Secure HDD disposal isn't just about deleting files; it's the process of ensuring data on your company's old hard drives is irrecoverable, typically through certified data wiping, degaussing, or physical shredding. This final step in IT asset disposition (ITAD) is a critical security measure because simply hitting "delete" or reformatting a drive is not nearly sufficient to protect sensitive information.
Why Secure HDD Disposal Is a Core Business Priority
In today's data-driven economy, the hard drives retired from your business's servers, laptops, and workstations are more than just obsolete hardware. They are compact vaults containing sensitive information—from financial records and customer PII to employee files and invaluable intellectual property.

Allowing these devices to accumulate in a storage closet or, worse, disposing of them without proper data sanitization, transforms retired assets into significant liabilities. The consequences of improper disposal are severe, ranging from devastating data breaches that erode customer trust to substantial fines for non-compliance with regulations like HIPAA, GDPR, or CCPA.
Proper hard drive disposal has evolved from an IT checklist item to a fundamental component of corporate risk management and brand protection. An experienced ITAD partner provides the expertise and, crucially, the documentation to prove your data was permanently destroyed, offering a clear chain of custody and a Certificate of Destruction as proof of due diligence.
The Escalating Stakes of Data Security
The growing importance of this process is reflected in market trends. The global Hard Drive Destruction Service Market, valued at USD 1.65 billion, is projected to reach USD 5.05 billion by 2035, growing at an annual rate of 10.7%. This growth is a direct response to the rising costs of data breaches and increasingly stringent compliance mandates.
This is precisely why partnering with a certified IT asset disposition (ITAD) provider like Reworx Recycling is no longer a luxury—it's a necessity for any responsible business. For companies new to formal ITAD, understanding the different methods of secure data destruction is the ideal starting point.
A proactive approach to secure HDD disposal shifts your organization from a reactive, damage-control mindset to a forward-thinking data defense strategy. It acknowledges that the data lifecycle doesn't end when a device is powered down for the last time.
From Compliance Burden to Community Impact
While managing risk is the primary driver for secure data destruction, modern ITAD presents an opportunity to achieve more. Implementing robust Data Security Best Practices, including secure HDD disposal, is essential for protecting your organization's sensitive information. When you partner with a social enterprise like Reworx Recycling, this compliance requirement transforms into a powerful story of corporate social responsibility.
Reworx Recycling combines industry-leading data destruction services with a clear social mission. We help businesses like yours:
- Mitigate Risk: We provide certified data wiping, degaussing, and shredding services that meet or exceed all industry and regulatory standards.
- Ensure Compliance: You receive comprehensive documentation needed to satisfy auditors and regulatory bodies.
- Promote Sustainability: We responsibly recycle all unusable materials and refurbish viable equipment through our donation-based recycling model.
- Support Communities: We donate refurbished technology to schools, nonprofits, and workforce development programs, helping to bridge the digital divide.
This unique approach turns a routine operational need into a positive force for both the environment and the community, perfectly aligning your security requirements with your corporate values.
Evaluating Your Company's Data Disposal Risks
Before determining how to dispose of old hard drives, you must first understand what data you are protecting. A one-size-fits-all approach to data disposal is a common mistake that can lead to a compliance nightmare or a catastrophic data breach. A solid, defensible strategy begins with a thorough internal risk assessment—a deep dive into the types of information your company handles and where it resides.
The first step is a complete inventory of every data-bearing device. This extends far beyond servers and desktops to include any hardware that stores information.
- Servers and Data Center Equipment: Central repositories for your most critical business and customer information.
- Employee Laptops and Desktops: Contain a mix of corporate data, credentials, and potentially sensitive personal files.
- External Hard Drives & USB Sticks: Often lost or forgotten, these devices can hold large volumes of unencrypted data.
- Mobile Devices: Company smartphones and tablets are gateways to emails, contacts, and corporate networks.
- Networking Hardware: Routers and switches can retain configuration files and sensitive network logs.
- Printers and Scanners: Modern office machines have internal hard drives that cache copies of every document they process.
A detailed inventory is the foundation of your risk assessment. Understanding the full scope of your IT assets is so critical that we've outlined why IT inventory audits matter before recycling, helping you map every potential vulnerability.
Classifying Your Data's Sensitivity
Once you know what you have, the next crucial step is to determine what kind of data is on each device. Not all data is equal, and your disposal method must reflect its sensitivity level. A computer from your R&D department holding proprietary designs requires a higher level of security than a marketing laptop with public-facing materials.
Sort your data into key categories:
- Personally Identifiable Information (PII): Names, addresses, Social Security numbers, and other data targeted by identity thieves.
- Protected Health Information (PHI): Medical records or patient data governed by strict HIPAA regulations.
- Financial Data: Customer payment information, corporate financial records, and transaction logs.
- Intellectual Property (IP): Your competitive advantage—trade secrets, source code, strategic plans, and proprietary formulas.
This classification allows you to build a tiered disposal strategy. Low-risk assets with non-sensitive information may be ideal for certified data wiping and donation through a corporate donation program. However, any device that ever contained high-risk IP or PHI should be immediately flagged for physical destruction.
Real-World Risk Scenarios
Consider a regional law firm performing an office cleanout and retiring old workstations. These machines are filled with confidential client files, privileged communications, and PII. A data breach would be catastrophic, destroying client trust and incurring massive legal penalties. For this firm, on-site, witnessed shredding is the only acceptable option.
Now, imagine a retail chain upgrading its point-of-sale systems. These devices contain sensitive transactional data, but the main challenge is the cost-effective and compliant disposal of hundreds of identical units. In this scenario, secure off-site shredding from a certified partner like Reworx Recycling provides the perfect balance of security, documentation, and efficiency.
By thoroughly evaluating your assets and data, you replace guesswork with a strategic approach. This assessment ensures your secure HDD disposal plan is not just compliant, but perfectly tailored to your organization's unique risk profile.
Choosing the Right Data Destruction Method
Once you have assessed your data risks, it is time to select a destruction method. The decision largely depends on one key question: do you need to reuse the hardware, or is the data so sensitive that the drive itself must be physically destroyed?
Your answer will lead to one of three core methods. Each functions differently, suits specific scenarios, and has distinct compliance implications. Choosing correctly is a critical part of a robust IT asset disposition (ITAD) strategy.
Software Wiping for Asset Reuse and Donation
If you plan to redeploy, sell, or donate your hardware, software wiping is the ideal solution. This process goes far beyond a simple format, which only removes pointers to your data. Specialized software overwrites every sector of the hard drive with random characters, permanently destroying the original information.
Professional data wiping adheres to strict standards, with NIST 800-88 being the industry benchmark for sanitizing all types of storage media, from traditional Hard Disk Drives (HDDs) to modern Solid-State Drives (SSDs). For a detailed explanation, see our guide on how to properly wipe a hard drive for donation or recycling.
Using certified wiping methods allows hardware to have a second life with complete confidence. This is a cornerstone of Reworx Recycling's social enterprise model. We securely sanitize functional equipment and donate it to community programs, supporting digital inclusion and the circular economy.
Degaussing for Magnetic Media
For older magnetic drives or hardware containing highly sensitive data that will not be reused, degaussing offers a fast and permanent solution. A degausser generates a powerful magnetic field that instantly scrambles the data on the magnetic platters of a traditional HDD.
This process is irreversible. The intense magnetic pulse erases the data and destroys the drive's firmware, rendering it completely inoperable. It is an extremely effective method for magnetic storage.
However, it is crucial to understand its limitations. Degaussing is completely ineffective on SSDs. Because SSDs use non-magnetic flash memory, the magnetic field has no effect on the stored data. This distinction is vital for any modern IT fleet.
Physical Shredding: The Ultimate Failsafe
When the risk is too high and absolute certainty is required, physical destruction is the only option. This is the gold standard for secure HDD disposal, offering a 100% guarantee that data can never be recovered. At Reworx Recycling, we use industrial machinery to shred hard drives into small, mangled pieces of metal and plastic.
Shredding is the ideal choice for:
- Drives containing top-secret intellectual property or classified data.
- Damaged, faulty, or failed hardware.
- SSDs that cannot be securely wiped through other methods.
- Organizations in highly regulated industries like healthcare or finance that require the highest level of assurance.
This decision tree helps visualize the process from asset assessment to selecting the appropriate disposal method.
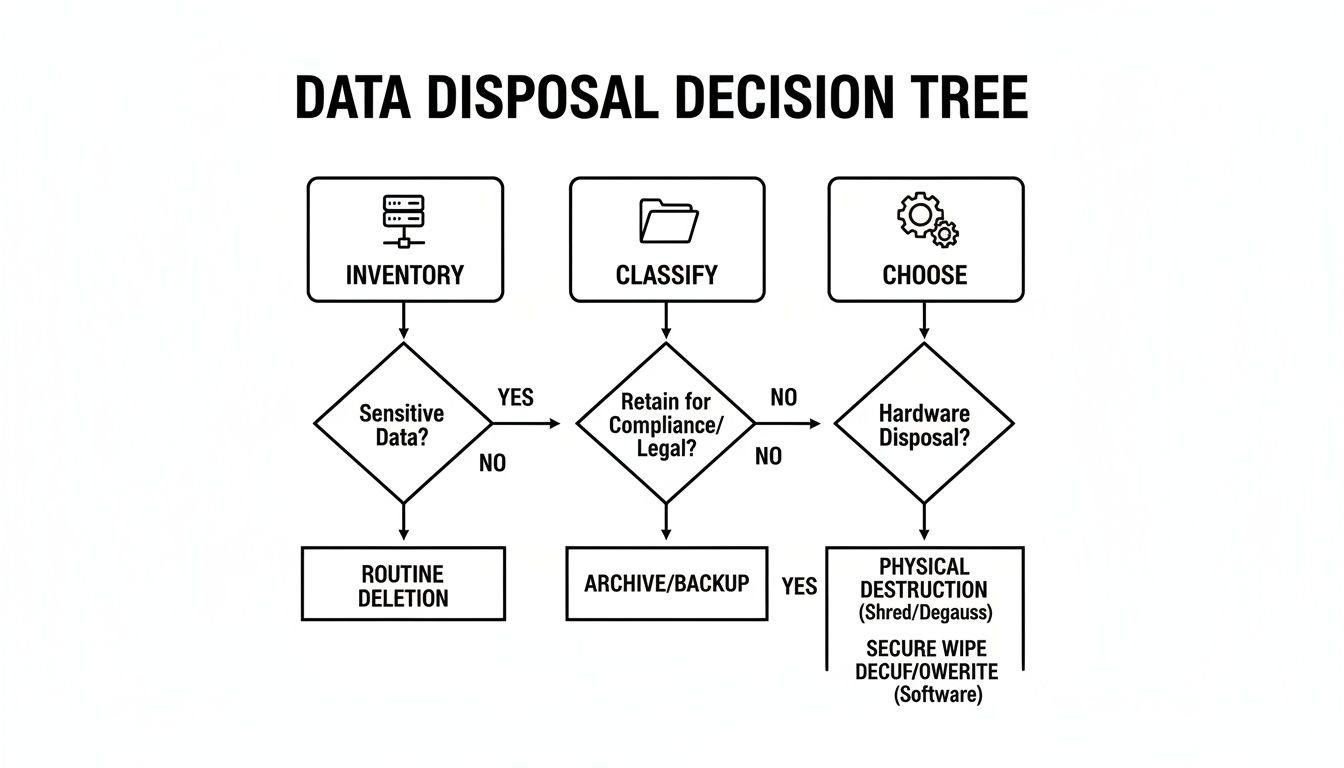
As shown, the process begins with inventory and classification. The type of asset and its data sensitivity then guide you to the most suitable destruction method.
HDD Disposal Method Comparison
This table provides a quick comparison to help you decide which method best fits your needs.
| Method | Description | Best For | Effectiveness (HDD/SSD) | Allows Reuse? |
|---|---|---|---|---|
| Software Wiping | Overwrites all data on the drive with random characters using certified software. | Redeploying, reselling, or donating hardware. Safely wiping functional drives. | HDD: High SSD: High |
Yes |
| Degaussing | Uses a powerful magnetic field to instantly erase data from magnetic media. | Quick, permanent data destruction of HDDs and magnetic tapes that won't be reused. | HDD: High SSD: None |
No |
| Physical Shredding | Industrial machinery grinds drives into small, irrecoverable metal fragments. | Highest security needs, failed/damaged drives, and regulatory compliance. | HDD: Absolute SSD: Absolute |
No |
Ultimately, the best method depends on your specific security needs, compliance obligations, and whether you aim to recover value from the asset through donation or resale.
Mastering Compliance and Chain of Custody
Determining how to destroy a hard drive is only half the battle. The task is not complete until you have the documentation to prove it.
This is where compliance and an airtight chain of custody become critical. This documentation is your shield, protecting your business long after the hardware has been processed.
A secure chain of custody documents the entire lifecycle of your IT assets in chronological order. It meticulously tracks every hard drive from the moment it leaves your facility, through secure transport, to its final, verified destruction. This is a non-negotiable requirement for nearly every data privacy regulation.
Without it, you have a significant gap in your audit trail. It is the final chapter that proves you followed proper procedures, which is essential during a compliance audit or legal inquiry.
The Role of the Certificate of Destruction
The cornerstone of this process is the Certificate of Destruction (CoD). This is not just a receipt; it is a formal, legally binding document that serves as your official proof of secure disposal. It is the final link in the chain and your primary defense against claims of negligence.
For a CoD to be valid, it must include specific, verifiable details:
- Individual Serial Numbers: A complete manifest listing every asset that was destroyed.
- Destruction Method: A clear description of whether drives were wiped, degaussed, or physically shredded, often referencing standards like NIST 800-88.
- Date and Location: The exact time and place where the destruction occurred.
- Transfer of Custody Details: A log of who handled the assets at each stage.
- Authorized Signature: An official sign-off from your certified ITAD partner.
Working with a partner like Reworx Recycling ensures this entire process is handled meticulously. We provide detailed, audit-ready documentation to help you satisfy industry regulations and prove due diligence.
A robust Certificate of Destruction isn't just paperwork—it's your liability shield. It formally transfers the responsibility for the data's secure end from your organization to your certified disposal partner.
A solid understanding of governance, risk, and compliance (GRC) is essential for getting this right. The GRC framework underpins the policies and procedures that make your disposal process legally sound and defensible.
Investing in Verifiable Security
The increasing focus on verifiable proof is evident in the market for secure disposal equipment. The global Hard Disk Destruction Equipment market was valued at USD 1,760 million and is expected to climb to USD 2,559 million by 2032.
A significant driver of this growth is the commercial sector, which accounts for an estimated USD 450 million of the market. This trend indicates a critical shift: companies now view secure, documented disposal not as a cost, but as an essential investment in risk mitigation.
By partnering with a certified ITAD provider like Reworx Recycling, you leverage their expertise and infrastructure, achieving the same high level of security and compliance without the capital expense of in-house equipment.
Finding the Right Partner for Secure and Socially Responsible ITAD
Choosing a partner for your IT asset disposition (ITAD) program is a significant decision that extends beyond simply removing old hardware. True secure hdd disposal requires a partner who not only meets every security and compliance standard but also aligns with your company's core values, turning a routine operational task into a strategic advantage.

The right partner offers a transparent, auditable process that actively protects your brand's reputation. It is a relationship built on trust, verifiable security, and a genuine commitment to responsible practices.
Core Competencies of a Top-Tier ITAD Partner
When vetting potential ITAD vendors, there are several non-negotiable competencies to look for. These pillars ensure your data remains secure and your company stays compliant throughout the process.
A professional ITAD partner will offer a full spectrum of data destruction services, including NIST 800-88 compliant software wiping for asset reuse, powerful degaussing for magnetic media, and industrial-grade shredding for ultimate security. Their ability to match the method to your risk level demonstrates true expertise.
Certifications are equally important. Look for credentials like R2 (Responsible Recycling) or e-Stewards, which prove the vendor adheres to the highest industry standards for environmental protection, data security, and worker safety.
Finally, insist on comprehensive, transparent reporting, including:
- A detailed chain of custody log for every asset.
- Itemized reports with serial numbers.
- Legally defensible Certificates of Destruction.
This documentation is your ultimate defense in an audit, proving your due diligence.
The Social Enterprise Advantage with Reworx Recycling
This is where a partnership can evolve. By moving beyond a simple transactional service, you can create a powerful narrative for your corporate social responsibility (CSR) initiatives. Working with a social enterprise like Reworx Recycling adds a unique and compelling layer of value to your ITAD program by merging best-in-class security with a mission to create positive community impact.
While traditional vendors often focus solely on destruction, our model is built on a "reuse-first" philosophy. For every non-sensitive, functional device you retire, we see an opportunity. Our expert technicians perform certified data wiping to securely sanitize these assets for a second life.
Choosing a social enterprise for ITAD means your retired assets don't just disappear—they become tools for empowerment. It's a direct way to invest in digital inclusion, support education, and foster workforce development in your own community.
These refurbished computers, laptops, and tablets are then donated to local schools, nonprofit organizations, and workforce development programs. This process turns a cost center into a tangible resource that helps bridge the digital divide.
Turning E-Waste Into a Force for Good
The scale of the e-waste problem is staggering. As one of the world's fastest-growing waste streams, the United Nations reported a record 136 billion pounds generated in a single year. An estimated 78% of this e-waste is not formally collected or properly recycled, creating significant environmental and data security risks.
By partnering with Reworx Recycling, you actively counter this trend. Our donation-based model ensures your equipment is handled responsibly while maximizing its social and environmental value. This transforms your secure disposal process into a visible demonstration of your commitment to sustainability and community support. You can learn more about how our model as a premier electronic waste recycling company benefits both businesses and the community.
Instead of just destroying value, you create it. This approach provides a powerful narrative for your sustainability reports, enhances your brand image, and engages employees who are passionate about making a real impact. It’s the ultimate win-win: your data is secure, your compliance is ensured, and your old technology becomes a catalyst for a better future.
Answering Your Top Hard Drive Disposal Questions
When it's time to retire old hard drives, IT managers and business leaders always have a few critical questions. Getting the right answers is the foundation of a secure and compliant IT asset disposition (ITAD) strategy. Let's tackle some of the most common ones we hear.
Is Formatting a Hard Drive Enough to Erase Data?
Absolutely not. This is one of the biggest misconceptions in data security.
Formatting a drive only removes the file system's "table of contents," leaving the actual data intact on the drive's platters. This data can be easily recovered using widely available software.
For data to be truly eradicated, it must be rendered unreadable through one of these methods:
- Certified Data Wiping: Using professional software to overwrite every sector of the drive with random characters, following standards like NIST 800-88.
- Degaussing: Applying a powerful magnetic field to a traditional HDD to completely scramble the magnetic data.
- Physical Shredding: Grinding the drive into tiny, irrecoverable fragments.
Simply formatting a drive is a risk no business can afford to take.
What Is a Certificate of Destruction and Why Is It Important?
A Certificate of Destruction (CoD) is your legal proof and official audit trail, demonstrating that your company's data-bearing devices were destroyed securely and permanently. Your ITAD partner provides this document to confirm you have met your due diligence and complied with data privacy laws like HIPAA, GDPR, or CCPA.
A legitimate CoD is a detailed record that includes:
- Unique serial numbers for every destroyed device.
- The exact method of destruction used (e.g., shredding, degaussing).
- The date and location of the destruction.
- A formal statement transferring custody and liability.
A Certificate of Destruction is your number one defense in a compliance audit. It officially shifts the liability for the data's secure end-of-life from your organization to a certified vendor like Reworx Recycling, giving you verifiable peace of mind.
Can You Degauss Solid State Drives (SSDs)?
No, and this is a critical detail. Degaussing is 100% ineffective on SSDs.
Degaussing works by disrupting the magnetic field on the platters of a traditional Hard Disk Drive (HDD). SSDs use non-magnetic flash memory chips for storage. Applying a degausser's magnetic field to an SSD will do absolutely nothing to the data it contains.
For SSDs, the only truly secure methods to eradicate data are cryptographic erasure (if supported by the drive) or complete physical destruction via industrial shredding.
What Is the Difference Between On-Site and Off-Site Shredding?
The main difference is the location of destruction and your visibility into the chain of custody. Both are highly secure options when managed by a certified partner.
On-Site Shredding
A mobile destruction truck comes directly to your facility. Your team can witness the hard drives being physically shredded on the spot, providing complete transparency and a chain of custody that never leaves your premises. This is the preferred method for organizations with the strictest security protocols.
Off-Site Shredding
Your hard drives are collected at your location in locked, tamper-evident containers. A GPS-tracked vehicle transports them to a secure, certified destruction facility. While you don't witness the shredding firsthand, a trusted partner like Reworx Recycling maintains a strict chain of custody throughout the process. You receive a full report and a Certificate of Destruction upon completion. This option is often more cost-effective, especially for larger quantities.
Ready to build a disposal strategy that is secure, compliant, and socially responsible? Partner with Reworx Recycling to turn your retired IT assets into a positive community impact while ensuring your data is completely protected. Schedule a pickup or contact us today to learn more about our corporate donation programs.
Explore our blog to learn more about our corporate donation programs and secure disposal services.