesn't know what's on it, don't downgrade the handling.
- Control onsite staging areas: Temporary accumulation points need restricted access and documented ownership.
- Require exception logs: Missing or mismatched assets need a written trail, not hallway conversations.
- Review certificates against manifests: Final paperwork should reconcile to what left your premises.
A secure enterprise ITAD program doesn't depend on trust alone. It depends on traceability.
Optimizing Logistics and Value Recovery Models
Chicago enterprises don't struggle with the concept of ITAD. They struggle with execution at building level and portfolio level.
A downtown law firm clearing six floors faces one logistics profile. A suburban data center retiring storage hardware faces another. A regional employer collecting laptops from remote staff across the metro area faces a third. The right model isn't the one with the lowest line-item price. It's the one that protects continuity while preserving recoverable value.
According to Chicago onsite versus offsite ITAD cost analysis from Transpere, onsite shredding can cost 30% to 50% more per asset, around $15 to $25 per unit versus $10 offsite, but it can reduce data center downtime by 40%. The same source notes that logistics costs can be up to 25% higher in Chicago because of urban density.
Onsite versus offsite isn't a philosophical debate
It's an operating choice with trade-offs.
If the business priority is absolute immediacy and minimal movement of sensitive media, onsite destruction may justify the premium. If the asset mix includes a meaningful percentage of reusable devices, offsite processing often creates more flexibility for testing, refurbishment, and value recovery.
Here is the practical comparison.
| Factor | Onsite Services | Offsite Services |
|---|---|---|
| Security posture | Strong for immediate witnessed destruction of high-risk media | Strong when chain of custody and facility controls are disciplined |
| Cost profile | Higher per asset in many cases | Lower per asset in many cases |
| Operational disruption | Can reduce downtime in certain environments | May require more coordination for pickup and staged removal |
| Value recovery potential | Lower when assets are destroyed immediately | Higher when devices can be tested, wiped, and remarketed |
| Best fit | Sensitive media, urgent decommissioning, strict internal policy | Mixed asset portfolios, office refreshes, broader resale strategy |
Where companies leave money on the table
The biggest financial mistake is over-destroying reusable equipment because the project was scoped too broadly. If everything is treated like scrap, the enterprise gives up remarketing value and often pays more for processing.
The second mistake is under-planning pickup logistics. In Chicago, loading docks, security desks, elevator reservations, and downtown time windows can turn a simple office cleanout into repeated truck rolls and idle labor charges. The cheapest quote on paper can become the most expensive path in execution.
A better model separates assets into at least three streams:
- Mandatory destruction assets such as failed drives or highly sensitive media
- Value recovery assets such as eligible laptops and certain enterprise hardware
- Donation or recycling assets where policy and condition make reuse or material recovery appropriate
A disciplined triage model usually outperforms a one-stream removal plan because it aligns cost, security, and residual value instead of forcing one answer onto every device.
Build logistics into your ROI model
An ROI discussion should include more than resale revenue and service fees. It should account for internal labor, business interruption, storage congestion, freight complexity, and the cost of delayed site turnover.
For larger projects, reverse logistics planning matters as much as downstream processing. In such cases, reverse logistics solutions for IT transitions can be relevant, especially when a company is coordinating pickups across multiple sites, office cleanouts, and staggered refresh schedules.
In Chicago, the most effective value recovery programs are boring in the best sense. Assets are categorized early. Pickup windows are realistic. Building access is confirmed. Destruction policy is narrow and intentional. Reuse candidates are protected instead of crushed by default.
That's how you turn ITAD from a cost center into a controlled recovery program.
How to Choose Your Chicago ITAD Partner
Most enterprise vendor failures are visible before the contract is signed. The problem is that teams often ask the wrong questions.
Price matters, but it rarely tells you whether the provider can manage sensitive removals from a Chicago high-rise, support a data center decommissioning event, or produce documentation that survives audit and ESG review. Vendor selection should focus on operational competence, not just service categories.
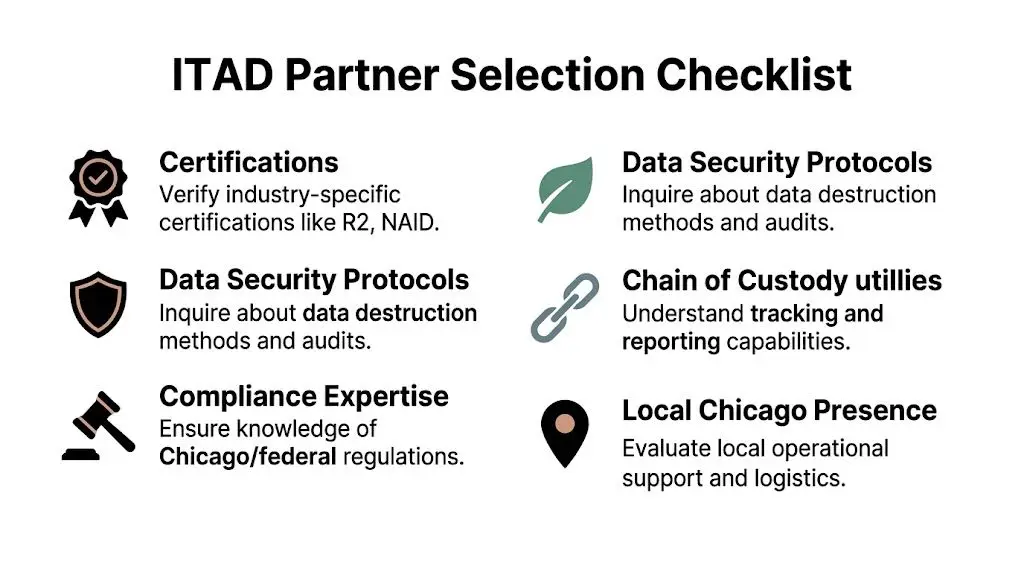
The shortlist criteria that matter
A serious partner should be able to explain, in plain language, how it handles intake, transport, processing, exceptions, reporting, and downstream accountability. If the answers stay vague, move on.
Use this checklist during procurement review.
- Certifications and standards: Ask which certifications are current and which facility they apply to. Don't accept broad claims that aren't tied to the actual processing site.
- Data destruction controls: Require a clear explanation of when the provider wipes, degausses, or physically destroys media, and how that gets documented.
- Local execution capability: In Chicago, local operating reality matters. Ask how the team handles loading docks, downtown scheduling, secure pickups, and multi-site coordination.
- Insurance and liability posture: Confirm environmental coverage and data-related risk coverage appropriate to your organization's requirements.
- Reporting quality: Request sample certificates, serialized reports, and exception documentation before signing.
- Downstream transparency: Ask where equipment goes after initial processing and how the provider monitors reuse, recycling, or destruction channels.
- Social impact fit: If ESG or CSR matters, ask how approved equipment donation is governed and documented.
Sample RFP questions procurement can use
A good RFP forces specificity. It doesn't invite marketing copy.
Consider language like this:
- Describe your chain of custody process from onsite pickup through final disposition, including how custody transfers are recorded.
- Provide sample reports showing serialized asset reconciliation, data destruction documentation, and final recycling outcomes.
- Explain your process for handling mixed loads that include reusable devices, destruction-only media, and nonconforming equipment.
- Identify which services are performed onsite and which are performed at your processing facility.
- Describe how your organization supports donation-based recycling or community reuse programs without weakening data security controls.
- List the circumstances under which assets are remarketed, recycled, or physically destroyed.
- Explain your escalation process for missing serials, damaged assets, and custody exceptions.
One practical lesson from public and enterprise procurement is that specialist services require specialist evaluation. The reasoning is similar to choosing a specialized service. Generic procurement language often misses the operational details that determine success.
Red flags that deserve immediate scrutiny
Some warning signs show up quickly.
| Red flag | Why it matters |
|---|---|
| Generic certificates with little asset detail | Weak audit support |
| No clear answer on downstream vendors | Environmental and reputational uncertainty |
| One-size-fits-all destruction policy | Lost value or weak risk alignment |
| Vague local service model | Pickup failures and project delays |
| No exception handling process | Missing asset risk increases |
For a more practical evaluation lens, this guide on factors in choosing an e-waste recycling partner is worth reviewing because it pushes beyond price and into process, accountability, and reporting.
Vendor selection should answer one question above all others: if something goes wrong, will this provider help you prove control or explain a gap?
That standard tends to produce better choices than any discount ever will.
The Final Step Certificates and Proof of Performance
An ITAD project isn't finished when the truck leaves or when the drives are destroyed. It's finished when the records are complete, internally filed, and usable months later by audit, legal, compliance, procurement, and sustainability teams.
Weak providers often expose themselves. They complete the physical work, then issue paperwork that's too generic to defend the outcome.
What a real certificate should show
A legitimate Certificate of Data Destruction should do more than confirm that "data was destroyed." For enterprise use, it should identify the assets or media covered, the method used, the date, and the processing entity. If the certificate can't be reconciled to your internal manifest, it has limited value.
A Certificate of Recycling should be equally concrete. It should show what was received, what scope it covered, and that the materials entered a documented recycling pathway rather than an informal disposal stream.
At minimum, the documentation set should help your team answer:
- Which assets were included
- What happened to each relevant category
- When the work occurred
- Which method was used for destruction or processing
- How the certificate ties back to the original pickup or manifest
How enterprises should review the paperwork
Don't file certificates automatically. Review them against the job scope.
If a data center decommissioning involved serialized storage media, the final destruction record should reflect that level of detail. If an office cleanout included mixed equipment categories, the recycling paperwork should align to what left the site. If assets were approved for donation or reuse, the reporting package should distinguish those outcomes clearly from scrap recycling.
This is also the point where ESG reporting becomes real. Sustainability teams don't need broad assurances. They need auditable evidence. The certificate package is often the only durable proof that connects retired equipment to environmental handling, secure data disposition, and approved community impact pathways.
A useful reference point for documentation standards is this explanation of a certificate of destruction for hard drives, which shows the level of specificity companies should expect when sensitive media is involved.
Proof of performance is what protects you later
Months after a project closes, details fade. Staff changes. Office moves happen. Auditors ask questions nobody anticipated. That's when paperwork stops being administrative and starts becoming defensive infrastructure.
The certificate isn't the receipt for the job. It's the evidence that the organization controlled the job.
For Chicago enterprises, that matters because ITAD sits at the intersection of data risk, environmental responsibility, and public accountability. If your final records are incomplete, the whole program looks weaker than it really was. If your final records are precise, the organization can show that it handled retired technology with discipline.
If your organization is planning a device refresh, office cleanout, data center decommissioning, or broader electronics recycling initiative in Chicago, Reworx Recycling is a practical resource for learning how donation-based recycling, secure data destruction, pickup scheduling, and responsible IT equipment disposal can fit into a more defensible enterprise program. Use that planning window before assets pile up. It's the easiest time to protect value, tighten compliance, and build measurable community impact into the process.